KEEP IN TOUCH
Subscribe to our mailing list to get free tips on Data Protection and Cybersecurity updates weekly!







The authors of a cryptocurrency-stealing malware are distributing it over Telegram to aspiring cybercriminals under the guise of free malicious applications.
Researchers have named the malware HackBoss and say that its operators likely stole more than $500,000 from wannabe hackers that fell for the trick.
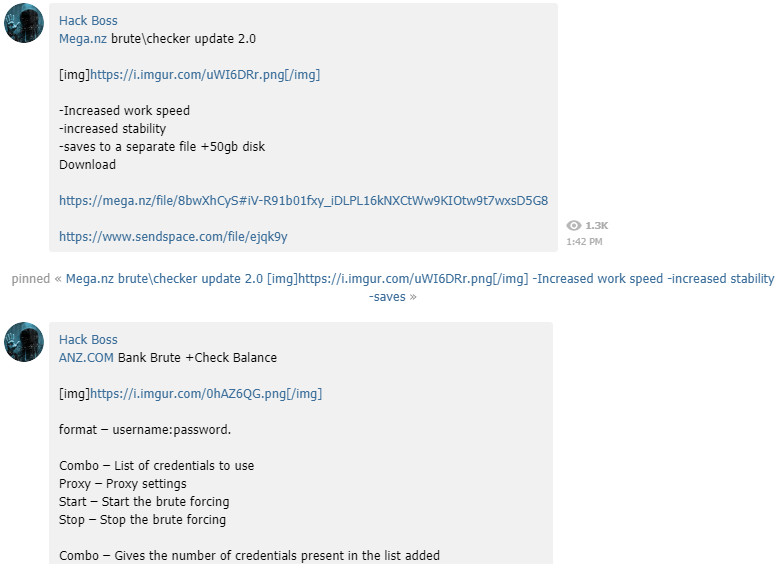
Although there is nothing sophisticated about HackBoss, the scheme proves to be effective as it tempts victims with the prospect of getting hacking tools, mostly for brute-forcing passwords for banking, dating, and social media accounts.
Researchers at Avast analyzing HackBoss note that the malware is packed in a .ZIP file with an executable that launches a simple user interface.
Regardless of the options available, the UI’s single purpose is to add the decrypt and execute the cryptocurrency-stealing malware on the victim’s system.
Also Read: 4 Best Practices On How To Use SkillsFuture Credit
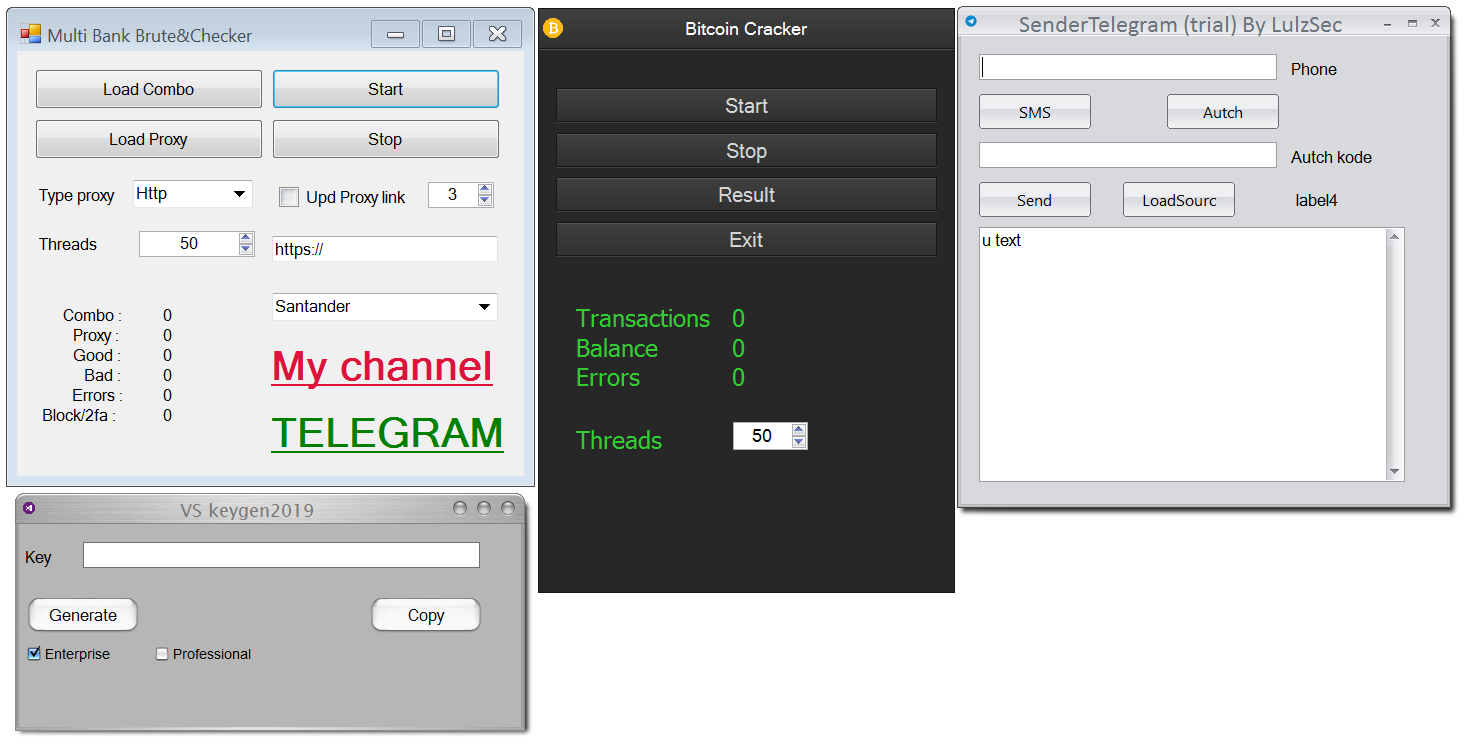
This occurs when clicking any button in the fake interface. The action can also give HackBoss persistence on the system by setting up a registry key to run it at startup or by adding a scheduled task that runs the payload every minute.
“The malicious payload keeps running on the victim’s computer even after the application’s UI is closed. If the malicious process is terminated — for example via the Task manager — it can then get triggered again on startup or by the scheduled task in the next minute”
– Avast
As for the functionality, there’s no complexity to it. The malware is designed to simply check the clipboard for a cryptocurrency wallet and replace it with one belonging to the attacker.
