KEEP IN TOUCH
Subscribe to our mailing list to get free tips on Data Protection and Cybersecurity updates weekly!







Google Chrome is getting a new feature that increases security when clicking on web page links that open URLs in a new window or tab.
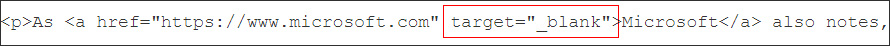
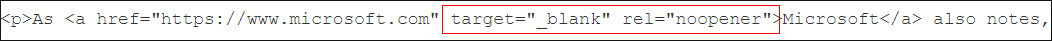
When inserting links into an HTML page, authors can include the target="_blank" attribute that tells the browser to open the link in a new tab when clicked.
However, this attribute has a known security issue that allows the newly opened page to utilize javascript to redirect the original page to a different URL. This redirected URL can be anything the threat actor wants, including phishing pages or pages that automatically download malicious files.
For example, suppose we link to another site in our article and use the target=”_blank” attribute. In that case, the new page can use JavaScript to redirect our article to a phishing page asking for BleepingComputer credentials.
To prevent this from happening, a rel=”noopener” HTML link attribute was created that prevents a new tab from using JavaScript to redirect the page.
In 2018, to increase security, Apple made a change in Safari that treats all HTML links that utilize target=”_blank” to also automatically imply the noopener attribute. With this feature enabled, even if a web site does not use rel=”nooopener” on their URLs, the browser will still secure them.
Last week, Microsoft Edge developer Eric Lawrence added this same feature to Chromium, which means it will also be brought to Microsoft Edge, Google Chrome, Brave, and other Chromium-based browsers.
Also Read: The Importance Of DPIA And Its 3 Types Of Processing
“To mitigate “tab-napping” attacks, in which a new tab/window opened by a victim context may navigate that opener context, the HTML standard changed to specify that anchors that target _blank should behave as if |rel=”noopener”| is set. A page wishing to opt out of this behavior may set |rel=”opener”|,” Lawrence stated in a commit to the Chromium browser.
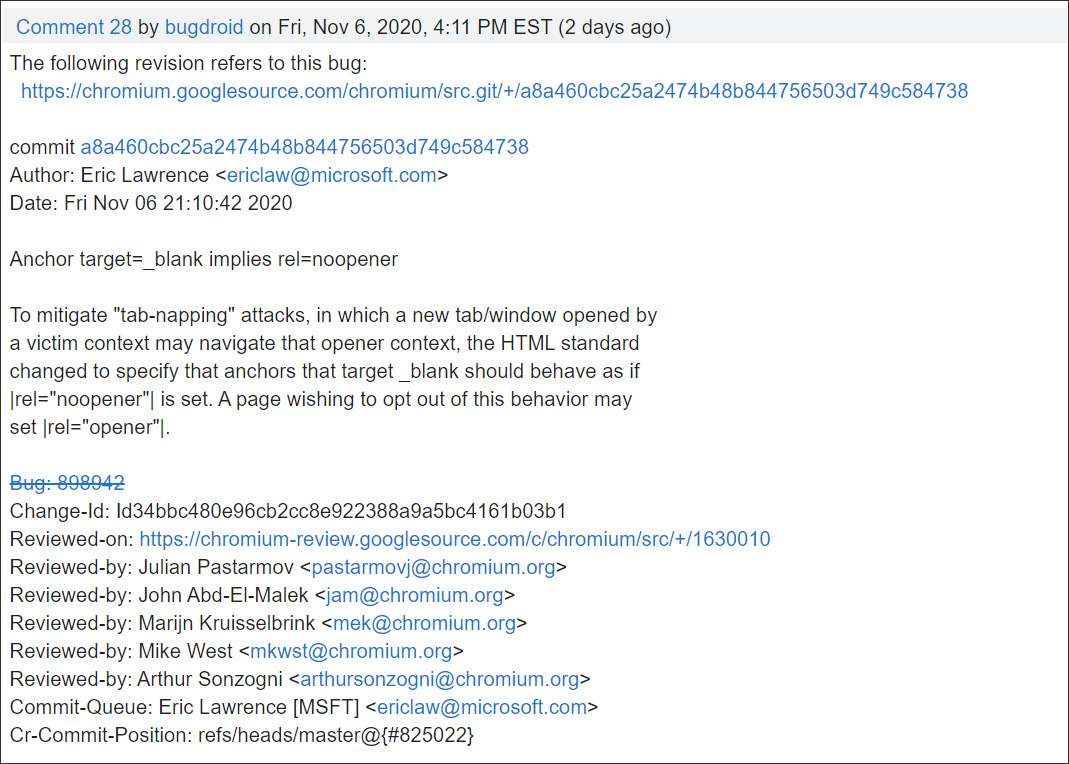
This feature is currently enabled in Chrome Canary and is expected to be released with Chrome 88 in January 2021.
Also Read: Data Storage Security Standards: What Storage Professionals Need To Know