KEEP IN TOUCH
Subscribe to our mailing list to get free tips on Data Protection and Cybersecurity updates weekly!







Ransomware-as-a-service (RaaS) crews are actively looking for affiliates to split profits obtained in outsourced ransomware attacks targeting high profile public and private organizations.
RaaS services are viewed by some as ransomware renting service where the threat actors who breach the targets’ networks pay a fee to use the RaaS crew’s malware. In reality, only the lowest quality ransomware is rented, or sold, in this manner.
The more well-known ransomware gangs run private affiliate programs where affiliates can submit applications and resumes to apply for membership.
For affiliates that are accepted into the program, the ransomware developers receive a 20-30% cut, and an affiliate gets 70-80% of the ransom payments they generate.
To encrypt victims’ systems, affiliates will request the services of a hacker who gains access to the targets’ networks, gets domain admin privileges, harvests and exfiltrates files, and then passes all the info needed to gain access and encrypt data back to the affiliates.
Also Read: By Attending This Event You Agree To Be Photographed
The profits originating out of the paid ransoms following each of the attacks will then be split between the RaaS crew, the hackers who breached the network (compromiser), and the ransomware affiliate, usually in equal shares.
At the moment, there are over two dozen active ransomware-as-a-service gangs that are actively looking to outsource extortion attacks to ransomware affiliates.
As threat intelligence firm Intel 471 says in a report published earlier today, there are also “known private gangs operating in tight, close-knit criminal circles using direct and private communication channels that we have little visibility into.”
The ransomware gangs Intel 471 observed during the last year can be classified into three different groups (or tiers) based on their notoriety and the time they’ve been active for.
They range “from well-known groups that have become synonymous with ransomware, to newly-formed variants that have risen from the failures of old, to completely new variants that may have the ability to unseat the current top-level cabals.”
TIER 1 ransomware gangs are groups who have successfully raked in hundreds of millions in ransoms over the last years.
The vast majority of them are also using additional extortion schemes such as stealing sensitive information from their victims’ networks and threatening to leak it unless the ransom is paid.
RaaS crews included in the TIER 1 group are DopplePaymer (used in attacks on Pemex, Bretagne Télécom, Newcastle University, Düsseldorf University), Egregor (Crytek, Ubisoft, Barnes & Noble), Netwalker/Mailto (Equinix, UCSF, Michigan State University, Toll Group), and REvil/Sodinokibi (Travelex, New York airport, Texas local govt).
Ryuk is at the top of the rankings, with its payloads being detected in roughly one in three ransomware attacks during the last year.
The group is also known for delivering their payloads as part of multi-stage attacks using Trickbot, Emotet, and BazarLoader infection vectors for an easy way into their targets’ networks.
Ryuk affiliates have also been behind a huge wave of attacks on the U.S. healthcare system and for pulling in huge ransom payments, having collected $34 million from a single victim earlier this year.
TIER 2 RaaS operations have slowly grown to a larger number of affiliates during 2020 and were involved in several confirmed attacks.
Ransomware groups included in this tier are SunCrypt, Conti, Clop, Ragnar Locker, Pysa/Mespinoza, Avaddon, DarkSide (believed to be a splinter of REvil), and more.
Just as the TIER 1 ransomware gangs, they are also using the data theft extortion tactic as a secondary extortion method.
Also Read: What Legislation Exists in Singapore Regarding Data Protection and Security?
| Name | Date Discovered | Attack claims | Markets Sold | Leak blog |
|---|---|---|---|---|
| Avaddon | March 2020 | Under 10 | Exploit | Yes |
| Conti | August 2020 | 142 | Private | Yes |
| Clop | March 2020 | Over 10 | N/A | Yes |
| DarkSide | August 2020 | Under 5 | Exploit | Yes |
| Pysa/Mespinoza | August 2020 | Over 40 | N/A | Yes |
| Ragnar | December 2019 | Over 25 | Exploit | Yes |
| Ranzy | October 2020 | 1 | Exploit & XSS | Yes |
| SunCrypt | October 2019 | Over 20 | Mazafaka | Yes |
| Thanos | August 2020 | Over 5 | Raid | No |
TIER 3 RaaS crews are offering newly created to affiliates but, according to Intel 471, “there is limited to no information on successful attacks, volume of attacks, payments received or cost of mitigation.”
The groups tagged as emerging TIER 3 gangs include Nemty, Wally, XINOF, Zeoticus, CVartek.u45, Muchlove, Rush, Lolkek, Gothmog, and Exorcist.
| Name | Date Discovered | Notable Incidents | Markets Sold | Leak blog |
|---|---|---|---|---|
| CVartek.u45 | March 2020 | None | Torum | No |
| Exorcist | July 2020 | None | XSS | No |
| Gothmog | July 2020 | None | Exploit | No |
| Lolkek | July 2020 | None | XSS | No |
| Muchlove | April 2020 | None | XSS | No |
| Nemty | February 2020 | 1 | XSS | Yes |
| Rush | July 2020 | None | XSS | No |
| Wally | February 2020 | None | Nulled | No |
| XINOF | July 2020 | None | Private Telegram channel | No |
| Zeoticus | 1.0 Dec. 2019, 2.0 Sept 2020 | None | XSS/Private channels | No |
Besides the ransomware gangs listed by Intel 471 as actively seeking partners, BleepingComputer is also aware of other big and emerging RaaS crews.
