KEEP IN TOUCH
Subscribe to our mailing list to get free tips on Data Protection and Cybersecurity updates weekly!






The Twitter account previously associated with the ANOM chat app is posting frivolous tweets this week. But, is it an account hijack, as some may wonder? Perhaps not.
ANOM was a fake encrypted messaging platform created as part of a global sting operation led by the U.S. FBI, Australian Federal Police (AFP), and other law enforcement agencies to catch criminals.
Also Read: How To Secure Your WiFi Camera: 4 Points To Consider
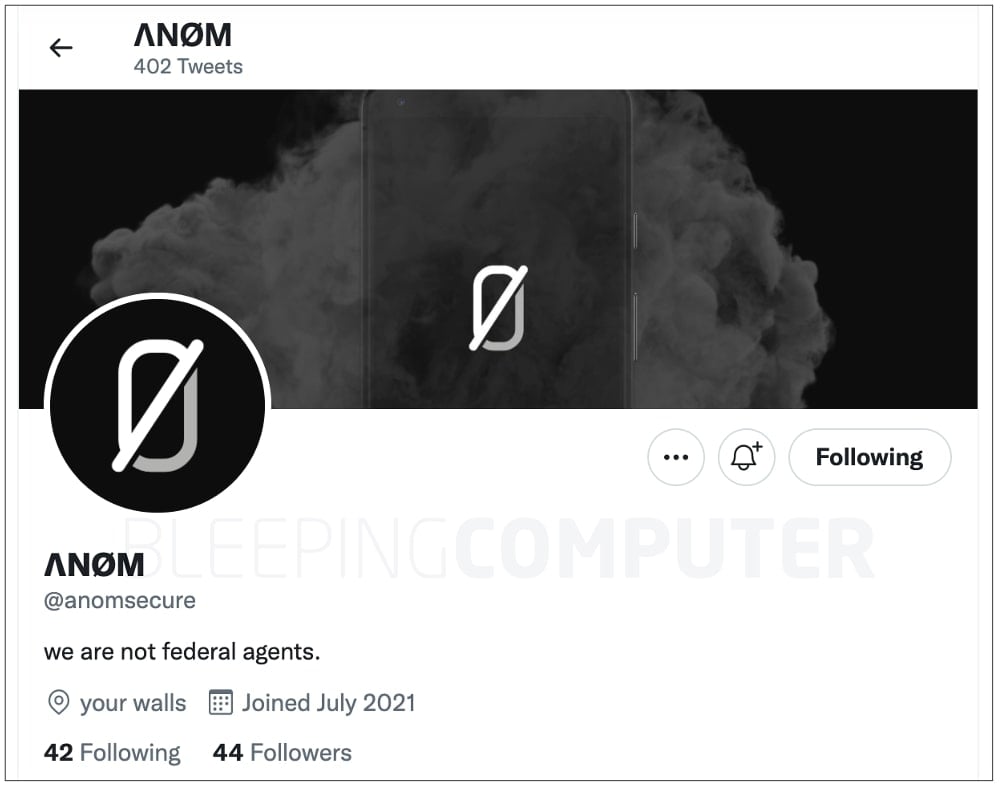
As seen by BleepingComputer today, ANOM’s Twitter account @anomsecure carries a revised bio that states “we are not federal agents,” in an attempt to mock ANOM’s purpose.
