KEEP IN TOUCH
Subscribe to our mailing list to get free tips on Data Protection and Cybersecurity updates weekly!






Russian-speaking hacking group Turla has hacked into the systems of an undisclosed European government organization according to a new Accenture Cyber Threat Intelligence (ACTI) report.
This attack perfectly lines up with Turla’s information theft and espionage motivation and its persistent targeting of government-related entities from a wide range of countries.
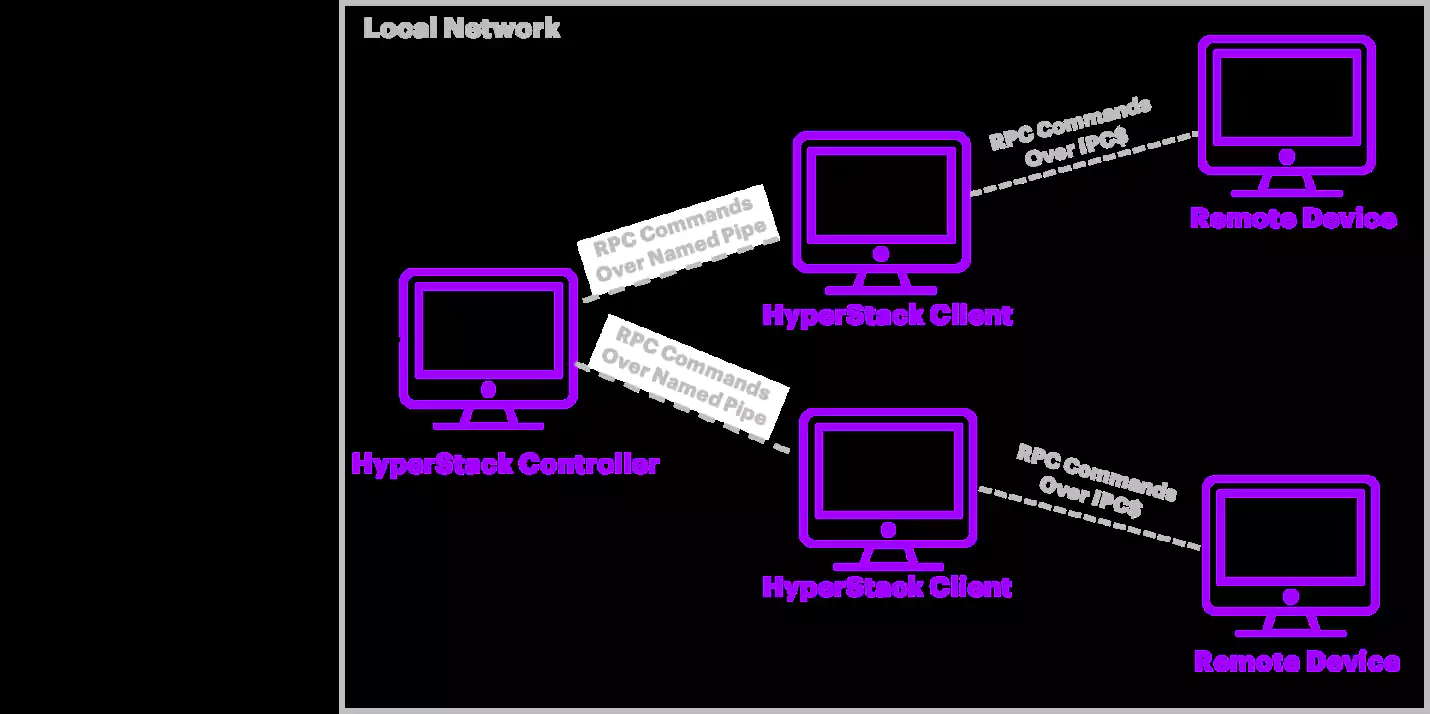
To compromise the organization’s network, the attackers used a combination of recently updated remote administration trojans (RATs) and remote procedure call (RPC)-based backdoors including HyperStack, analyzed by ACTI between June and October 2020.
“Notably, Accenture researchers recently identified novel command and control (C&C) configurations for Turla’s Carbon and Kazuar backdoors on the same victim network,” ACTI researchers said.
“The Kazuar instances varied in configuration between using external C&C nodes off the victim network and internal nodes on the affected network, and the Carbon instance had been updated to include a Pastebin project to receive encrypted tasks alongside its traditional HTTP C&C infrastructure.”
In all, during their espionage campaigns, Turla has compromised thousands of systems belonging to governments, embassies, as well as education and research facilities from over 100 countries.
Also Read: How Long Do Employers Keep Employee Records After Termination? 1 Hard Question
“Turla will likely continue to use its legacy tools, albeit with upgrades, to compromise and maintain long-term access to its victims because these tools have proven successful against Windows-based networks,” Accenture said.
Government entities are advised by ACTI to check network logs for indicators of compromise included at the end of the report and to build detections capable of blocking future Turla attacks.
The Turla group (also tracked as Waterbug and VENOMOUS BEAR) has been active since 1996 and the main suspect behind attacks targeting the Pentagon and NASA, the U.S. Central Command, the Finnish Foreign Ministry, and, earlier this year, Eastern European Ministries of Foreign Affairs.
The state-sponsored hacking group is also known for using unorthodox methods to achieve its cyber-espionage goals.
For instance, they’ve created backdoor trojans with their own APIs to reverse communication flows and controlled malware using comments on Britney Spears Instagram photos. They have also hijacked the infrastructure and malware of the Iranian-sponsored OilRig hacking group to use them in their own campaigns.
Also Read: By Attending This Event You Agree To Be Photographed
In May, ESET spotted a new version of the ComRAT backdoor controlled by Turla using the Gmail web interface in data theft attacks that targeted governmental institutions.
Also in May, Kaspersky shared info on what is believed to be another Turla malware “with a medium-to-low level of confidence”, a RAT variant dubbed COMpfun controlled using uncommon HTTP status codes deployed in attacks against European diplomatic entities.