





A joint announcement from the Ministry of Health and the National Cyber Directorate in Israel describes a spike in ransomware attacks over the weekend that targeted the systems of nine health institutes in the country.
In the joint announcement, the Israeli government states that the attempts resulted in no damage to the hospitals and the medical organizations, thanks to national-level coordination and the quick and decisive response of the local IT teams.
The two authorities had carried out numerous defensive activities in the health sector to identify open vulnerabilities and secure them before the weekend arrived, mostly in response to a Wednesday attack on the Hillel Yaffe Medical Center.
As it seems, though, these efforts weren’t enough to secure the exposed endpoints, and some healthcare organizations were still breached over the weekend.
Also Read: How Bank Disclosure Of Customer Information Work For Security
According to local media reports, the attack is attributed to a Chinese group of actors using the ‘DeepBlueMagic’ ransomware strain, which first appeared in the wild in August this year.
DeepBlueMagin is known to disable security solutions that usually detect and block file encryption attempts, allowing for successful attacks.
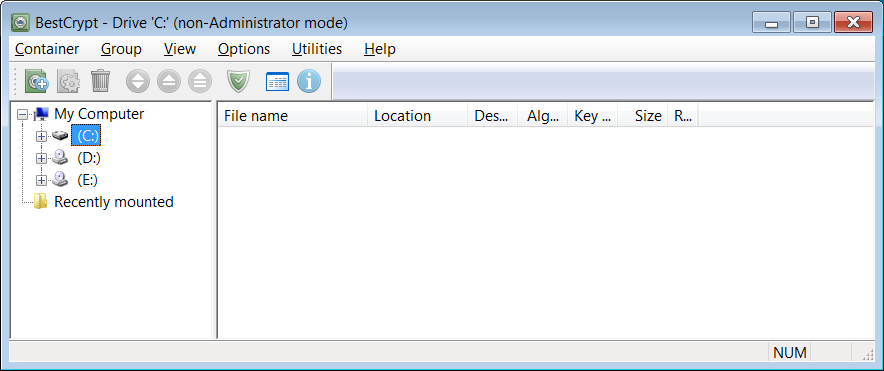
Testing the IOCs shared by the authorities, BleepingComputer determined that the threat actors are using the ‘BestCrypt’ hard drive encryption tool to encrypt devices.
Israel’s National Cyber Directorate has released indicators of compromise (IOCs) in the form of file hashes that have been seen in related attacks.
The agency suggests that Israeli organizations perform the following steps:
In the meantime, the Hillel Yaffe Medical Center in the north of Tel Aviv is still struggling with the restoration of its systems, and the staff is using “pen a paper” to admit patients and circulate exams for the sixth day now.
Also Read: Data Protection Framework: Practical Guidance for Businesses
Even though there’s hope that the Hillel Yaffe Medical Center will return to normal operations in a few days, there are fears that some medical records will be unrecoverable.
This is because the ransomware actors reportedly accessed the backup system, wiping all copies stored there for emergency cases like cyberattacks.
Reuven Eliyahu, the cybersecurity chief in the Health Ministry has confirmed that the mid-week attack was carried out by Chinese hackers in a statement today, and described the actors’ motives as “purely financial”.
“This is probably a Chinese hacker group that broke away from another group and started working in August,” Eliyahu said in an interview with Army Radio. “The motive for the attack was purely financial.”
However, a source in the cybersecurity industry has told BleepingComputer that the attribution to China is weak and that the attacks may have simply been port scans or probes into a network’s defenses.
As for the ransom payment, the Hillel Yaffa center is a government-owned hospital, and as such, it won’t negotiate with hackers.
Update 10/18/21 02:31 PM EST: Added further information about attribution to China.