KEEP IN TOUCH
Subscribe to our mailing list to get free tips on Data Protection and Cybersecurity updates weekly!







A security researcher was able to add a counterfeit test package to the official list of Microsoft Azure SDK latest releases.
The simple trick if abused by an attacker can give off the impression that their malicious package is part of the Azure SDK suite.
This month security researcher Alex Birsan
demonstrated how anyone could add their own package to the list of official Azure SDK Latest Releases.
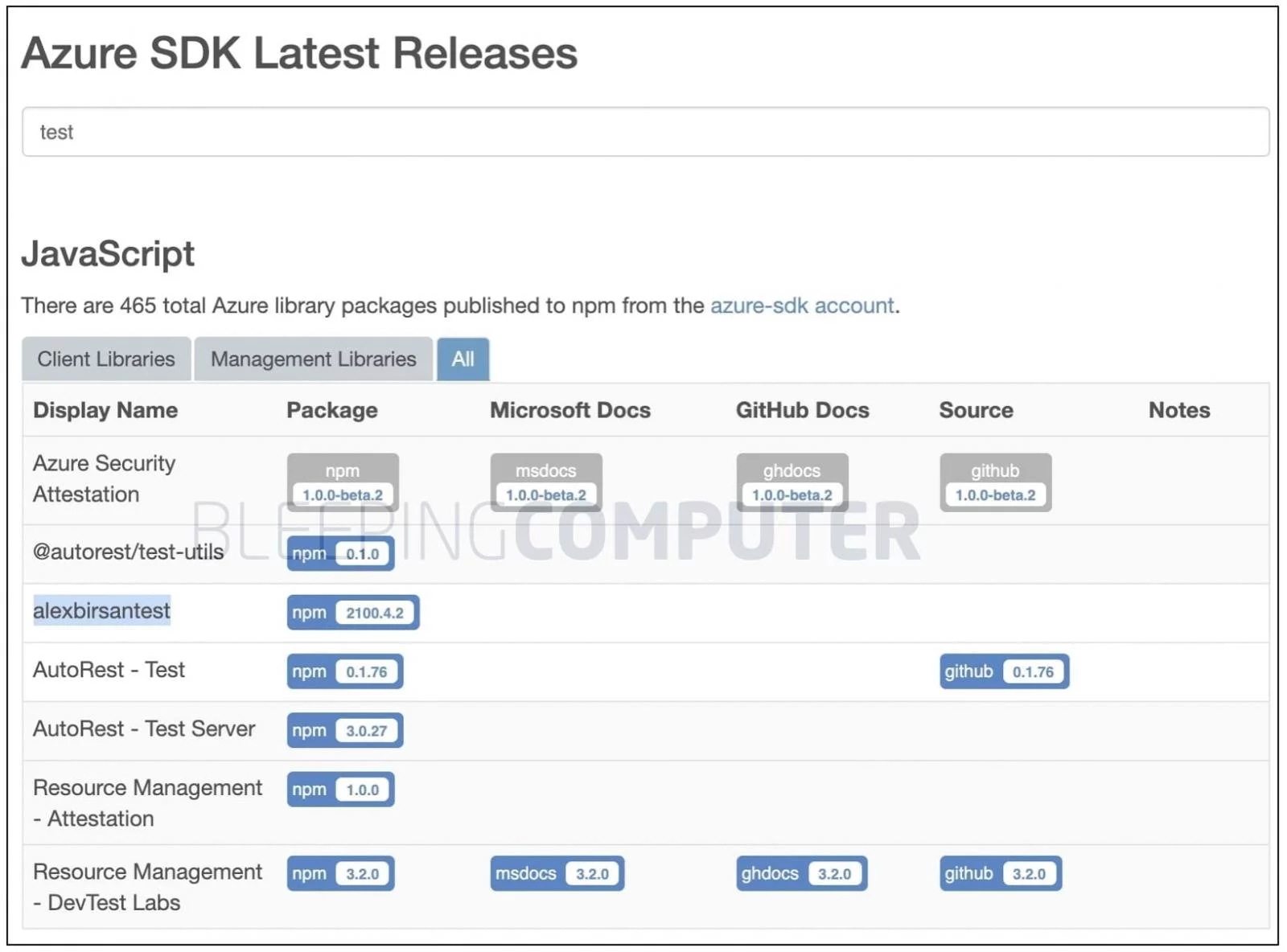
As of a few days ago, the Azure SDK releases page showed the authentic Microsoft Azure SDK releases alongside the mysterious package alexbirsantest.
