



The sophisticated hacking group known as StrongPity is circulating laced Notepad++ installers that infect targets with malware.
This hacking group, also known as APT-C-41 and Promethium, was previously seen distributing trojanized WinRAR installers in highly-targeted campaigns between 2016 and 2018, so this technique is not new.
The recent lure involves Notepad++, a very popular free text and source code editor for Windows used in a wide range of organizations.
The discovery of the tampered installer comes from a threat analyst known as ‘blackorbird’ analysts, while Minerva Labs reports on the malware.
Also Read: A Review of PDPC Undertakings July 2021 Cases
#APT #StrongPity NotePad++ installer(npp.8.1.7.Installer.x64.exe)
78556a2fc01c40f64f11c76ef26ec3ff
http[:]//advancedtoenableplatform.com pic.twitter.com/eEXZWIObnH— blackorbird (@blackorbird) November 30, 2021
Upon executing the Notepad++ installer, the file creates a folder named “Windows Data” under C:\ProgramData\Microsoft, and drops the following three files:
The installation of the code editor continues as expected, and the victim won’t see anything out of the ordinary that could raise suspicions.
As the setup finishes, a new service named “PickerSrv” is created, establishing the malware’s persistence via startup execution.
Also Read: Protecting Data Online in the New Normal
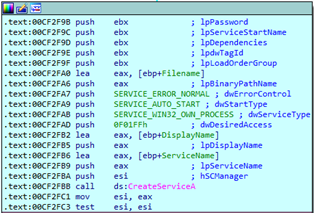
This service executes ‘ntuis32.exe’, which is the keylogger component of the malware, as an overlapped window (using WS_MINIMIZEBOX style).
The keylogger records all user keystrokes and saves them to hidden system files dumped created in the ‘C:\ProgramData\Microsoft\WindowsData’ folder. The malware also has the ability to steal files and other data from the system.
This folder is continuously checked by ‘winpickr.exe,’ and when a new log file is detected, the component establishes a C2 connection to upload the stolen data to attackers.
Once the transfer has been completed, the original log is deleted to wipe the traces of malicious activity.
If you need to use Notepad++, make sure to source an installer from the project’s website.
The software is available on numerous other websites, some of which claim to be the official Notepad++ portals but may include adware or other unwanted software.
The URL that was distributing the laced installer has been taken down following its identification by analysts, but the actors could quickly register a new one.
Follow the same precautions with all software tools you’re using, no matter how niche they are, as sophisticated actors are particularly interested in specialized software cases that are ideal for watering hole attacks.
In this case, the chances of detection from an AV tool on the system would be roughly 50%, so using up-to-date security tools is essential too.