KEEP IN TOUCH
Subscribe to our mailing list to get free tips on Data Protection and Cybersecurity updates weekly!







Microsoft has now confirmed signing a malicious driver being distributed within gaming environments.
This driver, called “Netfilter,” is in fact a rootkit that was observed communicating with Chinese command-and-control (C2) IPs.
G Data malware analyst Karsten Hahn first took notice of this event last week and was joined by the wider infosec. community in tracing and analyzing the malicious drivers bearing the seal of Microsoft.
This incident has once again exposed threats to software supply-chain security, except this time it stemmed from a weakness in Microsoft’s code-signing process.
Last week, G Data’s cybersecurity alert systems flagged what appeared to be a false positive, but was not—a Microsoft signed driver called “Netfilter.”
The driver in question was seen communicating with China-based C&C IPs providing no legitimate functionality and as such raised suspicions.
This is when G Data’s malware analyst Karsten Hahn shared this publicly and simultaneously contacted Microsoft:
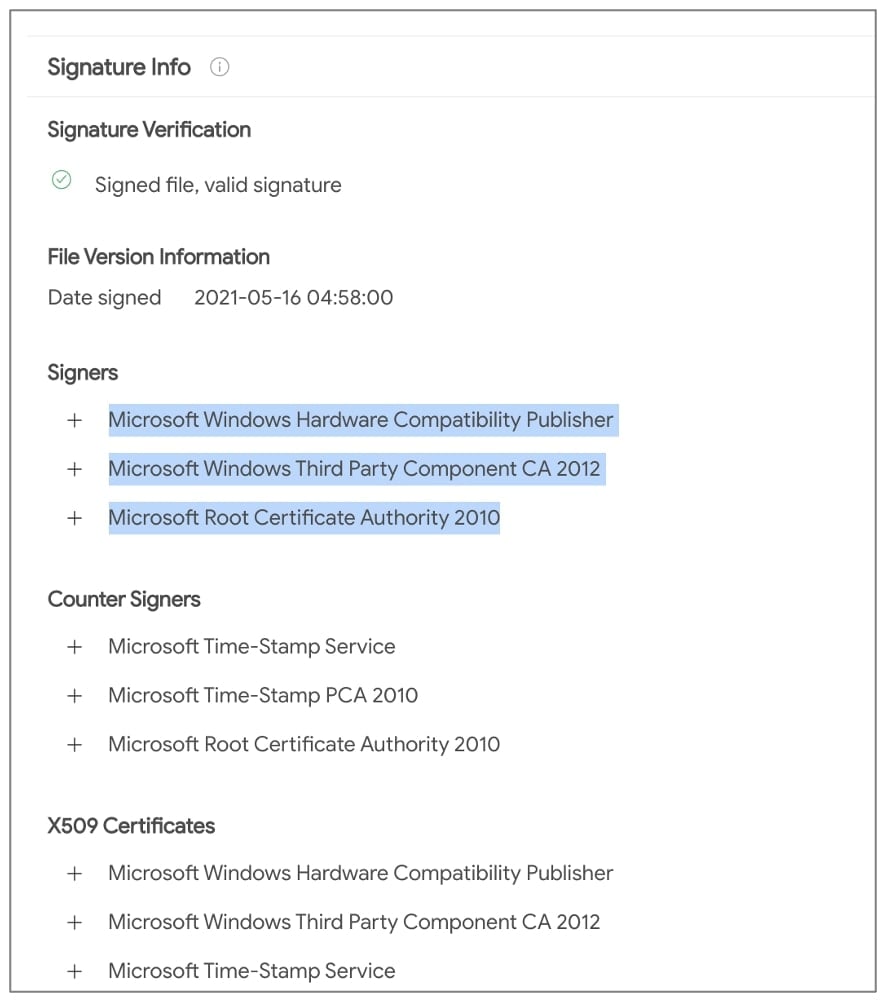
“Since Windows Vista, any code that runs in kernel mode is required to be tested and signed before public release to ensure stability for the operating system.”
“Drivers without a Microsoft certificate cannot be installed by default,” states Hahn.
At the time, BleepingComputer began observing the behavior of C2 URLs and also contacted Microsoft for a statement.
