





A massive ransomware campaign targeting QNAP devices worldwide is underway, and users are finding their files now stored in password-protected 7zip archives.
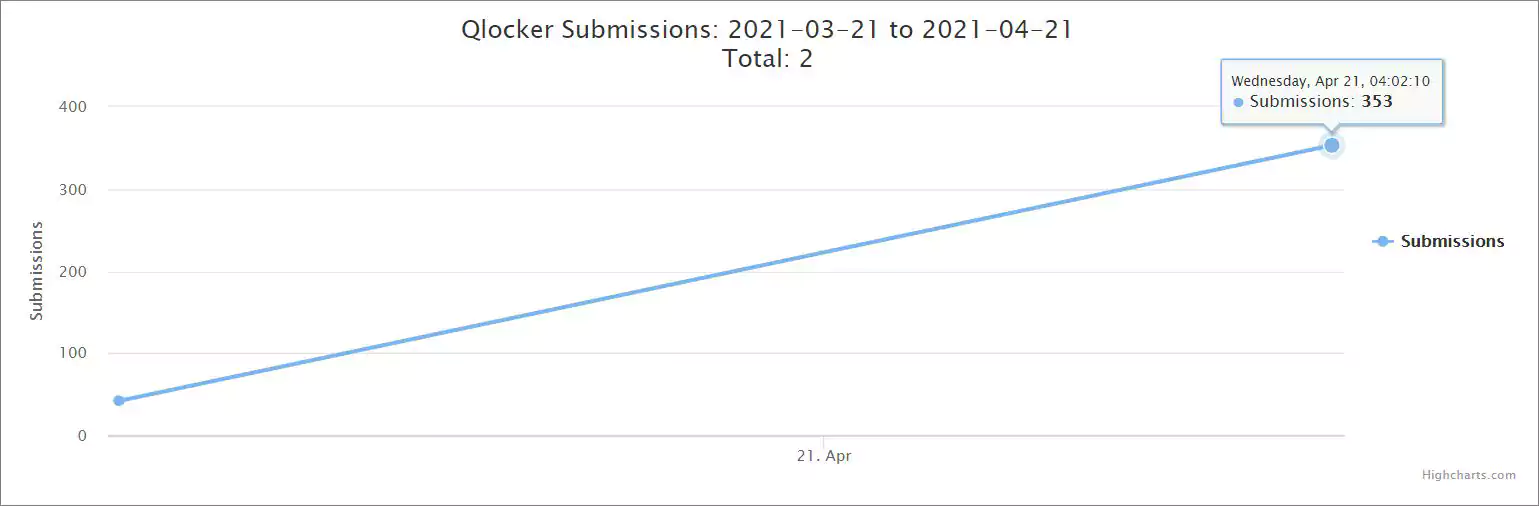
The ransomware is called Qlocker and began targeting QNAP devices on April 19th, 2021. Since then, there has been an enormous amount of activity in our support forum, and ID-Ransomware has seen a surge of submissions from victims.
