KEEP IN TOUCH
Subscribe to our mailing list to get free tips on Data Protection and Cybersecurity updates weekly!






Google researchers spotted malware developers creating malformed code signatures seen as valid in Windows to bypass security software.
This tactic is actively used to push OpenSUpdater, a family of unwanted software also known as riskware, which injects ads into victims’ browsers and installs other unwanted programs onto their devices.
Campaigns coordinated by the financially motivated threat actors behind OpenSUpdater will attempt to infect as many devices as possible.
Most targets are from the US and likely interested in downloading game cracks and other potentially booby-trapped tools.
Also Read: How To Make A PDPC Complaint: With Its Importance And Impact
Roughly a month ago, Google Threat Analysis Group (TAG) security researcher Neel Mehta discovered that the developers of an unwanted software known as OpenSUpdater started signing their samples with legitimate but intentionally malformed certificates, accepted by Windows but rejected by OpenSSL.
By breaking certificate parsing for OpenSSL (which won’t be able to decode the digital signatures and check them), the malicious samples would not be detected by some security solutions that use OpenSSL-powered detection rules and allowed to perform their malicious tasks on victims’ PCs.
“Since mid-August, OpenSUpdater samples have carried an invalid signature, and further investigation showed this was a deliberate attempt to evade detection,” Mehta said.
“Security products using OpenSSL to extract signature information will reject this encoding as invalid.
“However, to a parser that permits these encodings, the digital signature of the binary will otherwise appear legitimate and valid.”
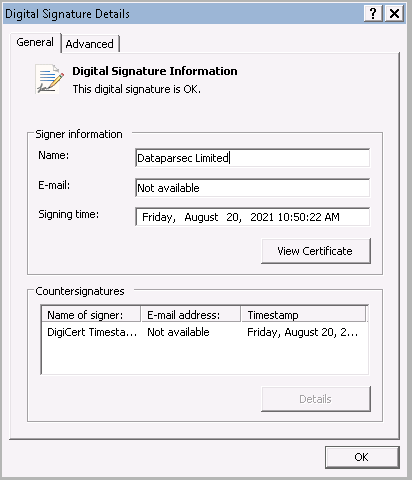
That last part is what allows OpenSUpdater to bypass security defenses, enabling samples deployed on a victim’s computer will be able to launch without issues.
This happens because security solutions that use OpenSSL to parse digital signatures will virtually ignore the samples’ malicious nature because they will reject the signature information as invalid, confusing and breaking the malware scan process.
“Since first discovering this activity, OpenSUpdater’s authors have tried other variations on invalid encodings to further evade detection,” Mehta added.
“This is the first time TAG has observed actors using this technique to evade detection while preserving a valid digital signature on PE files.”
After discovering the issue, the Google TAG researcher has also contacted Microsoft to report this detection evasion tactic.
Google TAG is currently working with the Google Safe Browsing team to block this family of unwanted software from further spreading onto other victims’ computers.
Also Read: Basic Info On How Long To Keep Accounting Records In Singapore?
The security research also urged Google users to download and install software only from trustworthy sources.