KEEP IN TOUCH
Subscribe to our mailing list to get free tips on Data Protection and Cybersecurity updates weekly!







Chromium-based browsers such as Microsoft Edge and Google Chrome will soon support the Intel CET security feature to prevent a wide range of vulnerabilities.
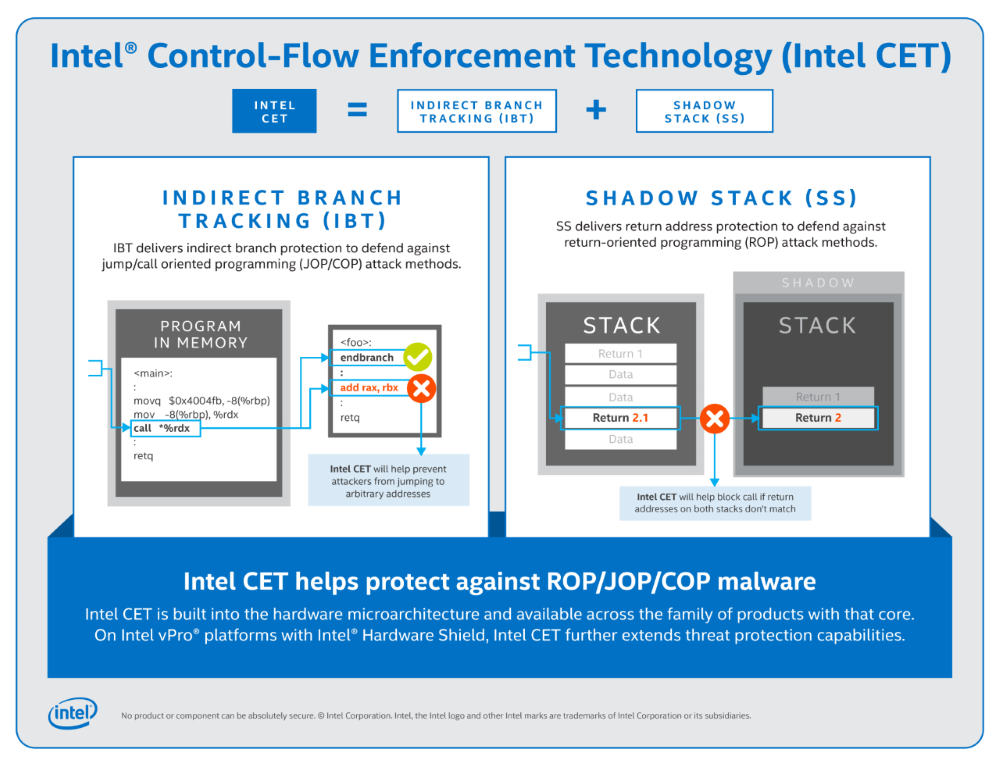
Intel’s Control-flow Enforcement Technology (CET) is a hardware security feature initially introduced in 2016 and added to Intel’s 11th generation CPUs in 2020.
The CET feature is designed to protect programs from Return Oriented Programming (ROP) and Jump Oriented Programming (JOP) attacks that modify an application’s normal flow so that an attacker’s malicious code is executed instead.
“JOP or ROP attacks can be particularly hard to detect or prevent because the attacker uses existing code running from executable memory in a creative way to change program behavior,” explains Microsoft’s Baiju V Patel.
These vulnerabilities include attacks that bypass a browser’s sandbox or perform remote code execution while visiting web sites.
Intel CET is a hardware-based solution that blocks these attempts by triggering exceptions when the natural flow is modified.
Also Read: How To Prevent WhatsApp Hack: 7 Best Practices
Windows 10 supports Intel CET through an implementation called Hardware-enforced Stack Protection.
For Windows applications to support this feature, they must first be compiled with the /CETCOMPAT linker flag in Visual Studio. When compiled with this flag, a program will be marked as CET Shadow Stack-compatible and opted into the security protection.
This week, Microsoft Edge vulnerability research lead Johnathan Norman tweeted that Microsoft Edge 90 would support the Intel CET feature in non-renderer processes.