Also Read: Compliance Course Singapore: Spotlight On The 3 Offerings
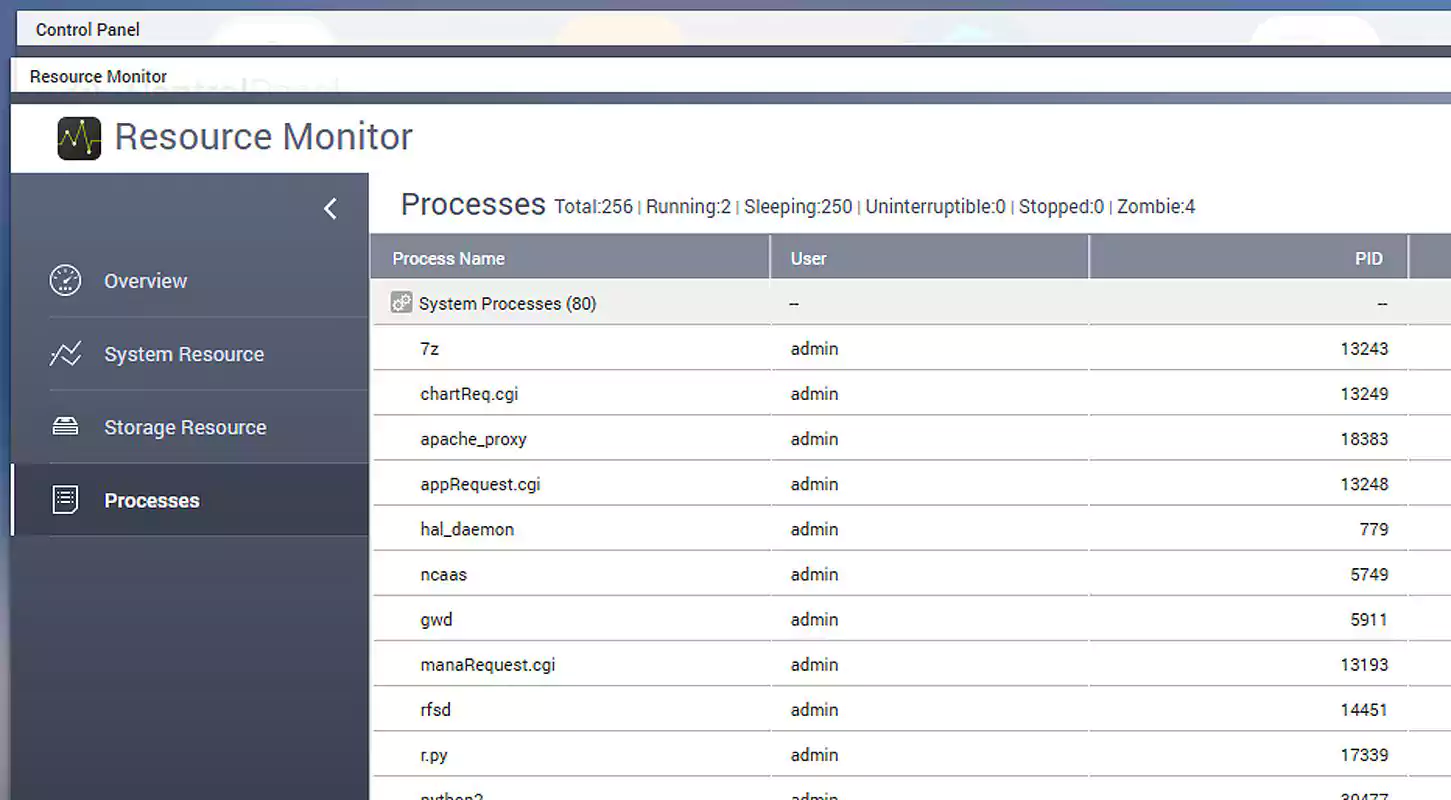
According to reports from victims in a BleepingComputer Qlocker support topic, the attackers use 7-zip to move files on QNAP devices into password-protected archives. While the files are being locked, the QNAP Resource Monitor will display numerous ‘7z’ processes which are the 7zip command-line executable.
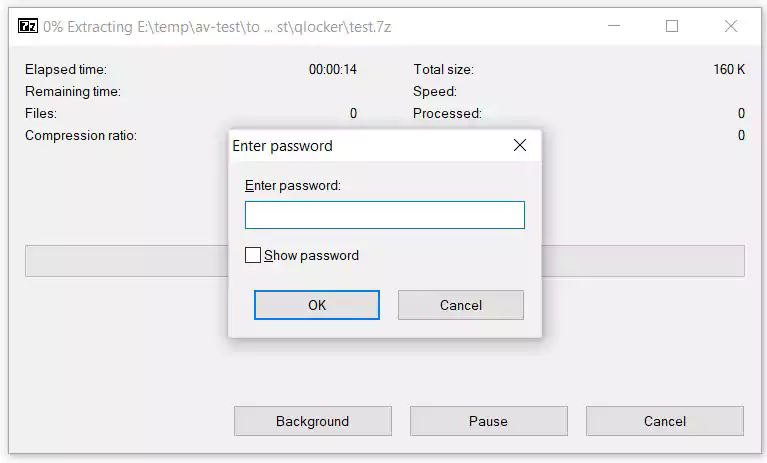
When the ransomware has finished, the QNAP device’s files will be stored in password-protected 7-zip archives ending with the .7z extension. To extract these archives, victims will need to enter a password known only to the attacker.
