KEEP IN TOUCH
Subscribe to our mailing list to get free tips on Data Protection and Cybersecurity updates weekly!







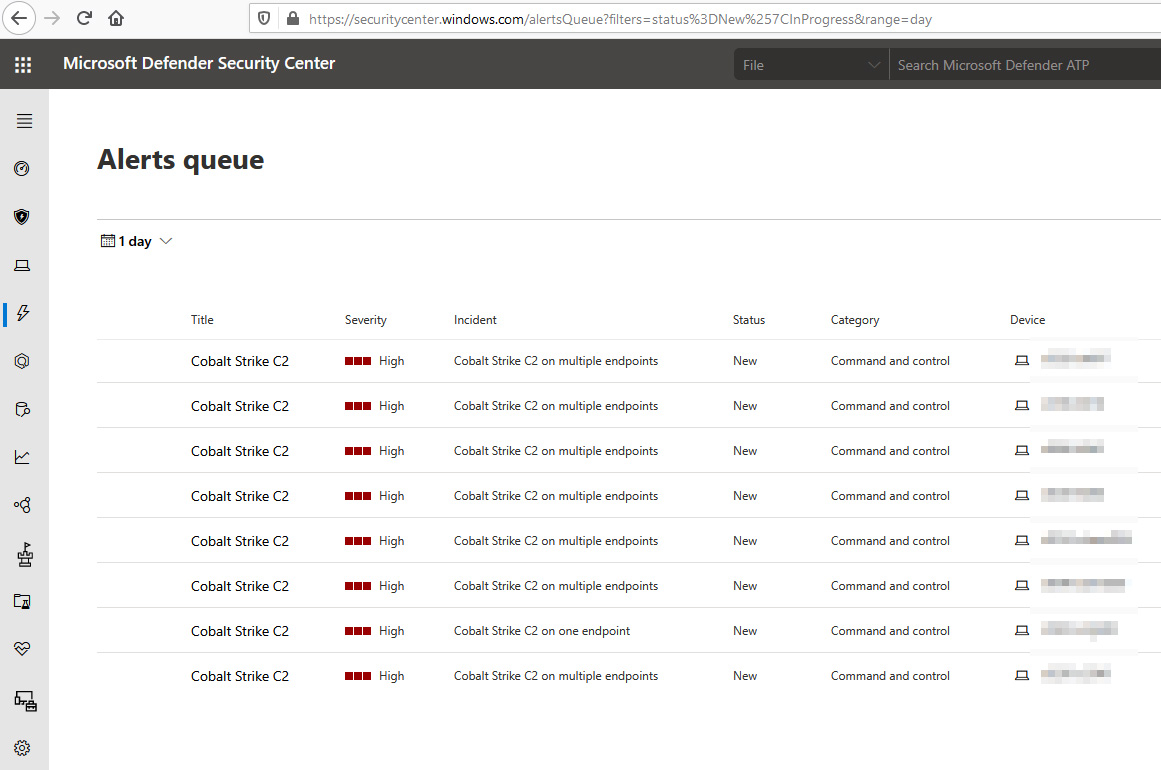
Administrators woke up to a scary surprise today after false positives in Microsoft Defender ATP showed network devices infected with Cobalt Strike.
Microsoft Defender ATP is Microsoft’s enterprise antivirus and threat monitoring solution that admins deploy on devices throughout an organization. These endpoints then monitor devices for malicious threats and behavior and send them back to Microsoft’s cloud-based Microsoft Defender Security Center, where the alerts are aggregated and viewed from a central location.
Starting today at approximately 7:30 AM CET / 2:30 AM EST, administrators worldwide woke up to a long list of ‘Cobalt Strike C2’ alerts detected throughout their organization.
Cobalt Strike is a legitimate penetration testing toolkit that allows attackers to deploy “beacons” on a compromised device to “create shells, execute PowerShell scripts, perform privilege escalation, or spawn a new session to create a listener on the victim system.”
Also Read: How Singapore Cybersecurity Masterplan 2020 Is Formidable
Attackers use cracked versions of Cobalt Strike to gain persistent remote access to a compromised network and are commonly used during ransomware attacks.
Seeing these alerts, many security administrators were scared that their networks were compromised and rushed to check for active infections.
It turns out that this was a Microsoft Defender ATP false positive that was detecting network connections to 127.0.0.1 (localhost) as Cobalt Strike C2 traffic.
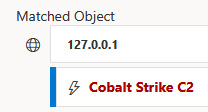
Microsoft Senior Threat Intelligence Analyst Kevin Beaumont confirmed the false positive on Twitter and stated that it should now be marked as such in the console. The bad signature causing the false positive has also been fixed, and admins should no longer see new alerts in Microsoft Defender Security Center.
Also Read: Going Beyond DPO Meaning: Ever Heard Of Outsourced DPO?
With that said, an alert for a Cobalt Strike beacon is a severe detection and, if you received such alerts, you are better off being safe than sorry and should perform a sweep of all affected devices.
Spending a few hours to double-check the devices will save you from many future headaches if it turns out to be a real detection mixed in with the false positive.