




The account information for almost 22 million ParkMobile customers is now in the hands of hackers and scammers after the data was released for free on a hacking forum.
On March 26th, 2021, ParkMobile issued a security notification on their website stating that one of their services was hacked and unauthorized people gained access to customer data.
“We recently became aware of a cybersecurity incident linked to a vulnerability in a third-party software that we use.”
“In response, we immediately launched an investigation with the assistance of a leading cybersecurity firm to address the incident. Out of an abundance of caution, we have also notified the appropriate law enforcement authorities,” reads the security notification.
Soon after, Brian Krebs reported that a threat actor was privately selling ParkMobile stolen during the data breach to other hackers for a high price of $125,000.
After a threat actor is unable to sell a stolen database or buyers begin to show little interest, it is common for the stolen data to be released on hacker forums for free as a way to increase reputation in the hacking community.
This is exactly what happened with ParkMobile, as threat actors published links to the full database yesterday on a popular hacking forum that allows anyone to download all of the data.
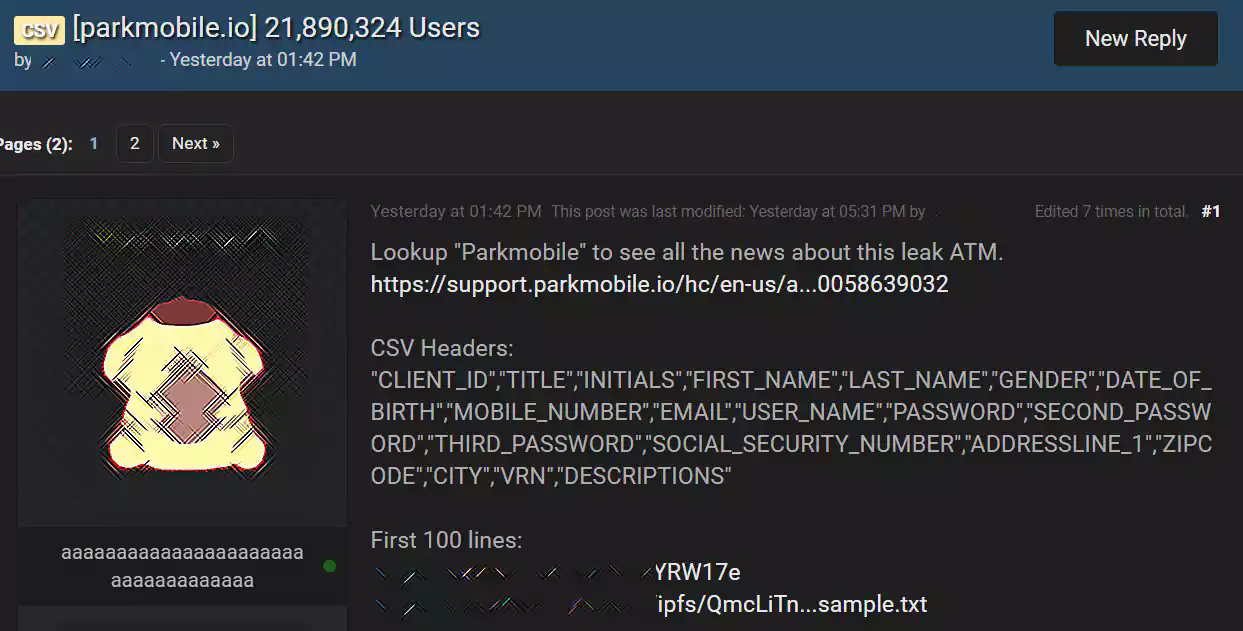
This data has been released as a 4.5 GB CSV text file containing the account information for 21,887,299 ParkMobile customers.
Also Read: How To Comply With PDPA: A Checklist For Businesses
The data includes customers’ first and last names, initials, mobile numbers, email addresses, user names, bcrypt hashed passwords, mailing address, license plate numbers, and vehicle information.
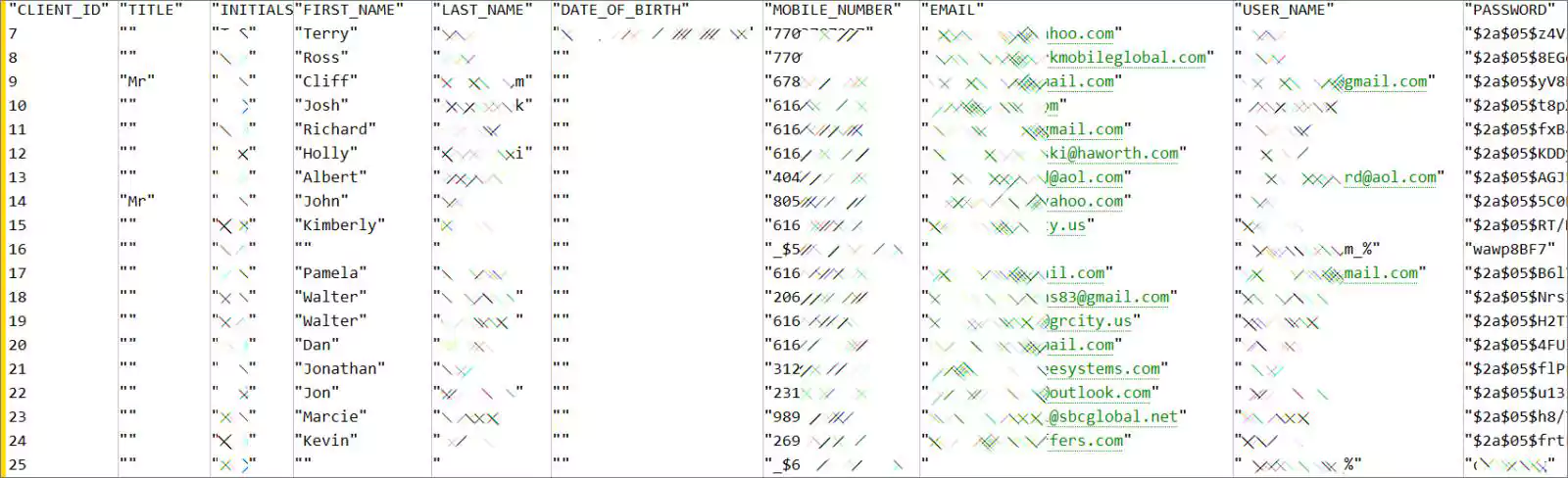
BleepingComputer has confirmed that the leaked information is legitimate after verifying data in the database for known ParkMobile users.
To check if the ParkMobile data breach includes your information, you can visit Have I Been Pwned and enter your email address in the search field. Once you click the ‘pwned?’ button, the site will display a list of all the data breaches where your email was exposed.
For example, below, I searched using an email address known to be part of the ParkMobile data breach. As you can see, Have I Been Pwned reports that the email was found in the ParkMobile data added to Have I Been Pwned.

If your data was exposed as part of this breach, you should read the following section to learn what to do.
If your data was exposed as part of this breach, the first thing you should do is immediately change your passwords at other sites using the same password as ParkMobile.
The ParkMobile passwords were hashed with an algorithm called bcrypt, which is difficult to convert into plain text passwords. However, it’s not impossible for threat actors to do so over time.
Once threat actors users gain your plain text passwords, they will use your email address and password combination to log in to other websites using credential stuffing attacks.
Also Read: In Case You Didn’t Know, ISO 27001 Requires Penetration Testing
These attacks would allow hackers to gain further access to your accounts and data.
Affected ParkMobile customers should also be on the lookout for phishing emails and SMS texts that use the exposed data to try and steal even more sensitive information from you.