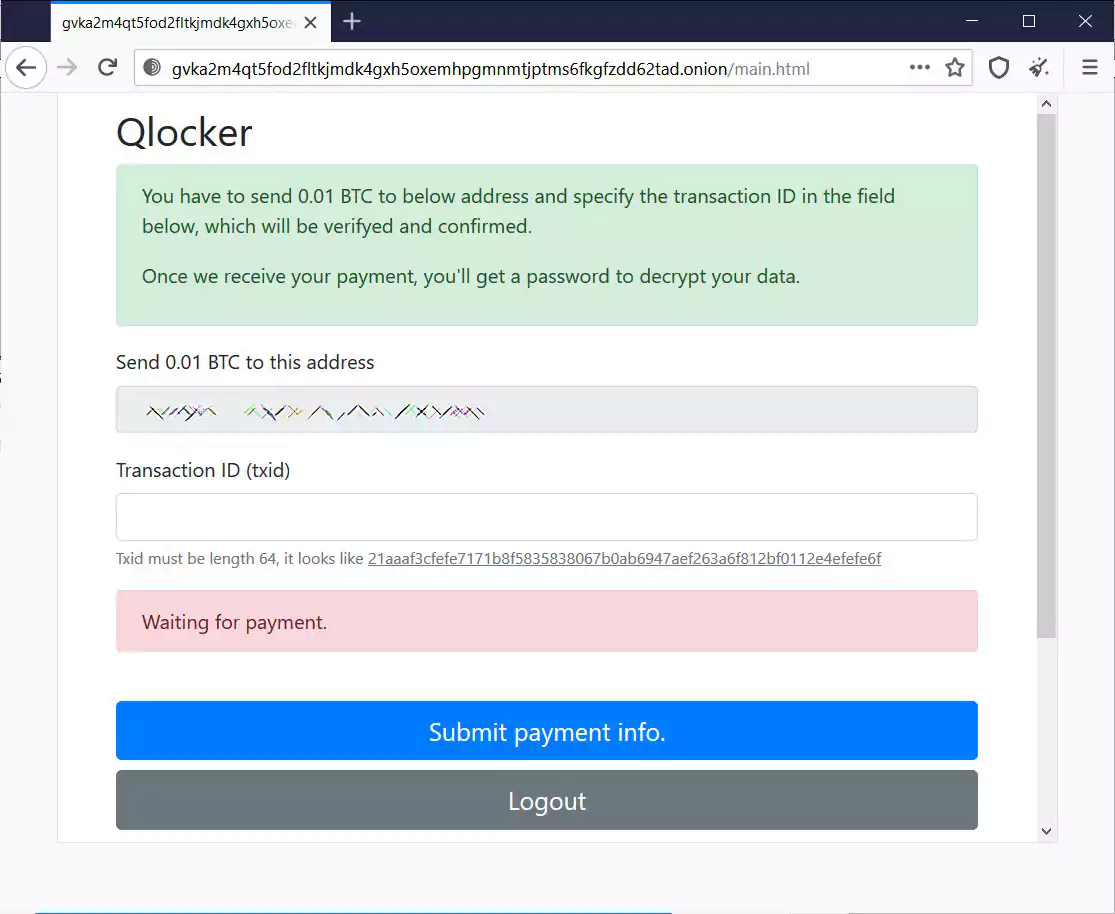
After QNAP devices are encrypted, users are left with a !!!READ_ME.txt ransom note that includes a unique client key that the victims need to enter to log into the ransomware’s Tor payment site.
