KEEP IN TOUCH
Subscribe to our mailing list to get free tips on Data Protection and Cybersecurity updates weekly!







An Internet Explorer zero-day vulnerability has been discovered used in recent North Korean attacks against security and vulnerability researchers.
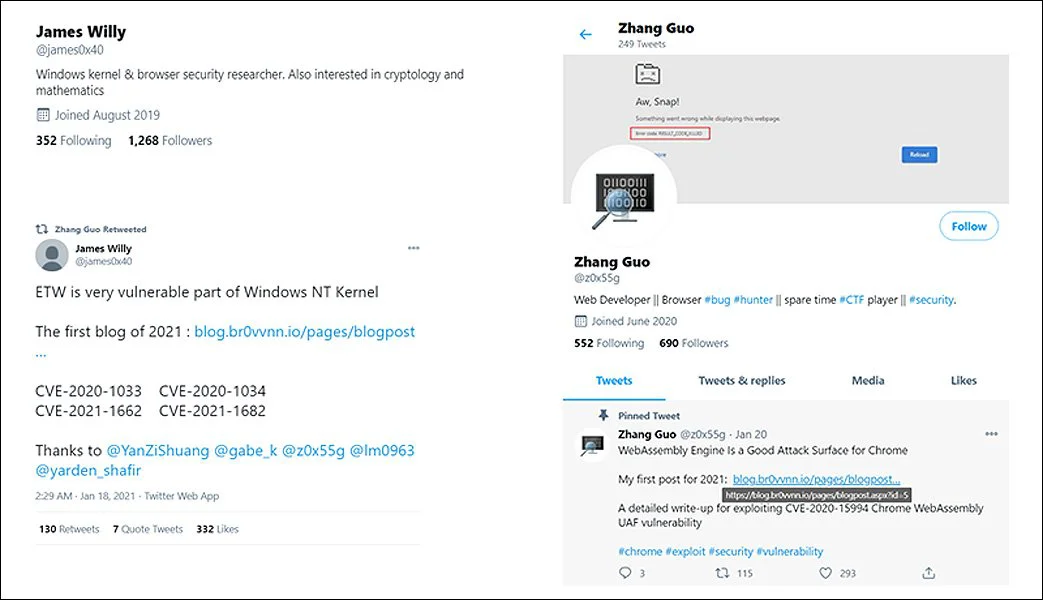
Last month, Google disclosed that the North Korean state-sponsored hacking group known as Lazarus was conducting social engineering attacks against security researchers.
To perform their attacks, the threat actors created elaborate online ‘security researcher’ personas that would then use social media to contact well-known security researchers to collaborate on vulnerability and exploit development.
As part of this collaboration, the attackers sent malicious Visual Studio Projects and links to websites hosting exploit kits that would install backdoors on the researcher’s computers.
Microsoft also reported they had been tracking the attack and had seen Lazarus sending MHTML files to researchers containing malicious javascript. At the time of their investigation, the command and control server was down, and Microsoft could not investigate further payloads.
Also Read: Limiting Location Data Exposure: 8 Best Practices
Today, South Korean cybersecurity firm ENKI reported that Lazarus targeted security researchers on their team with MHTML files in this social engineering campaign.
While they state that the attacks failed, they analyzed the payloads downloaded by the MHT file and discovered it contained an exploit for an Internet Explorer zero-day vulnerability.
An MHT/MHTML file, otherwise known as MIME HTML, is a special file format used by Internet Explorer to store a web page and its resources in a single archive file.
The MHT file sent to ENKI researchers contained what was allegedly a Chrome 85 RCE exploit and was named ‘Chrome_85_RCE_Full_Exploit_Code.mht.’
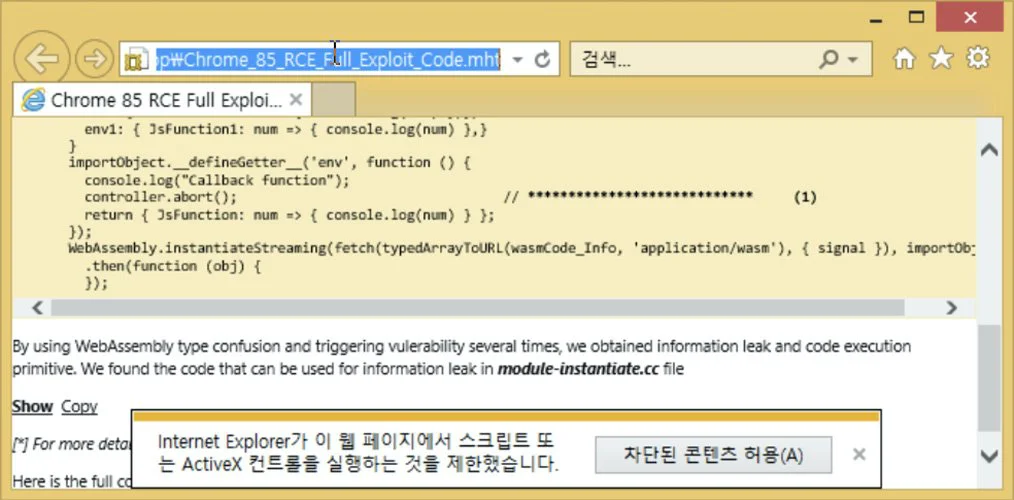
When the MHT/MHTML file was opened, Internet Explorer automatically launched to display the contents of the MHT file. If script execution was allowed, ENKI says that malicious javascript would download two payloads, with one containing a zero-day against Internet Explorer.
This exploit abuses a double-free bug in IE 11, allowing the attackers to upload a list of the running process, screen captures, and network information to their command and control server. It would then download and execute additional malicious code from the C2 server to be executed.
ENKI told BleepingComputer that they have reported the bug to Microsoft and were later contacted by a Microsoft employee requesting more information.
Acros CEO and 0patch co-founder Mitja Kolsek told BleepingComputer that he was able to reproduce the Internet Explorer zero-day PoC reported by ENKI.
Based on tweets from other security researchers, ENKI told BleepingComputer that they believe other researchers know of this IE 11 zero-day.
Microsoft told BleepingComputer that they investigate every report and will provide an update in the future.
Also Read: 10 Practical Benefits of Managed IT Services
“Microsoft has a customer commitment to investigate reported security issues and we will provide updates for impacted devices as soon as possible.”- a Microsoft spokesperson.