KEEP IN TOUCH
Subscribe to our mailing list to get free tips on Data Protection and Cybersecurity updates weekly!






Microsoft warns of an ongoing series of attacks compromising Kubernetes clusters running Kubeflow machine learning (ML) instances to deploy malicious containers that mine for Monero and Ethereum cryptocurrency.
The attacks had started towards the end of May when Microsoft security researchers observed a sudden increase in TensorFlow machine learning pod deployments.
“The burst of deployments on the various clusters was simultaneous,” said Microsoft Senior Security Researcher Yossi Weizman.
“This indicates that the attackers scanned those clusters in advance and maintained a list of potential targets, which were later attacked on the same time.”
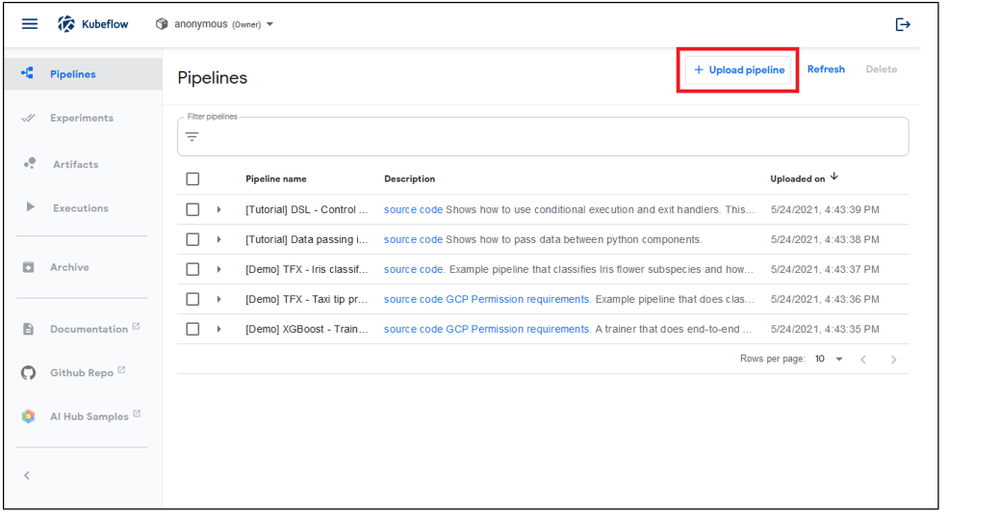
While the pods were legitimate from the official Docker Hub repository, the attackers modified them to mine for cryptocurrency on compromised Kubernetes clusters by deploying ML pipelines using the Kubeflow Pipelines platform.
To gain initial access to the clusters and deploy the cryptocurrency miners, the attackers use Internet-exposed Kubeflow dashboards, which should only be open to local access.
The threat actors deploy at least two separate pods on each of the hacked clusters: one for CPU mining and one for GPU mining.
Also Read: 3 Reasons Why You Must Take a PDPA Singapore Course
XMRig is used to mine Monero using the CPU, while Ethminer is installed to mine Ethereum on the GPU.
The malicious pods used in this active campaign are named using the sequential-pipeline-{random pattern} pattern.
“The attack is still active, and new Kubernetes clusters that run Kubeflow get compromised,” Weizman warned.
This campaign follows a similar campaign from April 2020, which also abused powerful Kubernetes clusters as part of a large-scale cryptomining campaign.
Unlike this campaign, when the attackers used Kubeflow Pipelines to deploy ML pipelines, the April 2020 attacks abused Jupyter notebooks.
Even though Microsoft detected several other campaigns targeting Kubernetes clusters in the past exploiting Internet-exposed services, the April 2020 campaign was the first time an attack specifically targeted Kubeflow environments.
Admins are advised to always enable authentication on Kubeflow dashboards if exposing them to the Internet cannot be avoided and monitor their environments (containers, images, and the processes they run).
In related news, Unit 42 researchers also shared info on Siloscape, the first-ever malware to target Windows containers, with the end goal of compromising and backdooring Kubernetes clusters.
Unlike other malware that targets cloud environments that mainly focus on cryptojacking, Siloscape exposes the compromised infrastructure to a broader range of malicious pursuits.
Also Read: The Difference Between GDPR and PDPA Under 10 Key Issues
These include ransomware attacks, credential theft, data exfiltration, and even highly disastrous supply chain attacks.