




Global payments processor VISA warns that threat actors are increasingly deploying web shells on compromised servers to exfiltrate credit card information stolen from online store customers.
Web shells are tools (scripts or programs) deployed by threat actors to gain and/or maintain access to hacked servers, remotely execute arbitrary code or commands, move laterally within a target’s network, or deliver additional malicious payloads.
Throughout the last year, VISA has seen a growing trend of web shells being used to inject JavaScript-based scripts known as credit card skimmers into hacked online stores in web skimming (aka digital skimming, e-Skimming, or Magecart) attacks.
Once deployed, the skimmers allow them to steal the payment, and personal info submitted by the compromised online stores’ customers and send it to servers under their control.
“Throughout 2020, Visa Payment Fraud Disruption (PFD) identified a trend whereby many eSkimming attacks used web shells to establish a command and control (C2)during the attacks,” VISA said.
“PFD confirmed at least 45 eSkimming attacks in 2020 using web shells, and security researchers similarly noted increasing web shell use across the wider information security threat landscape.”
As VISA PFD found, web shells were mostly used by Magecart threat actors to backdoor hacked online store servers and set up a command-and-control infrastructure that allowed them to exfiltrate the stolen credit card info.
The attackers used multiple methods to breach the online shops’ servers, including vulnerabilities in unsecured administrative infrastructure, eCommerce-related application/website plugins, and outdated/unpatched eCommerce platforms.
Also Read: 3 Reasons Why You Must Take A PDPA Singapore Course
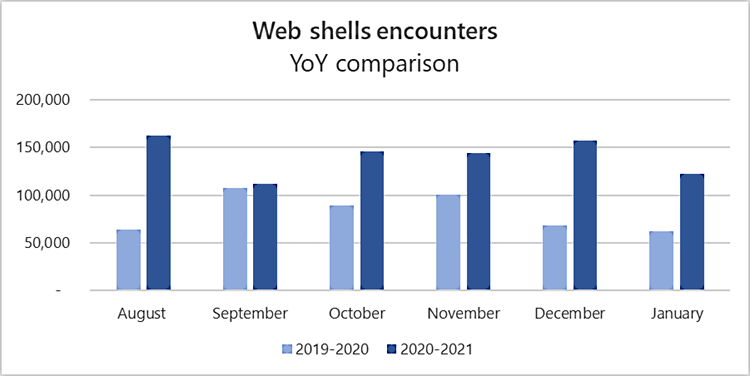
In February, VISA’s findings were confirmed by the Microsoft Defender Advanced Threat Protection (ATP) team, who said that the number of web shells deployed on compromised servers has almost doubled since last year.
The company’s security researchers discovered an average of 140,000 such malicious tools on hacked servers every month, between August 2020 to January 2021.
In comparison, Microsoft said in a 2020 report that it detected an average of 77,000 web shells each month, based on data collected from roughly 46,000 distinct devices between July and December 2019.
The US National Security Agency (NSA) also warned in a joint report issued with the Australian Signals Directorate (ASD) in April 2020 of threat actors escalating their attacks to backdoor vulnerable servers by deploying web shells.
“While the above tactics, techniques and procedures are not an exhaustive list of the various methods and exploits that attackers used in these web shell attacks, they are some of the leading methodologies identified,” VISA added.
“Identifying tactics, such as the use of web shells, also assists in identifying compromises when eSkimmers are not detected on the merchant website.
Also Read: What You Should Know About The Data Protection Obligation Singapore
“The use of web shells to facilitate eSkimming attacks will likely persist, especially as the restrictions around in-person, brick-and-mortar commerce remain in place as the pandemic continues.”