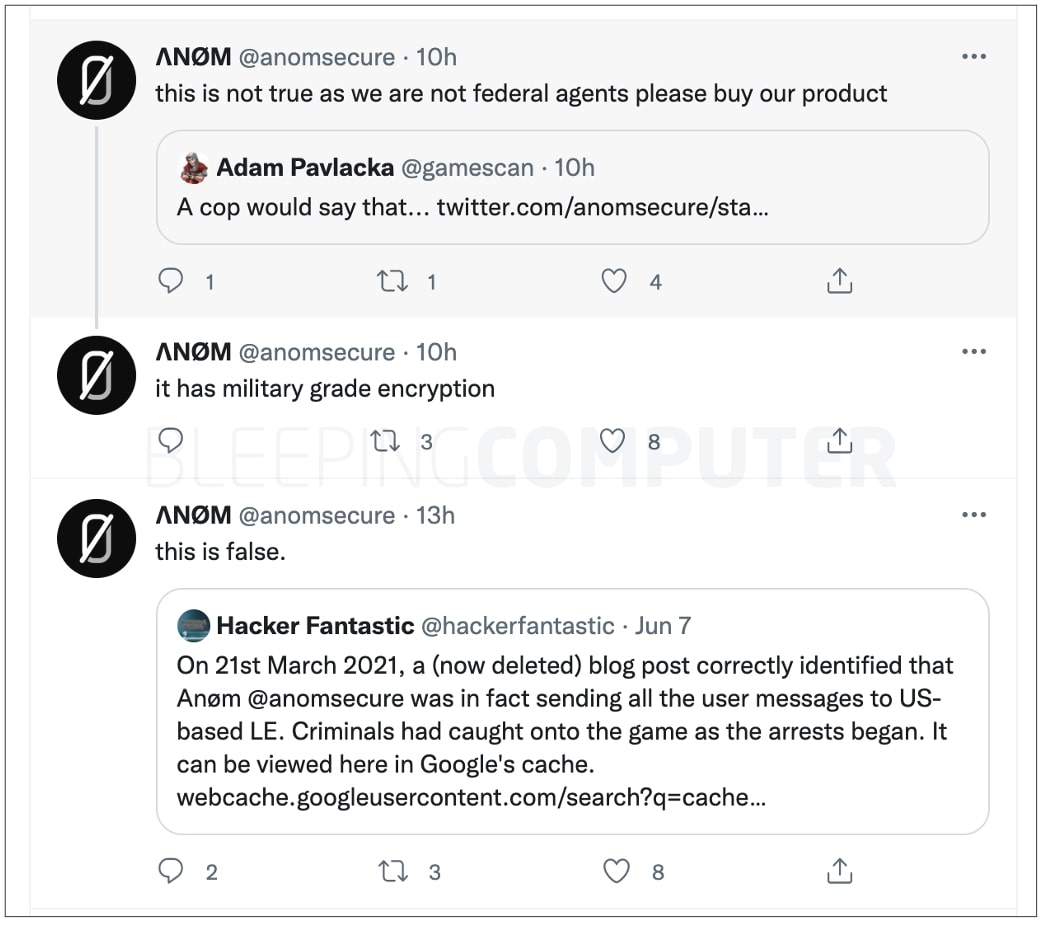
“Someone has taken over the social media accounts of ΛNØM, an encrypted phone messaging service that was reportedly used as a law enforcement sting, to tweet claims that they aren’t FBI…,” wrote Matthew Hickey aka Hacker Fantastic, co-founder of cybersecurity consultancy Hacker House, referring to the ongoing tweets published from the account:
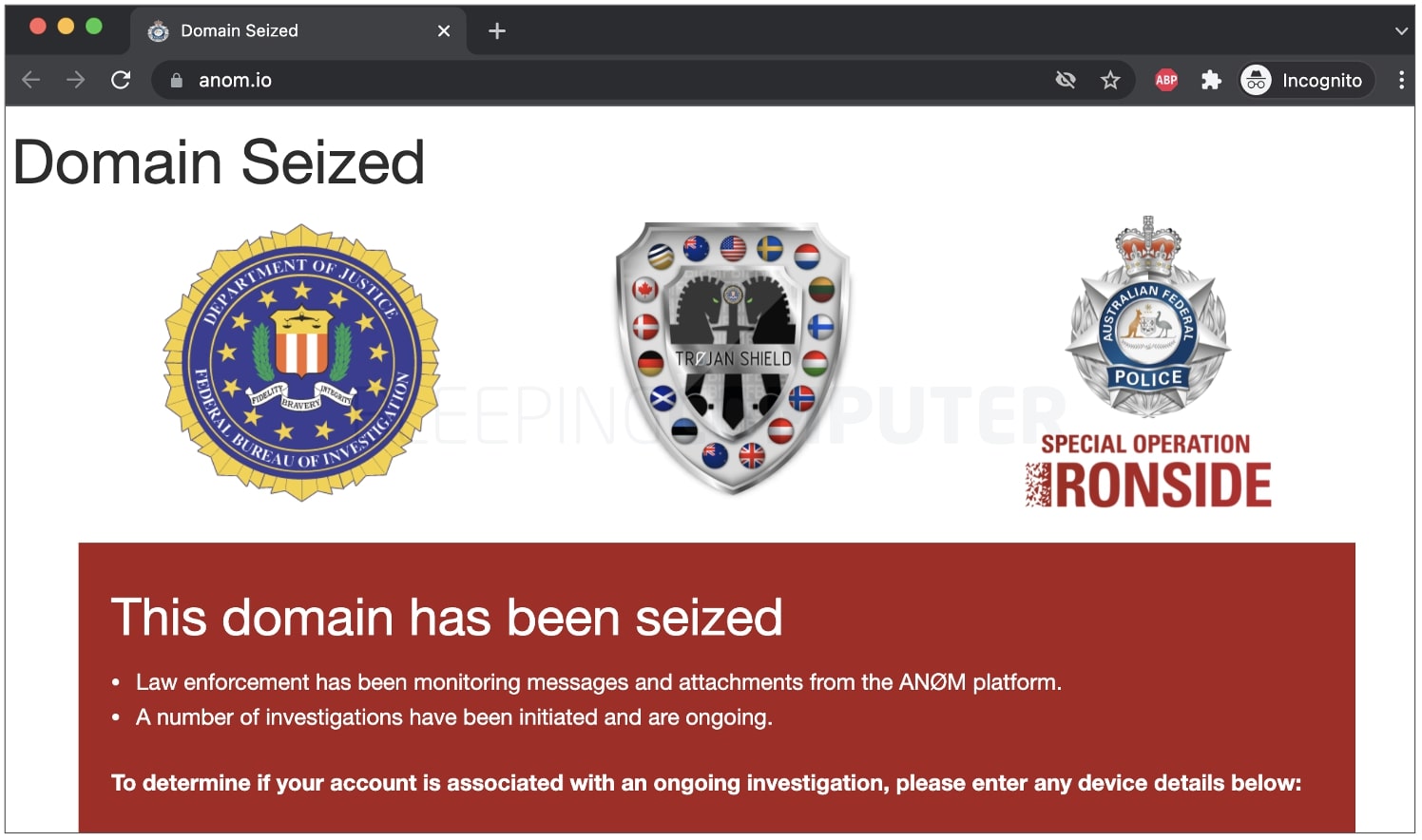
In June, BleepingComputer unveiled ANOM’s inception was part of a massive law enforcement initiative dubbed Operation Ironside, or Operation Trojan Shield that ran between 2018 and 2021.
During this time, the FBI, AFP, Europol, and various law enforcement agencies collaborated to create a fake encrypted messaging platform called Anom that was sold exclusively to criminals.
Also Read: How Formidable is Singapore Cybersecurity Masterplan 2020?
The platform allowed the authorities to intercept the messages and conversations between criminals.
After reviewing 27 million messages where criminals discussed their activities on the Anom platform, law enforcement was able to arrest 800 people and seize 8 tons of cocaine, 22 tons of cannabis and cannabis resin, 2 tons of synthetic drugs (amphetamine and methamphetamine), 6 tons of synthetic drugs precursors, 250 firearms, 55 luxury vehicles and over $48 million in various worldwide currencies and cryptocurrencies.
At the time, Europol acknowledged that many countries participated in the international coalition: Australia, Austria, Canada, Denmark, Estonia, Finland, Germany, Hungary, Lithuania, New Zealand, the Netherlands, Norway, Sweden, the United Kingdom incl. Scotland, and the United States.
This made Operation Ironside the “largest and most sophisticated law enforcement operations to date.”