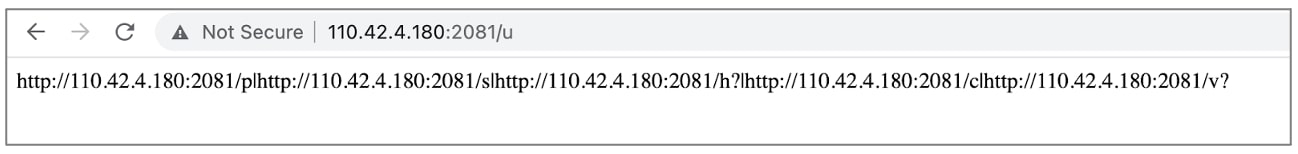
The first C2 URL returns a set of more routes (URLs) separated by the pipe (“|”) symbol:
Also Read: The DNC Singapore: Looking at 2 Sides Better
Each of these serves a purpose, according to Hahn:
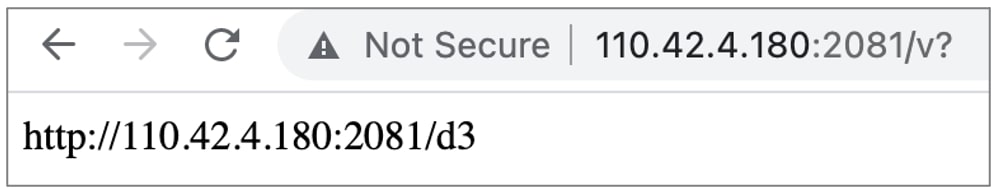
As seen by BleepingComputer, for example, the “/v?” path provided URL to the malicious Netfilter driver in question itself (living at “/d3”):
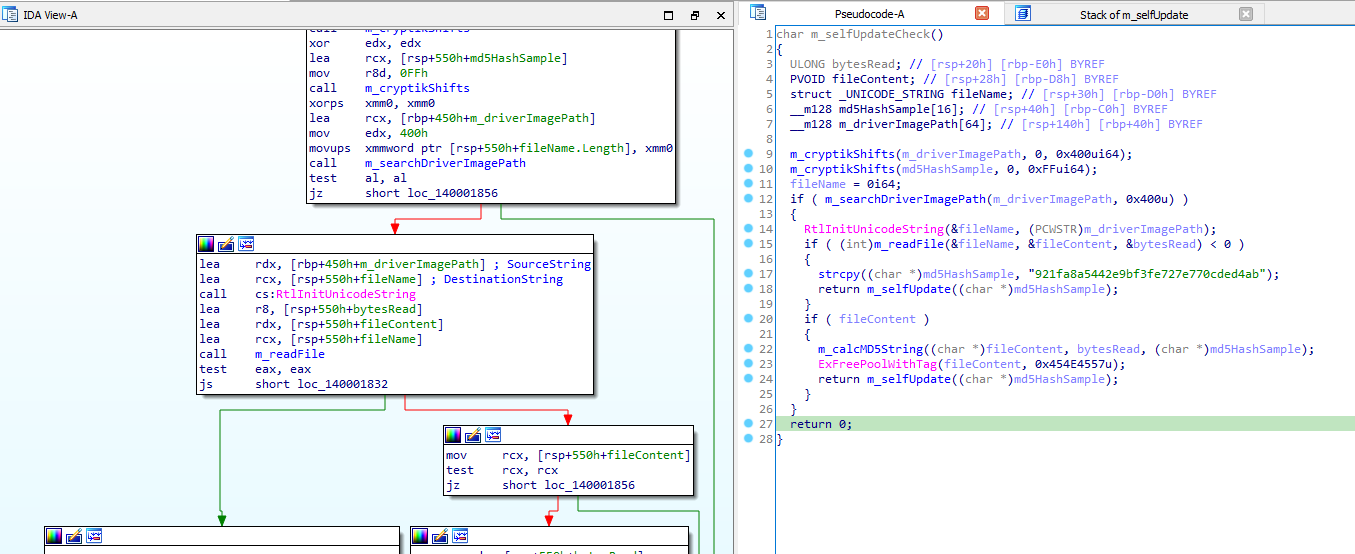
The G Data researcher spent some time sufficiently analyzing the driver and concluded it to be malware.
The researcher has analyzed the driver, its self-update functionality, and Indicators of Compromise (IOCs) in a detailed blog post.
“The sample has a self-update routine that sends its own MD5 hash to the server via hxxp://110.42.4.180:2081/v?v=6&m=,” says Hahn.
An example request would look like this:hxxp://110.42.4.180:2081/v?v=6&m=921fa8a5442e9bf3fe727e770cded4ab
“The server then responds with the URL for the latest sample, e.g. hxxp://110.42.4.180:2081/d6 or with ‘OK’ if the sample is up-to-date. The malware replaces its own file accordingly,” further explained the researcher.
During the course of his analysis, Hahn was joined by other malware researchers including Johann Aydinbas, Takahiro Haruyama, and Florian Roth.
Roth was able to gather the list of samples in a spreadsheet and has provided YARA rules for detecting these in your network environments.
