KEEP IN TOUCH
Subscribe to our mailing list to get free tips on Data Protection and Cybersecurity updates weekly!






Medtronic is urgently recalling remote controllers for insulin pumps belonging to the ‘MiniMed Paradigm’ family of products, due to severe cybersecurity risks.
The controllers that should be returned to the vendor are models MMT-500 and MMT-503, used with Medtronic MiniMed 508 insulin pump and the MiniMed Paradigm family of insulin pumps.
These devices were sold in the United States between August 1999 and July 2018, and it is estimated that there are 31,310 vulnerable units in use by diabetic patients in the country at the moment.
Insulin pumps are used for delivering insulin to diabetic users, while the remote controller aids in the wireless commanding of the device. It can be utilized to start, stop, or change the amount of insulin that is administered to the user.
Also Read: PDPA Laws And Regulations; A Systematic Guidelines In Singapore
The problem with these older remotes is that an unauthorized person could potentially record and replay the wireless communication signal that is generated when the user presses a button on the controller, sending commands directly to the insulin pump.
In this way, someone could purposefully over-deliver or stop the delivery of insulin to the patient. For some people who suffer from severe diabetes, going through hypoglycemia or ketoacidosis even shortly could lead to their death.
Medtronic told BleepingComputer that there are no confirmed reports of a remote controller being manipulated in this manner.
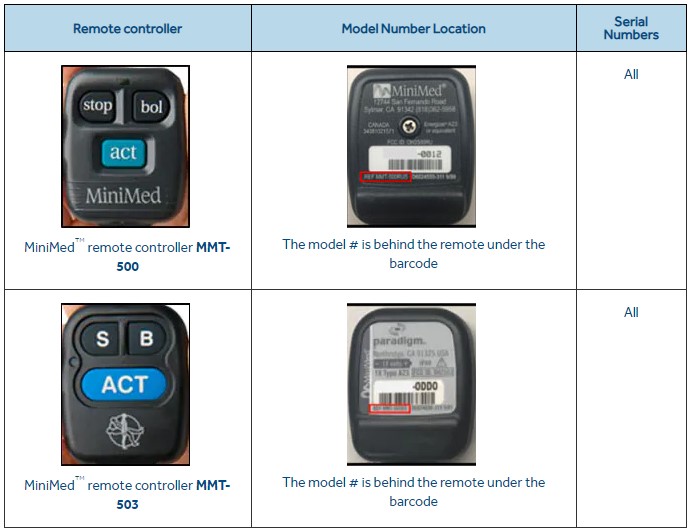
If you or your healthcare provider is using one of the remote controllers depicted above, Medtronic is advising that users immediately discontinue using them.
“You should immediately stop using and disconnect the remote controller, disable the remote feature, and return the remote controller to Medtronic. See the Appendix attached to this letter for detailed instructions” – Medtronic
Medtronic has sent letters with specific instructions for users’ recalled model, but if you’re a second-hand user you may find the instructions for each particular model on this ‘Urgent Medical Device Recall’ notice.
After you have disabled the controller and deleted the IDs, you are advised to send it back to the vendor by following the instructions provided here.
Also Read: PDPA Meaning: Know Its Big Advantages In Businesses
Back in June 2019, Medtronic and the FDA warned users of the MiniMed 508 and the Paradigm series insulin pumps about hacking risks, running a national recall program to address them.
That case concerned the potential for a man-in-the-middle attack exploiting the pump’s connection with other medical devices such as blood glucose meters and flow monitoring systems that are typically used in conjunction with insulin pumps.
The general takeaway is that if you’re using medical devices with “smart” or even remote communication capabilities, you should keep a close eye on their functions and ensure that they’re operating as they’re supposed to.