KEEP IN TOUCH
Subscribe to our mailing list to get free tips on Data Protection and Cybersecurity updates weekly!





Security researchers discovered that attackers are also deploying a Linux backdoor on compromised e-commerce servers after injecting a credit card skimmer into online shops’ websites.
The PHP-coded web skimmer (a script designed to steal and exfiltrate customers’ payment and personal info) is added and camouflaged as a .JPG image file in the /app/design/frontend/ folder.
The attackers use this script to download and inject fake payment forms on checkout pages displayed to customers by the hacked online shop.
“We found that the attacker started with automated eCommerce attack probes, testing for dozens of weaknesses in common online store platforms,” the Sansec Threat Research Team revealed.
Also Read: 5 Best Practices About Information Retention For Businesses
“After a day and a half, the attacker found a file upload vulnerability in one of the store’s plugins. S/he then uploaded a webshell and modified the server code to intercept customer data.”
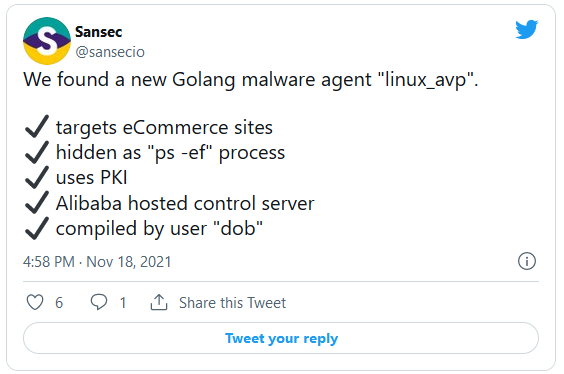
The Golang-based malware, spotted by Dutch cyber-security company Sansec on the same server, was downloaded and executed on breached servers as a linux_avp executable.
Once launched, it immediately removes itself from the disk and camouflages itself as a “ps -ef” process that would be used to get a list of currently-running processes.
Also Read: Employment Application Template: What Information Required
While analyzing the linux_avp backdoor, Sansec found that it waits for commands from a Beijing server hosted on Alibaba’s network.
They also discovered that the malware would gain persistence by adding a new crontab entry that would redownload the malicious payload from its command-and-control server and reinstall the backdoor if detected and removed or the server restarts.
Until now, this backdoor remains undetected by anti-malware engines on VirusTotal even though a sample was first uploaded more than one month ago, on October 8th.
The uploader might be the linux_avp creator since it was submitted one day after researchers at Dutch cyber-security company Sansec spotted it while investigating the e-commerce site breach.