





Google today announced that the company’s Vulnerability Reward Program has expanded to also include bug reports on methods threat actors can use to bypass the company’s abuse, fraud, and spam systems.
“A few examples of potentially valid reports for this program could include bypassing our account recovery systems at scale, identifying services vulnerable to brute force attacks, circumventing restrictions on content use and sharing, or purchasing items from Google without paying,” Google’s Eric Brown and Marc Henson said.
Reports highlighting such abuse techniques submitted to the Google Vulnerability Reward Program (VRP) will be reviewed by the company’s Trust & Safety team whose experts are specialized in preventing and mitigating abuse, fraud, and spam activity across Google’s product platforms.
“This program does not cover individual instances of abuse, such as the posting of content that violates our guidelines or policies, sending spam emails, or providing links to malware,” they added.
Valid reports reaching Google’s Trust & Safety team will most likely result in code changes designed to make sure that the technique used to bypass the company’s anti-fraud systems won’t be usable in the future.
Therefore, reports focused on outlining a specific instance of an abuse method being used to circumvent Google’s platform abuse prevention systems should be instead submitted using product-specific channels, including but not limited to Google+, YouTube, Gmail, and Blogger.
Also read: Does Personal Data Market About To Become The Next Big Thing
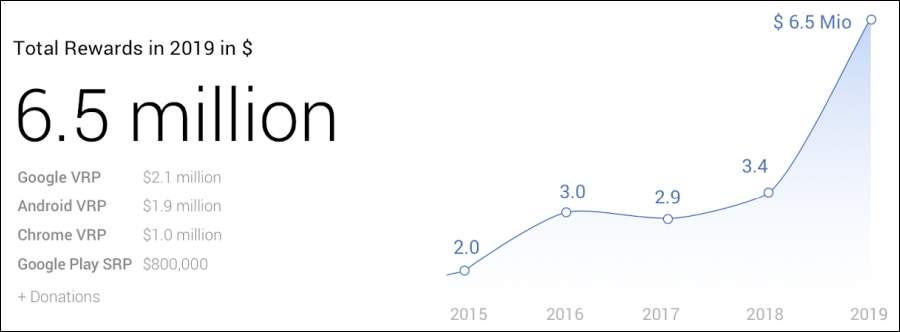
Starting with 2010, Google has paid more than $12 million to security researchers through its VRP, with $6.5 million — more than half of the total amount — having been awarded in 2019 alone.
The amount paid in VRP rewards by Google has almost doubled during 2019 when compared to the $3.4 million paid in 2018 or the total amount paid every single year since the Google VRP program was launched.
Reward amounts paid for qualifying bugs through Google’s VRP now range from $100 to $31,337, but the total amount rewarded can drastically increase for submitted exploit chains.
This is exactly what happened in the case of Alpha Lab’s Guang Gong who got a $201,337 payout for a remote code execution exploit chain targeting Pixel 3 devices.
In total, Google awarded 461 security researchers for their reports during 2019 alone, with Gong’s over $201,000 reward being the biggest single payout ever.
Also read: The Importance Of DPIA And Its 3 Types Of Processing