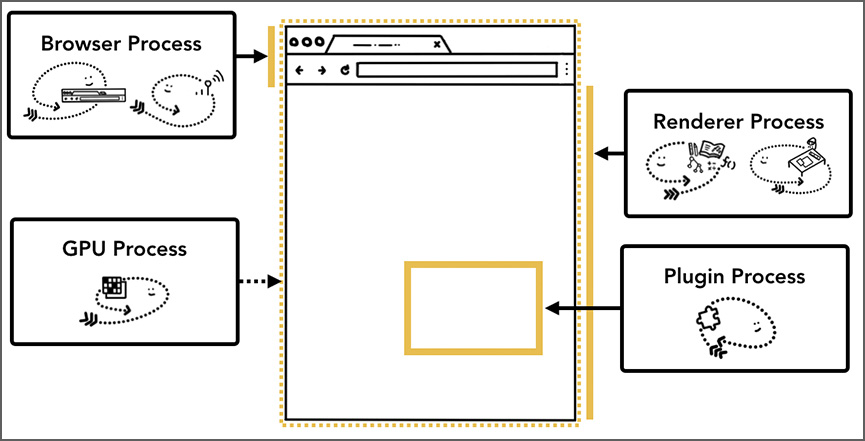
Microsoft Edge, which is based on Chromium, utilizes multiple processes to perform various tasks.
Based on Norman’s tweet, Intel CET will be utilized by the non-renderer processes, such as the browser, GPU, utility, extension, and plugin processes.
This security feature does not appear to be specific to Microsoft Edge but is coming to all Chromium browsers, including Google Chrome, Brave, and Opera.
Mozilla is also looking into adding support for Intel CET in Firefox, but there has been no recent status update for their implementation.
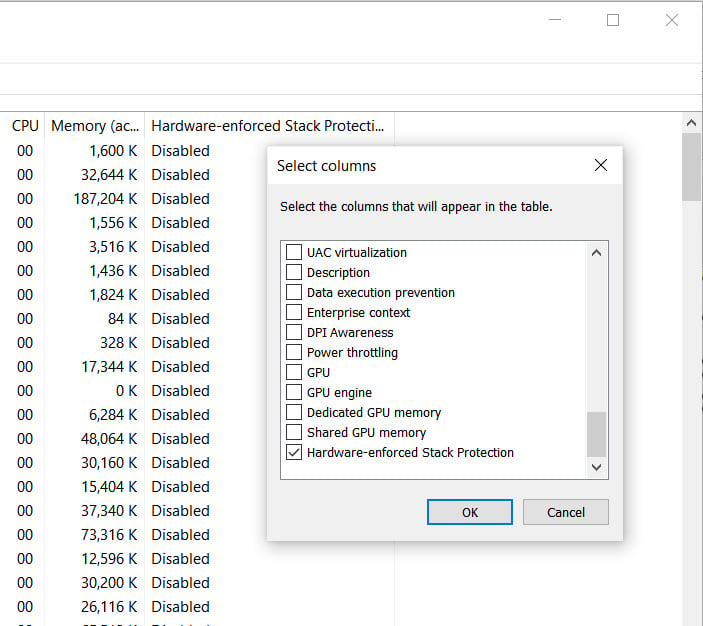
Windows 10 users running Intel 11th generation CPUs or AMD Zen 3 Ryzen CPUs, which also support CET, can use the Windows Task Manager to check if a process utilizes the hardware security feature.
To do this, open Task Manager, go into the Details tab, right-click on a column header, and then select ‘Select Colums.’
When the ‘Select columns’ dialog opens, scroll to the bottom and put a checkmark in ‘Hardware-enforced Stack Protection.’ Once enabled, this column will show you which processes support the Intel CET security feature.
BleepingComputer does not have any devices running 11th generation Intel CPUs to test this feature.
Also Read: Going Beyond DPO Meaning: Ever Heard of Outsourced DPO?
Google Chrome and Microsoft Edge 90 are expected to be released on April 13, 2021.