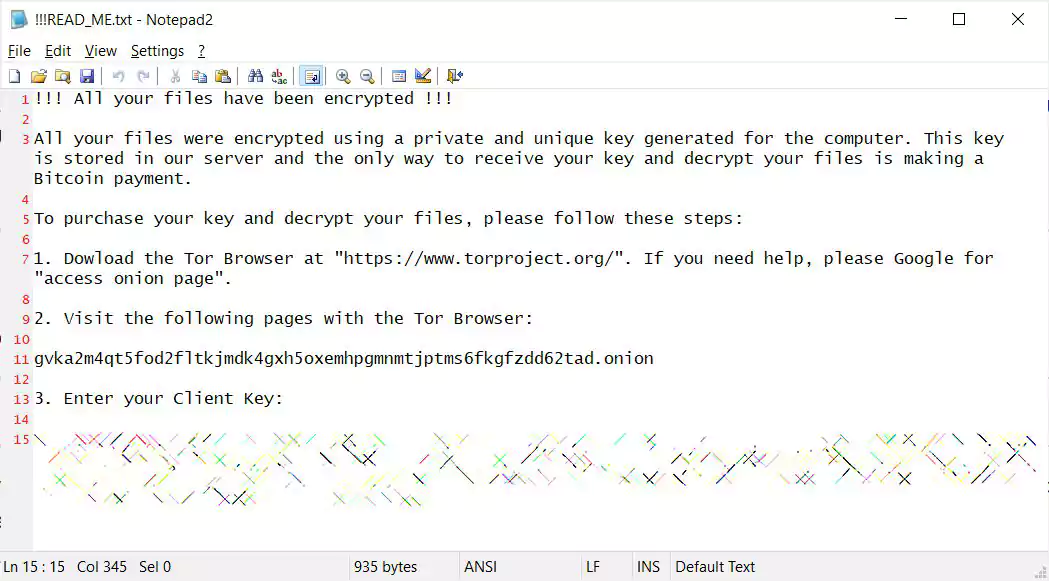
From the Qlocker ransom notes seen by BleepingComputer, all victims are told to pay 0.01 Bitcoins, which is approximately $557.74, to get a password for their archived files.
After paying the ransom and entering a valid Bitcoin transaction ID, the Tor payment site will display the password for the victim’s 7Zip archives, as shown below.
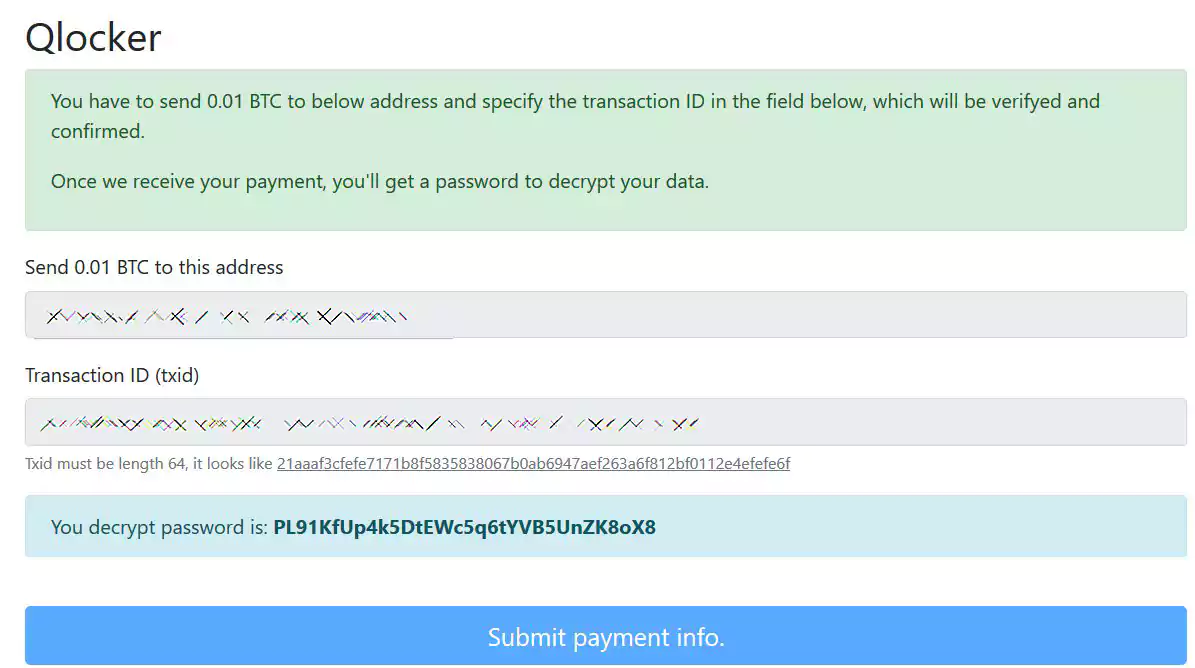
This password is unique to the victim and cannot be used on other victims’ devices.