For instance, Dharma is a long-running RaaS that has been around since 2017 and known as an offshoot of Crysis ransomware, which started operating in 2016.
Dharma does not use data leak sites and there are not wide reports of data being stolen. The ransoms their affiliates collect can range from thousands to hundreds of thousands of U.S. dollars.
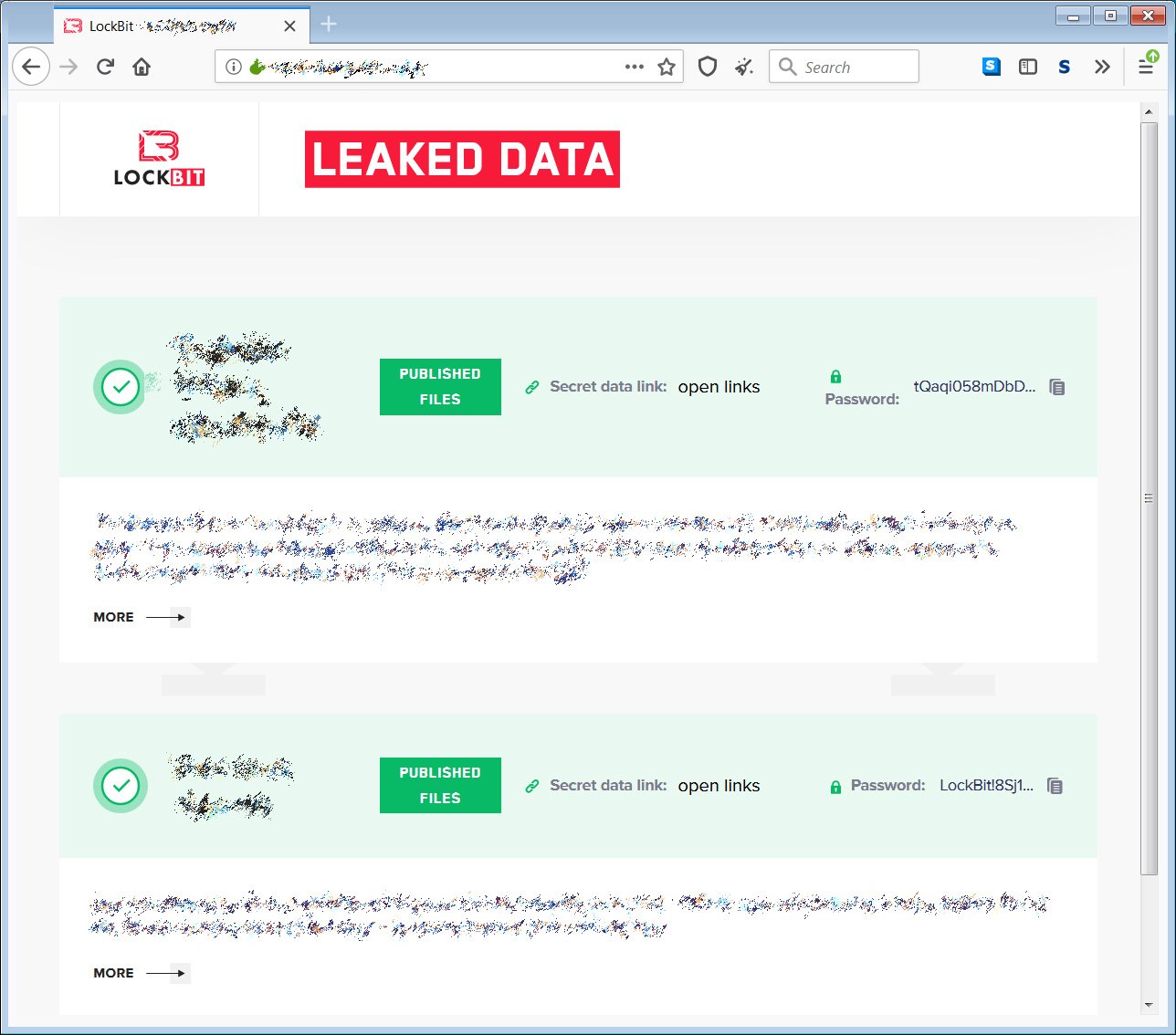
LockBit, another high-profile RaaS operation, surfaced in September 2019 as a private operation targeting enterprises and later observed by Microsoft while used in attacks healthcare and critical services.
The LockBit gang partnered with Maze to create an extortion cartel to share the same data leak platform during attacks, as well as to exchange tactics and intelligence.
LockBit ransomware actors also take as little as five minutes to deploy payloads after gaining access to the victim network.
Other RaaS operations left outside of Intel 471’s tiers are Ragnarok, CryLock, ProLock, Nefilim, and Mount Locker, with all of them known to be active and involved in recent attacks.