KEEP IN TOUCH
Subscribe to our mailing list to get free tips on Data Protection and Cybersecurity updates weekly!







The Federal Bureau of Investigation (FBI) has released some technical details and indicators of compromise associated with Hive ransomware attacks.
In a rare occurrence, the FBI has included the link to the leak site where the ransomware gang publishes data stolen from companies that did not pay.
Hive ransomware relies on a diverse set of tactics, techniques, and procedures, which makes it difficult for organizations to defend against its attacks, the FBI says.
Among the methods that the gang uses to gain initial access and to move laterally on the network, there are phishing emails with malicious attachments and the Remote Desktop Protocol (RDP).
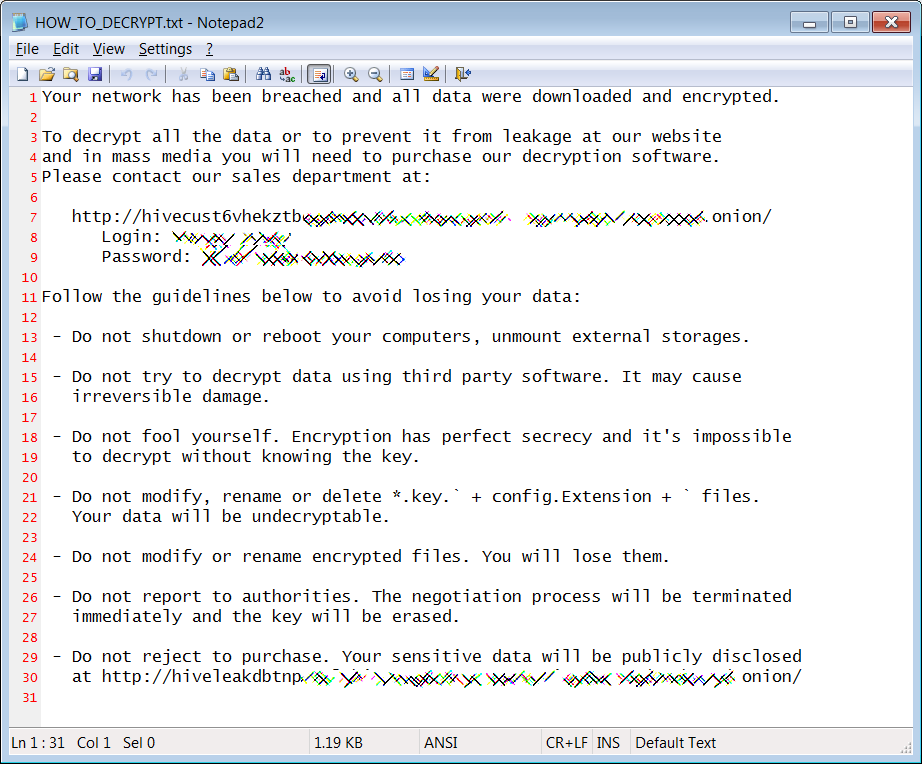
Before deploying the encryption routine, the Hive ransomware steals files they deem valuable, to pressure the victim to pay the ransom under the threat of a data leak.
The FBI says that the threat actor searches for processes for backups, file copying, and security solutions (like Windows Defender) that would hinder the data encryption task and terminates them.
This stage is followed by dropping a hive.bat script that performs a cleanup routine by removing itself after deleting the Hive malware executable.
Another script called shadow.bat is tasked with deleting shadow copies, backup files, and system snapshots and then removes itself from the compromised host.
The FBI says that some Hive ransomware victims reported being contacted by the attacker asking them to pay the ransom in exchange for the stolen files.
Also Read: Vulnerability Management For Cybersecurity Dummies
“The initial deadline for payment fluctuates between 2 to 6 days, but actors have prolonged the deadline in response to contact by the victim company,” the agency notes in its Flash bulletin.
Along with indicators of compromise (IoCs), the FBI also provides a link to the threat actor’s leak site, a detail that is typically hidden in technical reports.
Some of the files observed in Hive ransomware attacks include the following:
The FBI notes that the threat actor also relies on file-sharing services, many of them anonymous, like Anonfiles, MEGA, Send.Exploit, Ufile, or SendSpace.
Although it was first observed in late June, Hive ransomware has already breached more than 30 organizations this summer, a count that includes only victims that refused to pay the ransom.
A recent victim of Hive ransomware is Memorial Health System, which offers a network of services that includes three hospitals and providers representing 64 clinics.
From files seen by BleepingComputer, the attacker stole databases containing information belonging to more than 200,000 patients.
Also Read: Compliance With Singapore Privacy Obligations; Made Easier!
The FBI does not recommend paying the threat actors to discourage then from continuing the activity. Furthermore, there is no guarantee that the attacker will destroy the stolen data instead of selling it or giving it to fellow criminals.
Regardless of ransomware victim’s decision to pay or not, the FBI urges companies to report ransomware incidents to the local field office to help investigators with critical information to track the attackers, “hold them accountable under US law, and prevent future attacks.”