KEEP IN TOUCH
Subscribe to our mailing list to get free tips on Data Protection and Cybersecurity updates weekly!







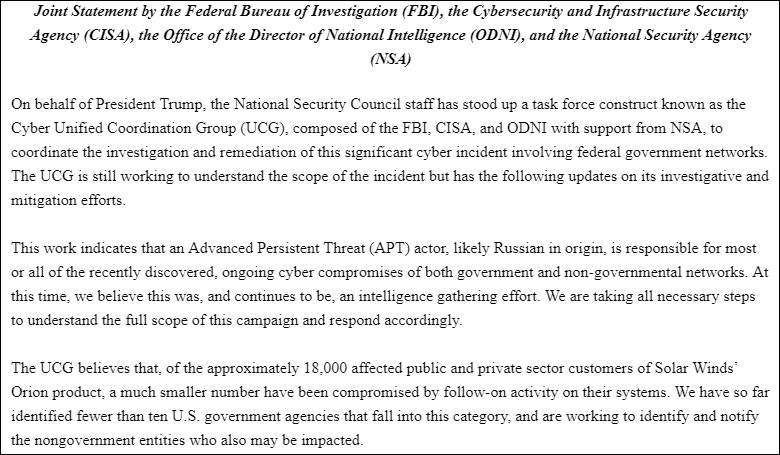
The Cyber Unified Coordination Group (UCG) said today that a Russian-backed Advanced Persistent Threat (APT) group is likely behind the SolarWinds hack.
The UCG was established by the National Security Council (NSC) after the SolarWinds supply chain attack to help the intelligence agencies better coordinate the government’s response efforts surrounding this ongoing espionage campaign.
“[A]n Advanced Persistent Threat (APT) actor, likely Russian in origin, is responsible for most or all of the recently discovered, ongoing cyber compromises of both government and non-governmental networks,” the UCG said.
“At this time, we believe this was, and continues to be, an intelligence gathering effort. We are taking all necessary steps to understand the full scope of this campaign and respond accordingly.”
The UCG also added in the joint statement issued by the FBI, CISA, ODNI, and the NSA that only 10 US government agencies were targeted by additional hacking activity after the initial breach.
“The UCG believes that, of the approximately 18,000 affected public and private sector customers of Solar Winds’ Orion product, a much smaller number have been compromised by follow-on activity on their systems,” the statement reads.
Also Read: Data Centre Regulations Singapore: Does It Help To Progress?
“We have so far identified fewer than ten U.S. government agencies that fall into this category, and are working to identify and notify the non-government entities who also may be impacted.”
The threat actor coordinating this operation is tracked by FireEye as UNC2452 and as Dark Haloby Volexity, and it is suspected to be APT29 according to unconfirmed media reports.
Russia denied links with the SolarWinds hackers saying that it “does not conduct offensive operations in the cyber domain.”
“This is a serious compromise that will require a sustained and dedicated effort to remediate,” the UCG added.
The compromise of several US federal networks was first acknowledged officially in a joint statement released by the FBI, DHS-CISA, and the ODNI on December 17, 2020.
CISA also issued an Emergency Directive after the suspected Russian state-sponsored hackers breached SolarWinds asking federal civilian agencies to disconnect or power down affected SolarWinds products to block future attacks.
The list of US agencies breached in this attack includes the US Treasury, the US Department of State, US NTIA, US NIH, DHS-CISA, the Department of Energy, the National Nuclear Security Administration, and the US Department of Homeland Security.
Also Read: Computer Misuse Act Singapore: The Truth And Its Offenses