Also Read: Key PDPA Amendments 2019/2020 You Should Know
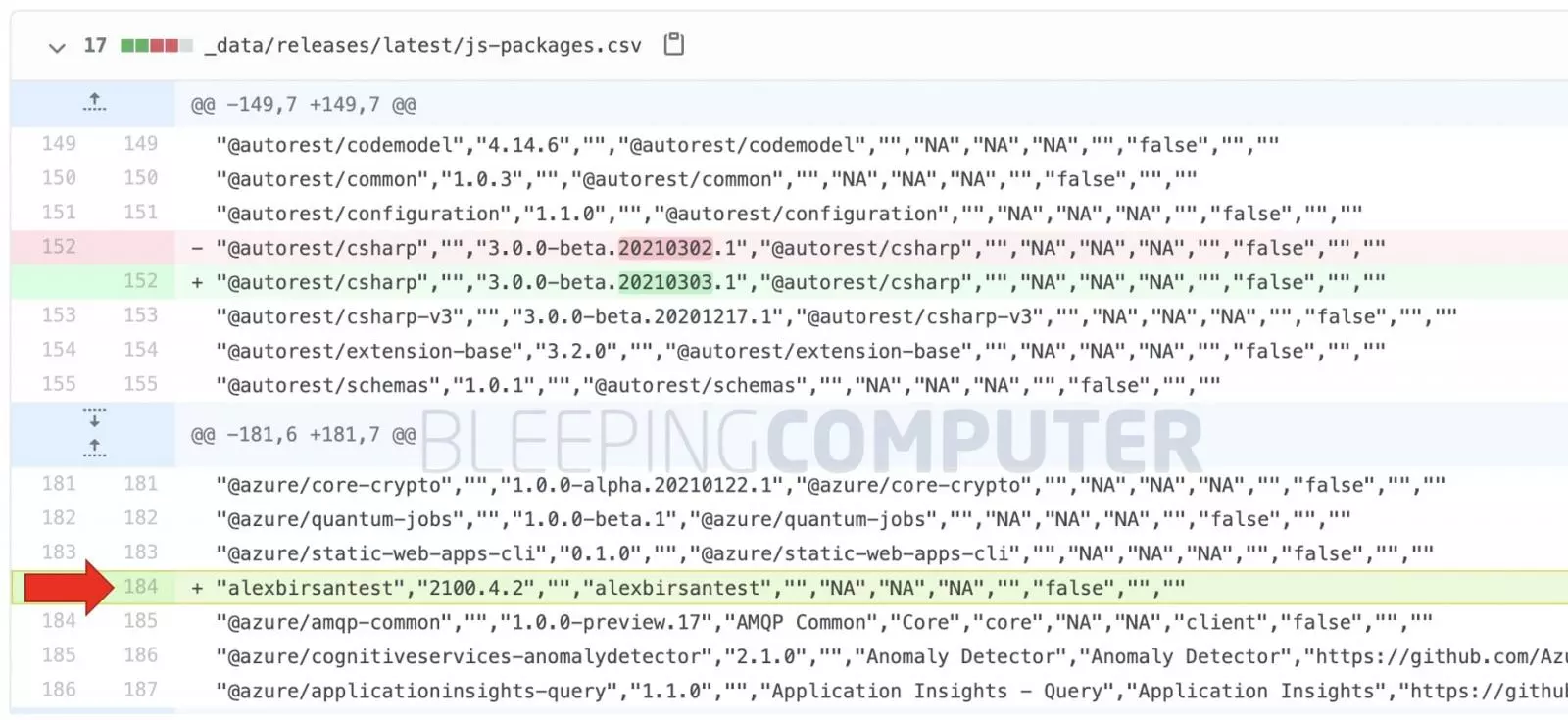
Additionally, one of the users pointed out that a GitHub commit was pushed by the “azure-sdk” bot and added the alexbirsantest package to the CSV file supposedly used for populating the Microsoft Azure SDK releases page.
This indicated the bot was somehow tricked into picking up this unofficial test package automatically.
Last month, as first reported by BleepingComputer, Alex Birsan could exploit the dependency confusion problem in the open-source ecosystem to ethically hack over 35 big tech firms in a novel supply chain attack, and earn over $130,000 in bug bounties.
However, the researcher has clarified this is not the result of dependency confusion but rather something much simpler.
The researcher published the alexbirsantest package to npm and further added the npm account azure-sdk as a collaborator to his package, by following simple instructions laid out by npm.
