KEEP IN TOUCH
Subscribe to our mailing list to get free tips on Data Protection and Cybersecurity updates weekly!







A security researcher has released a new proof-of-concept exploit this weekend that requires slight modification to install web shells on Microsoft Exchange servers vulnerable to the actively exploited ProxyLogon vulnerabilities.
Since Microsoft disclosed actively exploited Microsoft Exchange security vulnerabilities, known collectively as ProxyLogon, administrators and security researchers have been scrambling to protect vulnerable servers exposed on the Internet.
These attacks are being used to drop
web shells, cryptominers, and more recently, the DearCry ransomware on exploited servers.
Earlier this week, a security researcher named Nguyen Jang published a blog post detailing a proof of concept (POC) exploit for the Microsoft Exchange ProxyLogon vulnerability. Jang also shared a purposely broken exploit on GitHub that needs some fixes to work properly.
“Firstly, the PoC I gave can not run correctly. It will be crashed with many of errors. Just for trolling the reader,” Jang told BleepingComputer.
The PoC, though, provided enough information that security researchers and threat actors could use it to develop a functional remote code execution exploit for Microsoft Exchange servers.
Soon after the PoC was published, Jang received an email from Microsoft-owned GitHub stating that the PoC was being taken down as it violated Acceptable Use Policies.
In a statement to BleepingComputer, GitHub said they took down the PoC to protect devices that are being actively exploited.
Also Read: 3 Reasons Why You Must Take A PDPA Singapore Course
“We understand that the publication and distribution of proof of concept exploit code has educational and research value to the security community, and our goal is to balance that benefit with keeping the broader ecosystem safe. In accordance with our Acceptable Use Policies, GitHub disabled the gist following reports that it contains proof of concept code for a recently disclosed vulnerability that is being actively exploited.” – GitHub.
This weekend, a different security researcher published a new ProxyLogon PoC that requires very little modification to exploit a vulnerable Microsoft Exchange server and drop a web shell on it.
Will Dormann, a Vulnerability Analyst at the CERT/CC, tested the vulnerability on a Microsoft exchange server and told BleepingComputer that it worked with very little modification.
“It’s within the reach of “script kiddie” now,” warned Dormann in our discussion about the PoC.
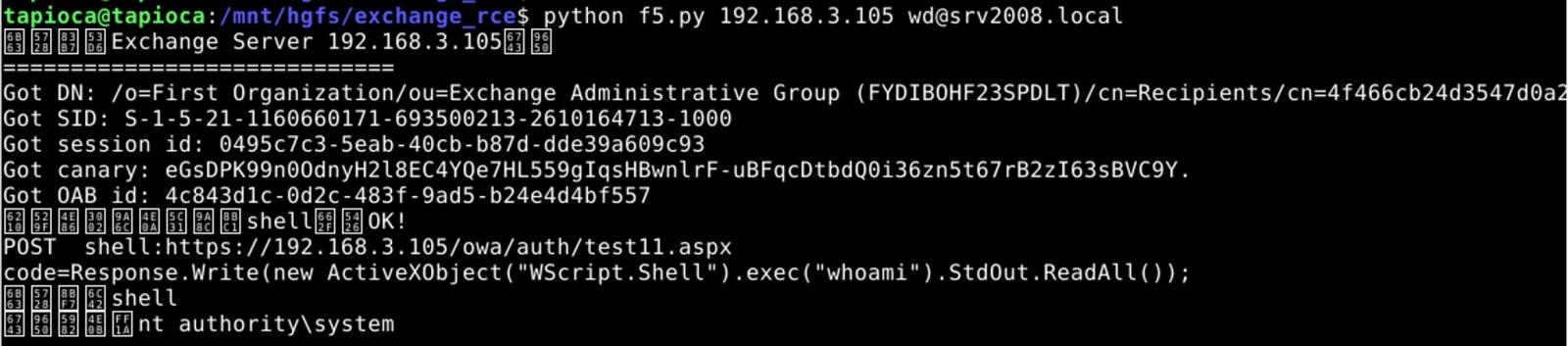
As you can see from the image below, Dormann used the exploit against a Microsoft Exchange server and remotely installed a web shell, and executed the ‘whoami’ command.
