KEEP IN TOUCH
Subscribe to our mailing list to get free tips on Data Protection and Cybersecurity updates weekly!





Microsoft announced today that Microsoft Defender for Endpoint’s detection and response (EDR) capabilities are now generally available on Linux servers.
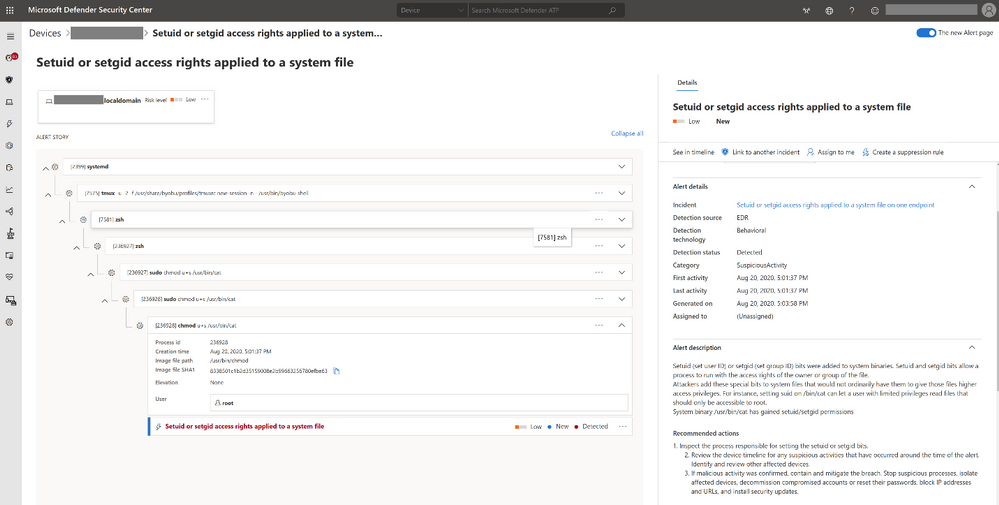
EDR capabilities allow admins and security teams to spot attacks targeting or involving Linux servers in their environments almost in real-time with the help of alerts automatically aggregated as incidents based on attacker techniques and attribution.
This adds to the already existing preventative antivirus capabilities and the centralized reporting features available to admins via the Microsoft Defender Security Center.
Microsoft Defender for Endpoint (Linux) was first showcased during the Ignite 2019 conference, entered public preview in February 2020, and it was made generally available in June 2020. EDR capabilities were released in public preview in November 2020.
Right now, the full set of EDR capabilities are available on Linux Server distributions supported by Microsoft Defender for Endpoint (Linux), including RHEL 7.2+, CentOS Linux 7.2+, Ubuntu 16 LTS or higher LTS, SLES 12+, Debian 9+, and Oracle Linux 7.2.
Also Read: Data Centre Regulations Singapore: Does It Help To Progress?
Microsoft Defender for Endpoint (Linux) EDR capabilities provide admins with:
On Linux endpoints, it comes in the form of a command-line product that sends all detected threats to the Microsoft Defender Security Center.
Admins can deploy and configure it on enterprise Linux devices using Ansible or Puppet, as well as with the help of any other Linux configuration management tool.
To be able to deploy Microsoft Defender for Endpoint (Linux) you need a Servers license (more info can be found in the product terms).
If you’re already evaluating the public preview version of EDR capabilities, you have to update the agent to version 101.18.53 or higher.
“If you are already running Microsoft Defender for Endpoint (Linux) preventive AV in production, your devices will seamlessly receive the new EDR capability as soon as you update the agent to version 101.18.53 or higher,” Microsoft Senior Product Manager Tomer Hevlin said.
Detailed information on how to install, configure, and update Microsoft Defender for Endpoint for Linux is available here.
Also Read: What Is A Governance Framework? The Importance And How It Works