Update 4/22/21 09:15 AM EST: Early this morning, BleepingComputer was contacted by security researcher Jack Cable about a bug he discovered in the Qlocker Tor site that allowed users to recover their 7zip passwords for free.
Using this bug, victims could take a Bitcoin transaction ID from a person who had already paid and slightly alter it. When they submitted the altered transaction ID into the Qlocker Tor site, it accepted it as payment and displayed the victim’s 7zip password.
Last night, Cable had been privately helping people recover their passwords and arrangements were being made with Emsisoft to create a help system to better exploit this weakness.
Sadly, an hour after we learned of the bug, the ransomware operators caught on and fixed it.
At this point, there is no way to recover the files without a password, which can no longer be retrieved for free.
Recently QNAP resolved critical vulnerabilities that could allow a remote actor to gain full access to a device and execute ransomware.
QNAP fixed these two vulnerabilities on April 16th with the following descriptions:
More information about these vulnerabilities can be found in a blog post by the SAM Seamless Network research team who disclosed the bugs to QNAP.
QNAP told BleepingComputer that they believe Qlocker exploits the CVE-2020-36195 vulnerability to execute the ransomware on vulnerable devices.
Due to this, it is strongly recommended to update QTS, Multimedia Console, and the Media Streaming Add-on to the latest versions.
“QNAP strongly urges that all users immediately install the latest Malware Remover version and run a malware scan on QNAP NAS. The Multimedia Console, Media Streaming Add-on, and Hybrid Backup Sync apps need to be updated to the latest available version as well to further secure QNAP NAS from ransomware attacks. QNAP is urgently working on a solution to remove malware from infected devices,” QNAP stated in a security advisory.
QNAP warns that if a device’s files have been encrypted already they should not reboot the device and instead immediately run the malware scanner.
“If user data is encrypted or being encrypted, the NAS must not be shut down. Users should run a malware scan with the latest Malware Remover version immediately, and then contact QNAP Technical Support at https://service.qnap.com/,” advises QNAP.
Also Read: Considering Enterprise Risk Management Certification Singapore? Here Are 7 Best Outcomes
While the malware scanner and security updates will not recover your files, it will protect you from future attacks using this vulnerability.
!!!READ_ME.txt!!! All your files have been encrypted !!!
All your files were encrypted using a private and unique key generated for the computer. This key is stored in our server and the only way to receive your key and decrypt your files is making a Bitcoin payment.
To purchase your key and decrypt your files, please follow these steps:
1. Dowload the Tor Browser at "https://www.torproject.org/". If you need help, please Google for "access onion page".
2. Visit the following pages with the Tor Browser:
gvka2m4qt5fod2fltkjmdk4gxh5oxemhpgmnmtjptms6fkgfzdd62tad.onion
3. Enter your Client Key:
[client_key]