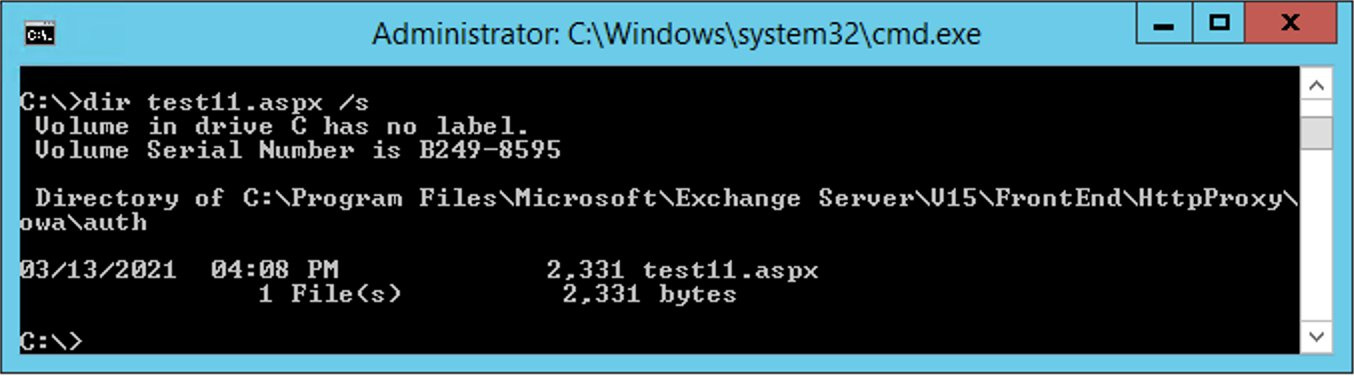
Another image shared by Dormann shows that the exploit dropped the test11.aspx web shell in the specified location on the server.
Didier Stevens, a senior analyst at NVISO and SANS ISC senior handler, also tested the exploit against a Microsoft Exchange virtual machine but did not have as much luck with the PoC.
In a conversation with BleepingComputer, Stevens said that he tested the new PoC against an unpatched Exchange 2016 with no cumulative updates. Still, the PoC would not work without tweaking some Active Directory settings.
However, Stevens said that new information in the PoC released this weekend enabled him to get Jang’s PoC working to achieve successful remote code execution against his Microsoft Exchange server.
Stevens also agreed with Dormann’s assessment that the information disclosed in the new PoC would make it easier for less-skilled threat actors, known as ‘Script Kiddies,’ to create a working ProxyLogon exploit.
Due to the large number of vulnerable servers still exposed on the Internet, BleepingComputer will not be sharing links to the PoC released this weekend.
With exploits for the Microsoft Exchange vulnerabilities becoming publicly available, it is more important than ever that administrators patch their servers.
According to Palo Alto Networks’ research, there are approximately 80,000 vulnerable Microsoft Exchange servers exposed on the Internet.
“The number of vulnerable servers running old versions of Exchange that cannot directly apply the recently released security patches dropped over 30% from an estimated 125,000 to 80,000, according to Expanse internet scans conducted March 8 and 11,” Palo Alto Networks told BleepingComputer.
Microsoft also warned that even though there has been a significant drop of vulnerable servers, there are still many that need to be patched.
“Based on telemetry from RiskIQ, we saw a total universe of nearly 400,000 Exchange servers on March 1. By March 9 there were a bit more than 100,000 servers still vulnerable. That number has been dropping steadily, with only about 82,000 left to be updated,” Microsoft stated in a blog post.
Also Read: What You Should Know About The Data Protection Obligation Singapore
Many of these servers are for older versions that did not have available security updates.
On Thursday, Microsoft released additional security updates for older versions of Microsoft Exchange, which now cover 95% of the servers exposed on the Internet.