Prior to ANOM’s social media account posting mock tweets of today, in June, the account’s bio linked to the anom.io domain and had a more believable description:
“Encrypted Messaging Platform, Keep Secrets Safe || App that enforces your Privacy #Anom…”
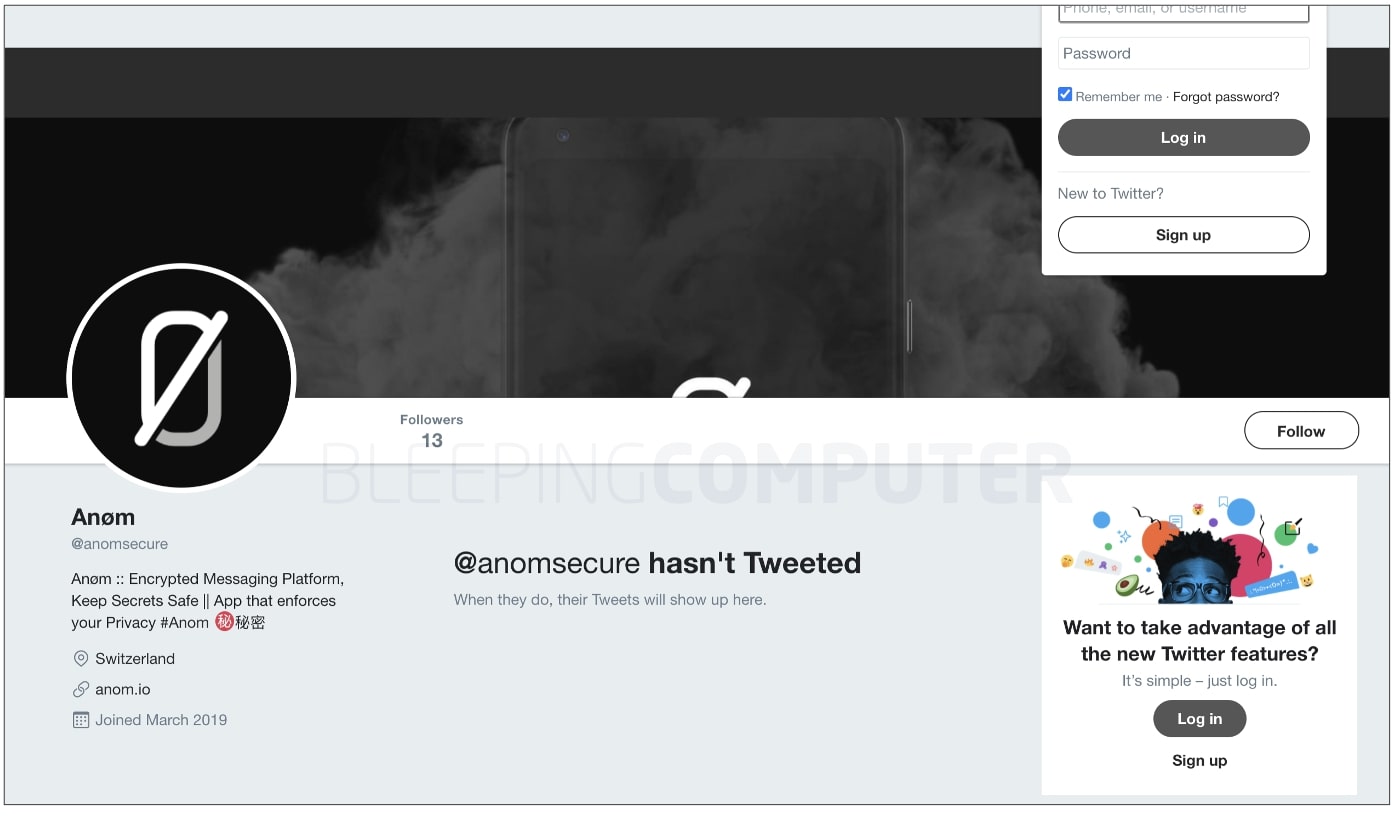
Later in June, the @anomsecure Twitter account had completely disappeared, leading to a “nothing to see here… looks like this page doesn’t exist” message, as confirmed by BleepingComputer.
This could have happened, for example, if the Twitter username was changed, and the @anomsecure handle became available for anyone to claim.
Twitter clearly states that “once you change your username, your previous username will immediately be available for use by someone else.”
Around the same time, as Operation Ironside was being made public knowledge, the anom.io domain was set to display a “domain seized” notice by the law enforcement agencies, which is still up today.
Since then, the oldest tweet still available today from @anomsecure, as seen by BleepingComputer, dates back to July 23rd. And, the account’s “joined” date states “July 2021,” as opposed to “March 2019” listed in the June screenshot above.
It is therefore looking increasingly likely that rather than an account hijack, this is simply a case of @anomsecure handle becoming available at some point in time, and claimed July 4th, 2021 by a troll who is behind the new bio and mock tweets.
BleepingComputer has reached out to multiple law enforcement agencies associated with ANOM for comment and we are awaiting their response.