KEEP IN TOUCH
Subscribe to our mailing list to get free tips on Data Protection and Cybersecurity updates weekly!







Google Chrome is now blocking HTTP, HTTPS, and FTP access to TCP port 10080 to prevent the ports from being abused in NAT Slipstreaming 2.0 attacks.
Last year, security researcher Samy Kamkar disclosed a new version of the NAT Slipstreaming vulnerability that allows scripts on malicious websites to bypass visitors’ NAT firewall and gain access to any TCP/UDP port on the visitor’s internal network.
Using these vulnerabilities, threat actors can perform a wide range of attacks, including modifying router configurations and gaining access to private network services.
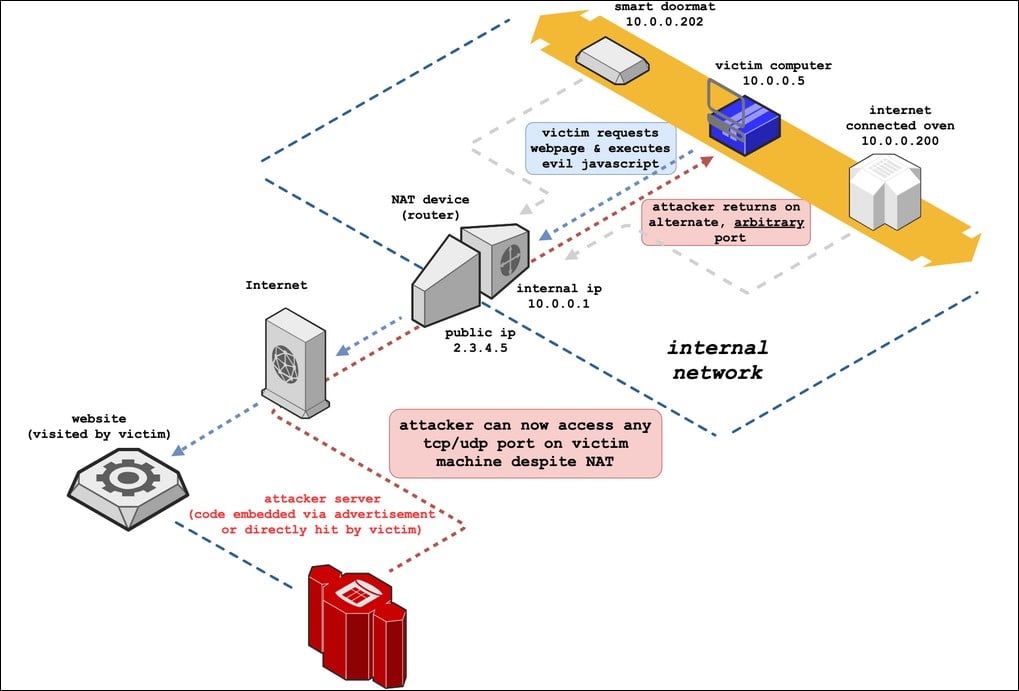
As this vulnerability only works on specific ports monitored by a router’s Application Level Gateway (ALG), browser developers have been blocking vulnerable ports that do not receive a lot of traffic.
Currently, Google Chrome is blocking FTP, HTTP, and HTTPS access on ports 69, 137, 161, 554, 1719, 1720, 1723, 5060, 5061, and 6566.
Today, Google has stated that they intend to block TCP port 10080 in Chrome, which Firefox has already blocked since November 2020.
In discussions regarding whether the port should be blocked, browser developers determined that the Amanda backup software and VMWare vCenter utilize the port but would not be affected by the block.
The most concerning point regarding blocking port 10080 is that some developers may utilize it as an alternative to port 80.
Also Read: Limiting Location Data Exposure: 8 Best Practices
“It is an attractive port for HTTP because it ends in in “80” and does not require root privileges to bind on Unix systems,” explains Google Chrome developer Adam Rice.
To allow developers to continue using this port, Rice will be adding an enterprise policy that developers can use to override the block.
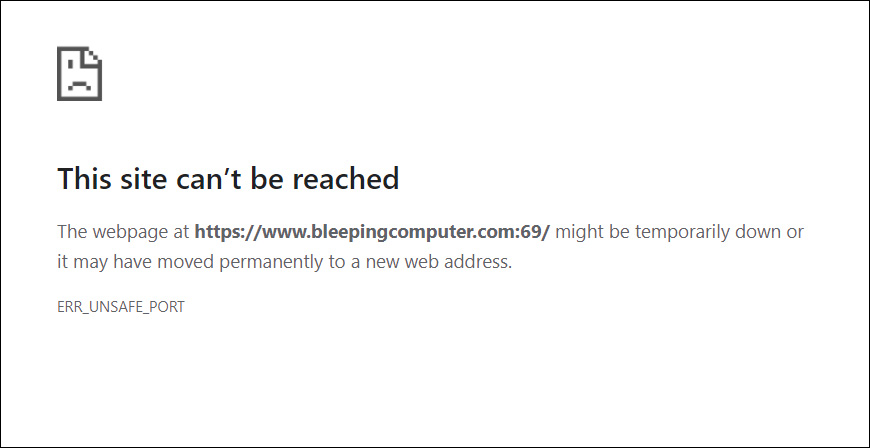
Once a port is blocked, users are shown an error message stating ‘ERR_UNSAFE_PORT’ when they attempt to access the port, as shown below.
Also Read: 10 Practical Benefits of Managed IT Services
If you are currently hosting a website on port 10080, you may want to consider using a different port to allow Google Chrome to continue accessing the site.