KEEP IN TOUCH
Subscribe to our mailing list to get free tips on Data Protection and Cybersecurity updates weekly!






The recently patched vulnerabilities in Microsoft Exchange have sparked new interest among cybercriminals, who increased the volume of attacks focusing on this particular vector.
While ransomware attacks have increased in frequency in the past six months, cybersecurity company Check Point last week noticed a surge in incidents targeting Microsoft Exchange servers vulnerable to the so-called ProxyLogon critical bugs.
Even with patching moving at a rapid pace, the company saw attempted attacks triple across the globe, counting tens of thousands.
According to Microsoft, there were about 82,000 vulnerable Exchange servers on March 14. About a week later, the number dropped considerably to roughly 30,000 exposed machines, as per data from RiskIQ.
Telemetry data from Check Point last week showed more than 50,000 attack attempts globally, most of them aimed at organizations in the government/military, manufacturing, and banking/finance sectors.
Almost half of the exploit attempts occurred in the U.S. (49%), by far the most appealing region compared to other countries where Check Point recorded far fewer incidents (UK – 5%, Netherlands and Germany – both 4%).
Also Read: What Does A Data Protection Officer Do? 5 Main Things
The company saw a 57% rise in ransomware attacks over the past six months at a global level. More worrisome is a constant monthly increase of 9% since the beginning of the year.
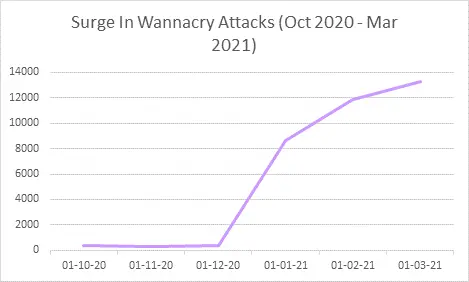
Aside from the normal ransomware strains observed (Maze, Ryuk, REvil), the company notes a 53% swell in the number of organizations affected by the wormable WannaCry ransomware.
“In fact, CPR found that there are 40 times more affected organizations in March 2021 when compared to October 2020. The new samples still use the EternalBlue exploit to propagate – for which patches have been available for over 4 years“ – Check Point
Almost four years ago, the WannaCry outbreak propagated through NSA’s EternalBlue for Windows Server Message Block (SMB), causing hundreds of millions of USD in damages in just a few days.
Its spread was contained after security researcher Marcus Hutchins discovered a kill switch and Microsoft released patches. Over 200,000 computers were affected by the attacks.
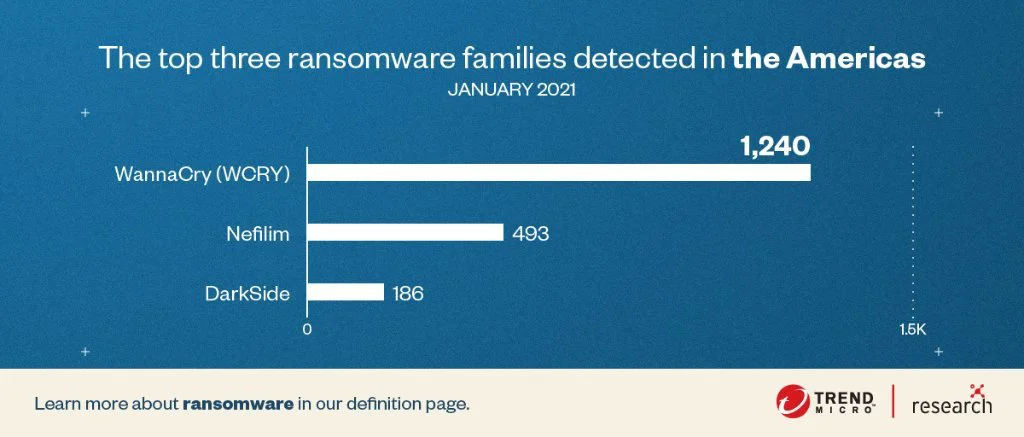
The malware has not been eradicated, though. Security firms continue to detect WannaCry even these days. In January, it was TrendMicro’s top ransomware detection.
The reason behind the high numbers is WannaCry being wormable and thousands of systems still vulnerable to EternalBlue that are reachable over the public internet.
Check Point observed the same trend starting in December 2020, with attacks continuing to increase well over 12,000 in March 2021.
Also Read: The DNC Registry Singapore: 5 Things You Must Know
The figures show the importance of patching on time, else organizations remain vulnerable to attack vectors that should be mostly extinct.