KEEP IN TOUCH
Subscribe to our mailing list to get free tips on Data Protection and Cybersecurity updates weekly!





After infecting themselves with their own custom remote access trojan (RAT), an Indian-linked cyber-espionage group has accidentally exposed its operations to security researchers.
The threat actor has been active since at least December 2015 and is tracked as PatchWork (aka Dropping Elephant, Chinastrats, or Quilted Tiger) due to the use of copy-pasted code.
During PatchWork’s most recent campaign, between late November to early December 2021, Malwarebytes Labs observed the threat actors using malicious RTF documents impersonating Pakistani authorities to infect targets with a new variant of the BADNEWS RAT, known as Ragnatela.
Also Read: PDPA Meaning: Know Its Big Advantages In Businesses
The Ragnatela RAT allows the threat actors to execute commands, capture screen snapshots, log keystrokes, harvest sensitive files and a list of running apps, deploy additional payloads, and upload files.
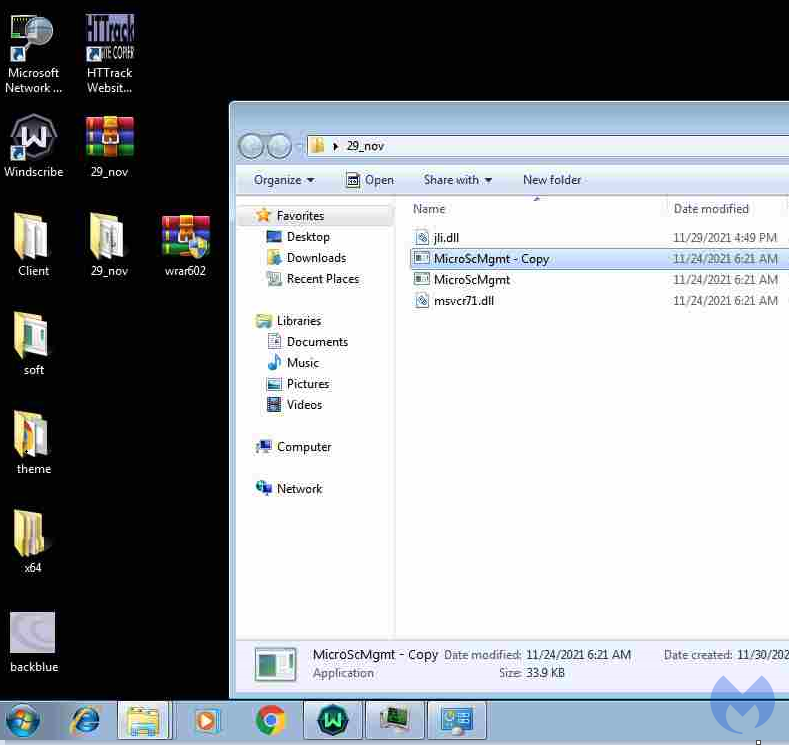
“Ironically, all the information we gathered was possible thanks to the threat actor infecting themselves with their own RAT, resulting in captured keystrokes and screenshots of their own computer and virtual machines,” Malwarebytes Labs’ Threat Intelligence Team explained.
After discovering that the PatchWork operators infected their own development systems with the RAT, the researchers were able to monitor them while using VirtualBox and VMware for testing and web development and testing on computers with dual keyboard layouts (i.e., English and Indian).
While observing their operations, they also gained info on targets the group compromised, including Pakistan’s Ministry of Defense and faculty members from molecular medicine and biological science departments at multiple universities such as the National Defense University of Islam Abad, the UVAS University’s Faculty of Bio-Science, the Karachi HEJ Research institute, and SHU University.
Also Read: What Is PDPA And What Are The 5 Things You Should Know About
“Thanks to data captured by the threat actor’s own malware, we were able to get a better understanding about who sits behind the keyboard,” Malwarebytes Labs added.
“The group makes use of virtual machines and VPNs to both develop, push updates and check on their victims. Patchwork, like some other East Asian APTs is not as sophisticated as their Russian and North Korean counterparts.”
PatchWork operators have previously targeted US think tanks in March 2018 in multiple spear-phishing campaigns using the same tactic of pushing malicious RTF files to compromise their victims’ systems and a QuasarRAT malware variant.
Two months earlier, in January 2018, they were observed pushing weaponized documents delivering BADNEWS malware in attacks against targets from the Indian subcontinent.
They were also behind a spear-phishing campaign targeting employees of a European government organization during late May 2016.