





Google’s Threat Analysis Group has exposed the operations of a threat actor group dubbed “EXOTIC LILY,” an initial access broker linked to the Conti and Diavol ransomware operations.
This particular group was first spotted exploiting a zero-day vulnerability in Microsoft MSHTML (CVE-2021-40444), so it sparked the interest of Google researchers as a potentially sophisticated threat actor.
After further investigation, it was determined that “EXOTIC LILY” is an initial access broker that uses large-scale phishing campaigns to breach targeted corporate networks and then sells access to those networks to ransomware gangs.
At its peak, EXOTIC LILY was sending more than 5,000 emails to 650 organizations in a single day, showing the extensive nature of the phishing campaigns.
Also Read: Exploring MAS’ framework for equitable sharing of scam losses
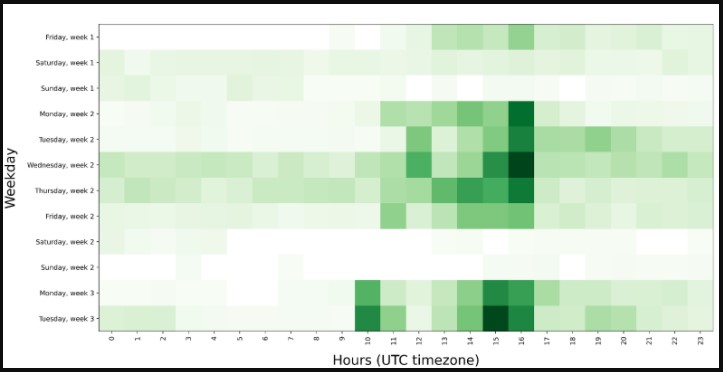
After analyzing the hacking group’s activity, TAG found that the threat actors work primarily from 09:00 AM to 05:00 PM EST during weekdays and log very little activity during the weekends.
While it may be strange to think of cybercriminals working a regular 9-to-5 job, the recent Conti Leaks show that many threat actors run their operations like a business, requesting days off, reporting to managers, and receiving salaries.
Additionally, the group members perform backend technical tasks such as customizing business proposal templates or uploading malware payloads to legitimate file-sharing services before sharing links with targets.
From an operational perspective, the attack chain follows a strict form, starting with registering a spoofed domain, then using it to send emails, build a relationship with the target, and finally share a payload via a file-hosting service.
.jpg)
The domains used are identical to the actual domain name of the spoofed organization but are registered on different TLDs such as “.us,” “.co,” or “.biz.”
The actors source the targets’ email addresses through open-source intelligence or use the website’s contact form to send a fake proposal.
EXOTIC LILY operators even create fake social media accounts on LinkedIn, claiming they work on the spoofed organization, using AI-generated or straight-out stolen images from actual employee.
Also Read: Protecting your business against cyberattacks: a practical guide
This is all to complete the false image of legitimacy while keeping initial communications strictly around discussing the proposal’s design or service requirements.
Once the victim lowers their guard, Google TAG says the attacker shares a download link via TransferNow, TransferXL, WeTransfer, or OneDrive, which leads to the downloading of BazarLoader malware.
These same file-sharing services were used in a similar BazarLoader phishing campaign disclosed last week by Abnormal Security.
.jpg)
When first spotted, the group’s malware came in the form of a document file that attempted to exploit the CVE-2021-40444 vulnerability. Later, the threat actor changed the delivery form to ISO archives containing BazarLoader DLLs and LNK shortcuts.
Google’s analysts have found signs of customization in these samples, but this may have been done by other actors who supplied the malware to EXOTIC LILY.
This month, the group continued using ISO files but now incorporated a DLL containing a custom loader, an advanced variant of the first-stage loader used previously.
That loader drops a malware strain called “Bumblebee”, which users WMI to gather system information and exfiltrate everything to the C2.
Bumblebee can also receive commands from the remote actors and download and run additional payloads. At this time, the files fetched are Cobalt Strike.
While the activities of EXOTIC LILY overlap with Conti’s own operations, Google’s threat analysts believe it’s a distinct threat actor focusing entirely on the establishment of initial network access.
“While the nature of those relationships (with other groups) remains unclear, EXOTIC LILY seems to operate as a separate entity, focusing on acquiring initial access through email campaigns, with follow-up activities that include deployment of Conti and Diavol ransomware, which are performed by a different set of actors,” details Google’s report.
It is worth noting that the recent leak of Conti’s internal messages reflects a thriving crime syndicate with dedicated departments having distinctive roles and central coordination.
Furthermore, the Conti/Ryuk operation has always had strong links to the TrickBot group and their malware operations, namely Diavol, TrickBot, BazarBackdoor, and Anchor.
Recently, researchers discovered that the Conti ransomware operation had taken control over the development of TrickBot’s malware families, which is supported by conversations between Conti managers exposed in the Conti leaks.
As such, it wouldn’t be surprising if Conti had its own internal teams that focused on high-level spear phishing and initial network access that deployed these infections.
However, Google TAG told BleepingComputer that while it’s possible that the spamming operation is conducted by the Conti operation themselves, the lack of conversation regarding spamming in the Conti leaks indicates it’s an external group.
“In the Conti leaks, Conti members mention “spammers” as someone who they work with (e.g. provide custom-built “crypted” malware samples, etc.) through outsourcing,” Google TAG told BleepingComputer in response to our questions.
“However most of the “spammers” don’t seem to be present (or actively communicate) in the chat, hence leading to a conclusion they’re operating as a separate entity.”
Update 3/17/22: Added responses from Google TAG.