When the victim initiates a cryptocurrency payment and copies the recipient’s wallet, HackBoss quickly replaces it, taking advantage of the fact that few users check the string before hitting the pay button.
Despite the simple functions, maintaining the cover of a hacking tool distributor requires some effort as each post comes with a bogus description to make it a believable offer.
But the endeavor appears to be profitable. Avast researchers say in a blog post today that they found over 100 cryptocurrency wallet addresses associated with the HackBoss operation that received more than $560,000 since November 2018.

Not all the funds came from the cryptocurrency-stealing malware though as there some of the addresses have been reported in scams that tricked victims into buying fake software.
Data from the Telemetrio service for Telegram and chat statistics shows that the Hack Boss channel has about nine posts per month, each with more than 1,300 views and that it grew to more than 2,800 subscribers.

Avast researchers say that HackBoss authors also promote their fake hacking tools outside the Telegram channel, although this remains the main distribution path.
One avenue is a blog (cranhan.blogspot[.]com) that advertises fake tools, provides promo videos, and also posts ads on public forums and discussions.
Also Read: 3 Reasons Why You Must Take A PDPA Singapore Course
Avast provides a lengthy list of indicators of compromise on its GitHub page with hashes and names of the fake applications disguising HackBoss malware and the cryptocurrency wallet addresses (Bitcoin, Ethereum, Litecoin, Monero, Dogecoin) associated with the actor.