In this particular case, the “azure-sdk” accounts used on npm and GitHub appear to be bots configured to pick up any and all npm packages that these accounts were listed as collaborators for.
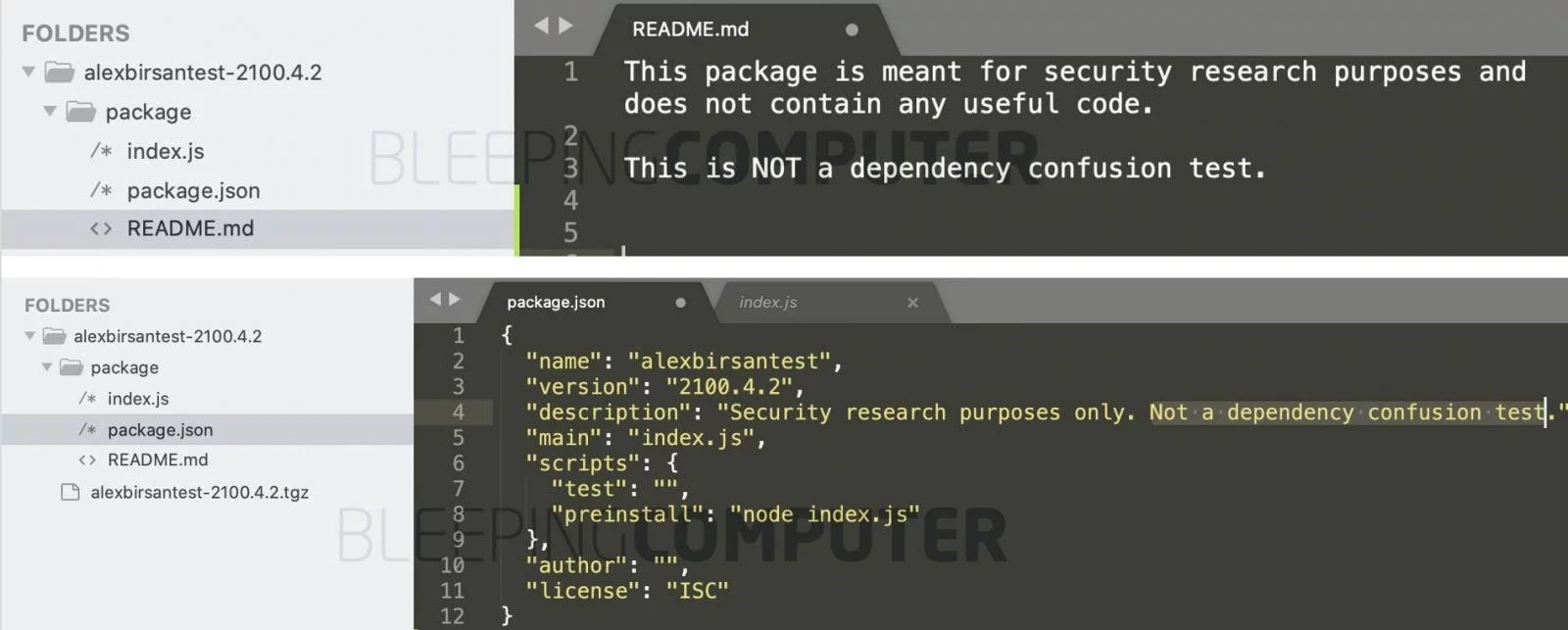
Although alexbirsantest has since been taken down, as a Sonatype security researcher, I was able to obtain a copy of the original npm package from Sonatype’s automated malware detection system archives.
The index.js file in alexbirsantest version 2100.4.2 contains the same proof-of-concept code as Birsan’s previously published dependency confusion packages, but the package has a disclaimer in multiple places clarifying that this is “NOT a dependency confusion test.”
“I just added a bunch of companies as collaborators to my package to see what would happen. This was the only interesting result,” Birsan told BleepingComputer.
Even though this event may not have a direct impact on compromising a system’s security, it is still noteworthy.
An adversary being able to add a malicious package with a name similar to other Azure SDK packages can easily disguise their malware as a part of the official Azure SDK releases.
Also Read: The 5 Benefits Of Outsourcing Data Protection Officer Service
If downloaded by an unsuspecting developer or user, this could potentially become the root cause of a software supply chain attack.
After all, the page explicitly says that it contains “Azure library packages published to npm from the azure-sdk account.“
As seen by BleepingComputer, Microsoft has now removed the alexbirsantest package from the list of their official Azure SDK latest releases.
BleepingComputer has reached out to Microsoft for comment before publishing this article and we are awaiting their response.