KEEP IN TOUCH
Subscribe to our mailing list to get free tips on Data Protection and Cybersecurity updates weekly!







Multiple malware authors are using the “Ezuri” crypter and memory loader to make their code undetectable to antivirus products.
Source code for Ezuri, written in Golang, is available on GitHub for anyone to use.
According to a report released by AT&T Alien Labs, multiple threat actors are using Ezuri crypter to pack their malware and evade antivirus detection.
Although Windows malware have been known to deploy similar tactics, threat actors are now using Ezuri for infiltrating Linux environments as well.
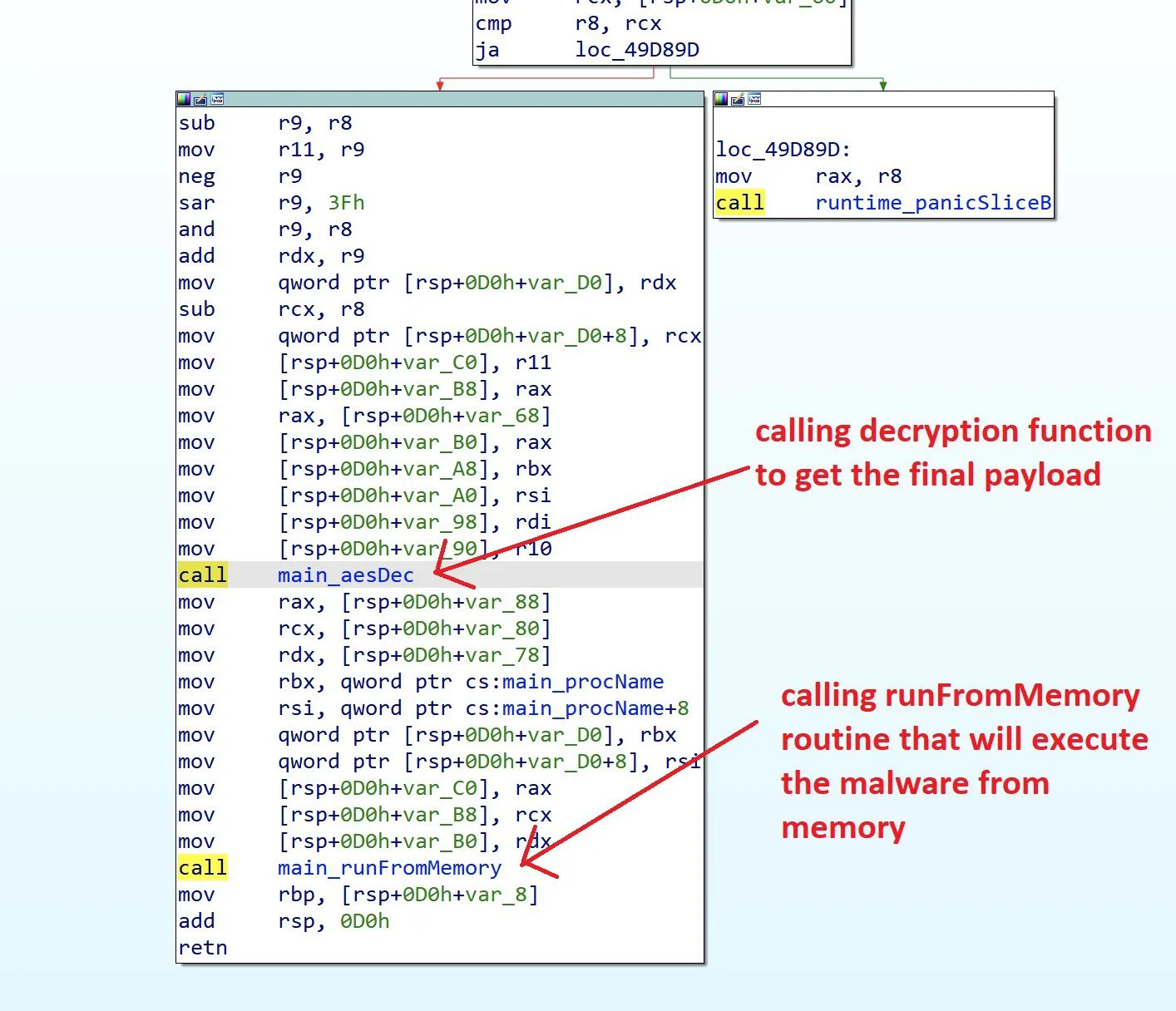
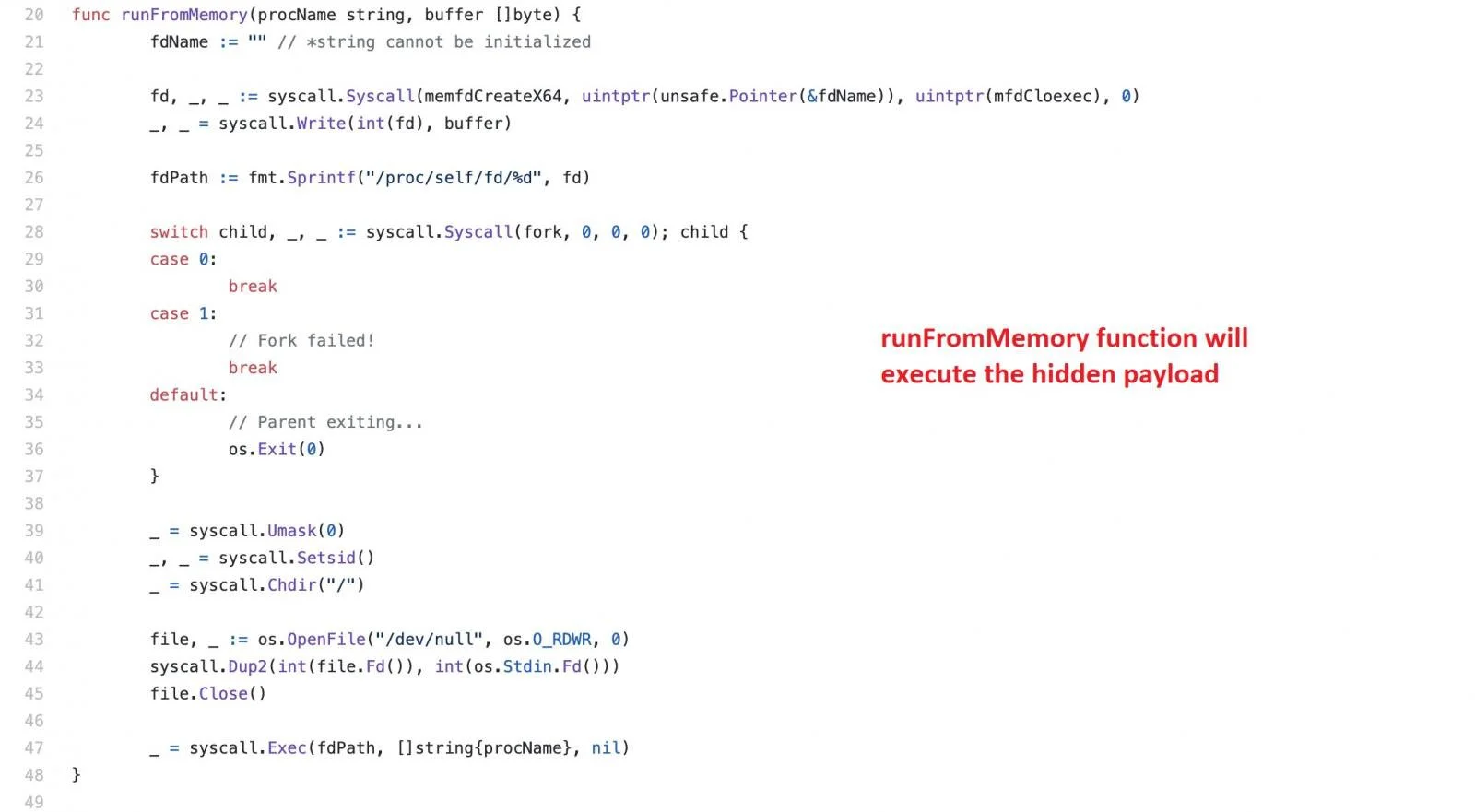
Written in Go, Ezuri acts both as a crypter and loader for ELF (Linux) binaries. Using AES, it encrypts the malware code and, on decryption, executes the malicious payload directly within memory without generating any files on the disk.
Also Read: What Do 4 Messaging Apps Get From You? Read The iOS Privacy App Labels
Systems engineer and Ezuri’s creator, Guilherme Thomazi Bonicontro (‘guitmz’), had open-sourced the ELF loader on GitHub in 2019 and debuted the tool in his blog post.
In an email interview, Bonicontro aka TMZ shared with BleepingComputer that he is a malware researcher and creates research tools for spreading awareness and helping defenders.
“I’m an independant malware researcher, I do this as one of my hobbies only. The goal of my work is simply to learn and bring awareness on diverse PoC attack and defense techniques, but never cause any damage. As a rule of thumb, I always share samples of my projects with antivirus companies and I never release code with destructive payload or anything with sophisticated replication capabilities. I believe knowledge should be accessible to everyone and each individual should be responsible for their own actions to sleep well at night.”
“Unfortunately, if anything, this reinforces the fact that the security industry needs to invest more on Linux threat detection and that threat actors are more active than ever,” Bonicontro told BleepingComputer.
Researchers Ofer Caspi and Fernando Martinez of AT&T Alien Labs noted after decrypting the AES-encrypted payload, Ezuri immediately passes the resulting code to the runFromMemory function as an argument without dropping malware files anywhere on the infected system.
