




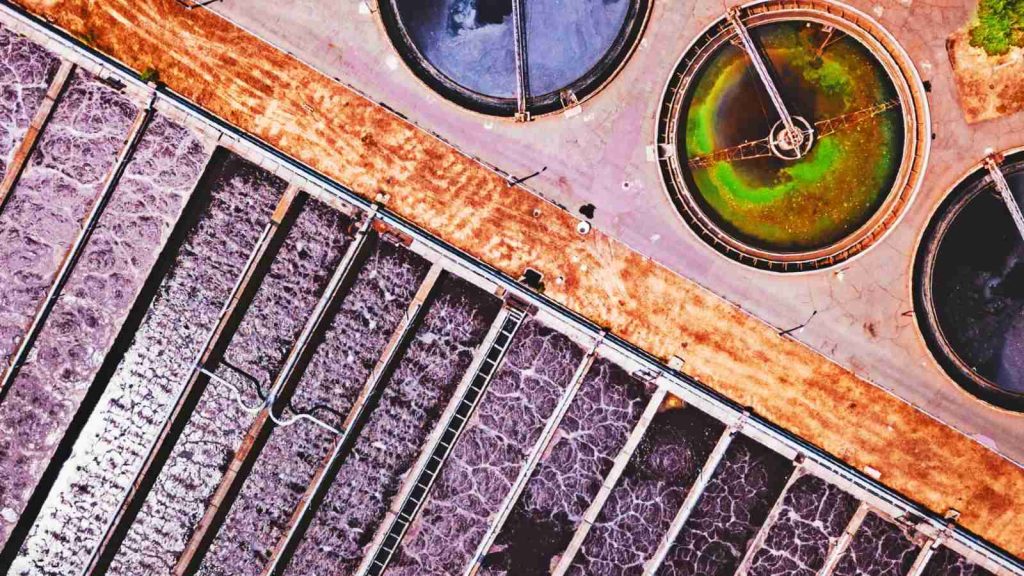
U.S. Water and Wastewater Systems (WWS) Sector facilities have been breached multiple times in ransomware attacks during the last two years, U.S. government agencies said in a joint advisory on Thursday.
The advisory also mentions ongoing malicious activity targeting WWS facilities that could lead to ransomware attacks affecting their ability to provide potable water by effectively managing their wastewater.
Since they are part of the 16 U.S. critical infrastructure sectors, their compromise and incapacitation via spearphishing and outdated software exploitation attacks would directly impact national security, economic security, and public health or safety.
Multiple ransomware strains were used in the incidents revealed in this advisory to encrypt water treatment facilities’ systems, including Ghost, ZuCaNo, and Makop ransomware:
Attackers had also infiltrated WWS plants’ networks attempting to poison the drinking water, as it happened in March 2019 when a former employee at Kansas-based WWS facility failed in his attempt to use unrevoked credentials for malicious purposes after he resigned.
While not included in the advisory, an unknown threat actor also gained access to the water treatment system for Oldsmar, Florida, in February 2021 and tried to poison the town’s drinking water by raising the levels of chemicals used to clean wastewater to hazardous levels.
Other breaches of water treatment facilities have happened over the past two decades, including a South Houston wastewater treatment plant in 2011, a water company with outdated software and hardware equipment in 2016, the Southern California Camrosa Water District in August 2020, and a Pennsylvania water system in May 2021.
“To secure WWS facilities—including Department of Defense (DoD) water treatment facilities in the United States and abroad— [..] , CISA, FBI, EPA, and NSA strongly urge organizations to implement the measures described in the Recommended Mitigations section of this advisory,” the joint advisory says.
You can find the complete list of mitigation measures recommended by the four federal agencies here.