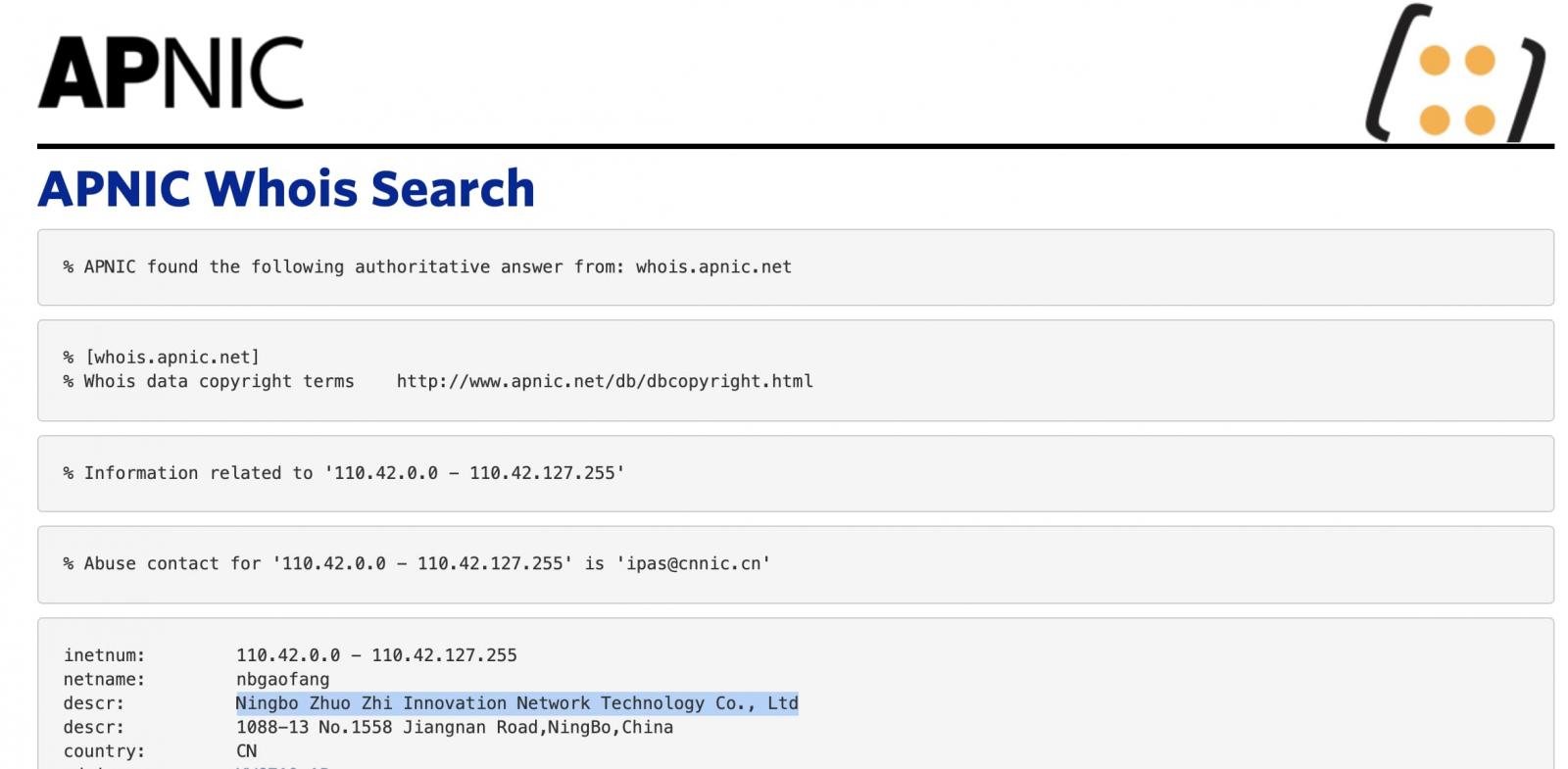
Notably, the C2 IP 110.42.4.180 that the malicious Netfilter driver connects to belonged to Ningbo Zhuo Zhi Innovation Network Technology Co., Ltd, according to WHOIS records:
Another researcher @cowonaut alleged that the aforementioned company has previously been marked by the U.S. Department of Defense (DoD) as a “Communist Chinese military” company.
However, BleepingComputer did not see Ningbo Zhuo Zhi Innovation Network Technology Co., Ltd. present on any of the DoD lists available, and has reached out to the G Data researcher for clarification.
Also Read: 4 Best Practices on How to Use SkillsFuture Credit
Microsoft is actively investigating this incident, although thus far, there is no evidence that stolen code-signing certificates were used.
The mishap seems to have resulted from the threat actor following Microsoft’s process to submit the malicious Netfilter drivers, and managing to acquire the Microsoft-signed binary in a legitimate manner:
“Microsoft is investigating a malicious actor distributing malicious drivers within gaming environments.”
“The actor submitted drivers for certification through the Windows Hardware Compatibility Program. The drivers were built by a third party.”
“We have suspended the account and reviewed their submissions for additional signs of malware,” said Microsoft yesterday.
According to Microsoft, the threat actor has mainly targeted the gaming sector specifically in China with these malicious drivers, and there is no indication of enterprise environments having been affected so far.
Microsoft has refrained from attributing this incident to nation-state actors just yet.
Falsely signed binaries can be abused by sophisticated threat actors to facilitate large-scale software supply-chain attacks.
The multifaceted Stuxnet attack that targeted Iran’s nuclear program marks a well-known incident in which code-signing certificates were stolen from Realtek and JMicron to facilitate the attack.
This particular incident, however, has exposed weaknesses in a legitimate code-signing process, exploited by threat actors to acquire Microsoft-signed code without compromising any certificates.
Update 12:26 PM ET: Clarified that BleepingComputer did not see the DoD list explicitly mentioning the alleged Chinese company, contrary to the details in the researcher’s report. Also reached out to Hahn for clarification.