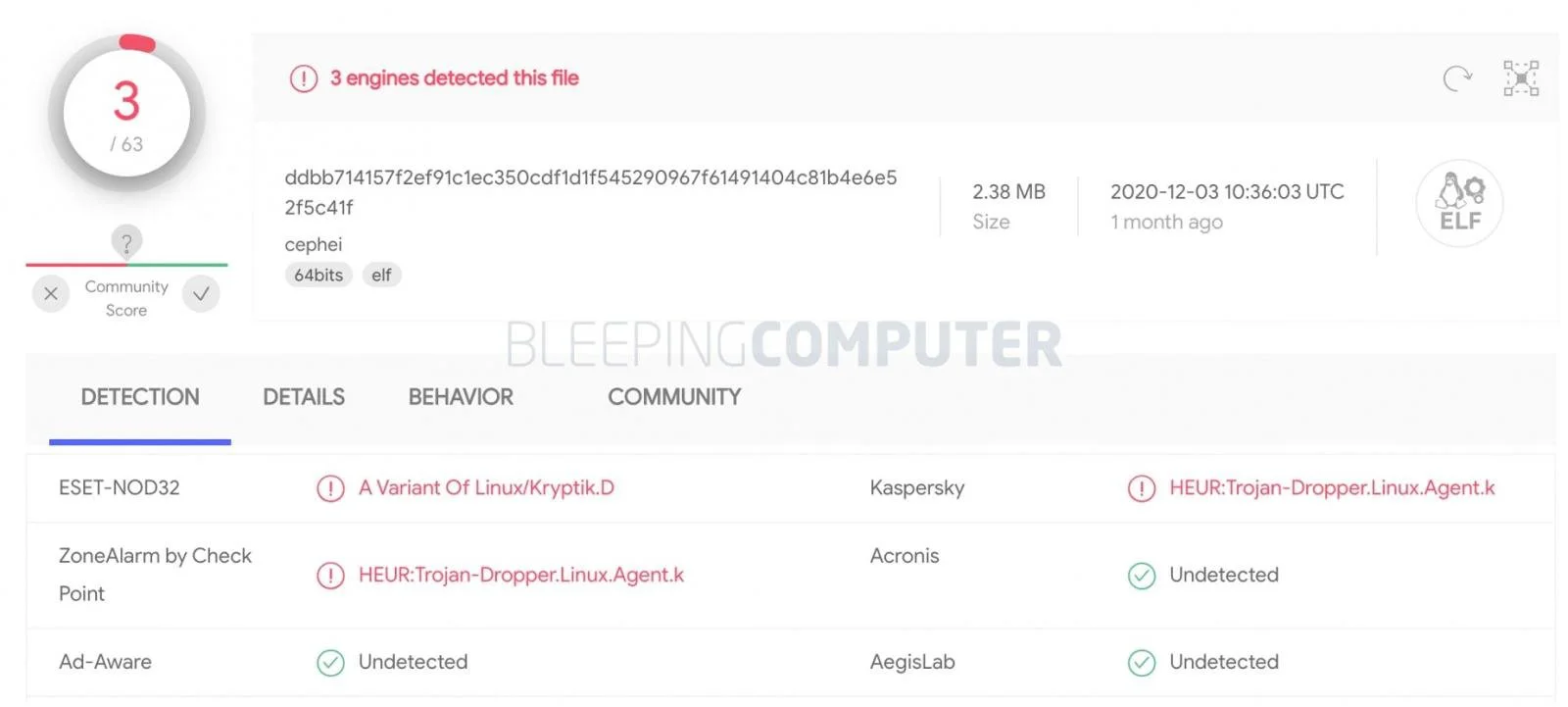
Malware samples which were typically detected by about 50% of antivirus engines on VirusTotal, yielded 0 detections when encrypted with Ezuri, at the time of AT&T’s research.
Even today, as observed by BleepingComputer, the Ezuri-packed sample has less than a 5% detection rate on VirusTotal.
Also Read: Key PDPA Amendments 2019/2020 You Should Know
During the last few months, Caspi and Martinez identified several malware authors that pack their samples with Ezuri.
These include the cybercrime group, TeamTnT, active since at least April 2020.
TeamTnT is known to attack misconfigured Docker instances and exposed APIs to turn vulnerable systems into DDoS bots and cryptominers.
Later variants of TeamTnT’s malware, such as “Black-T” that install network scanners on infected systems and extract AWS credentials from memory were also found to be laced with Ezuri.
According to the AT&T researchers, “the last [Black-T] sample identified by Palo Alto Networks Unit42 is actually an Ezuri loader.”
“The decrypted payload is an ELF file packed with UPX, which is a known sample from TeamTNT, first seen in June 2020.”
The researchers also noticed the presence of the ‘ezuri’ string in multiple Ezuri-packed binaries.
Ezuri’s Indicators of Compromise (IOCs), YARA detection rules, and more information can be found in the blog post published by AT&T Alien Labs.
Additionally, Craig H. Rowland of Sandfly Security has provided tips on how to detect and mitigate Linux fileless malware like these in your environment.
Update 7-Jan-2020: Added statement from malware researcher and Ezuri creator, Bonicontro/TMZ