





The DarkSide ransomware gang posted a new “press release” today stating that they are apolitical and will vet all targets before they are attacked.
Last week, the ransomware gang encrypted the network for the Colonial Pipeline, the largest fuel pipeline in the United States.
FBI Statement on Compromise of Colonial Pipeline Networks https://t.co/XxHgezpref pic.twitter.com/McrRFOil64
— FBI (@FBI) May 10, 2021
Due to the attack, Colonial shut down its network and the fuel pipeline while recovering from the cyberattack.
As this pipeline transports 2.5 million barrels of refine fuel per day and provides 45% of all fuel consumed on the East Coast, the US government issued a state of emergency for 18 states affected by the ransomware incident.
Also Read: Practitioner Certificate In Personal Data Protection: Everything You Need To Know
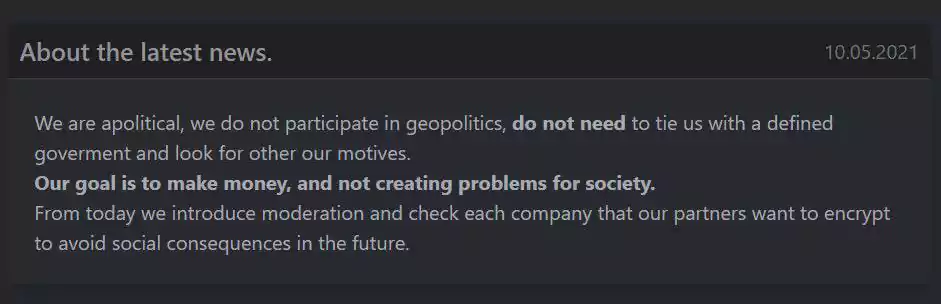
Today, the DarkSide ransomware gang issued a press statement stating that their organization is ‘apolitical’ and is not associated with any government.
“We are apolitical, we do not participate in geopolitics, do not need to tie us with a defined goverment and look for other our motives.
Our goal is to make money, and not creating problems for society.
From today we introduce moderation and check each company that our partners want to encrypt to avoid social consequences in the future.” – DarkSide gang.
DarkSide is operated as a Ransomware-as-a-Service, which consists of two groups of people. One group is the core operators and developers of the ransomware, and the other is its affiliates that are recruited to hack networks and deploy the ransomware.
As part of this arrangement, the core operators earn approximately 20-30% of any ransom payment, and the rest goes to the affiliate.
RaaS operations are typically free-for-alls where affiliates can attack whoever they want, and the core operators simply develop the ransomware, handle negotiations, and accept ransom payments.
Realizing that one of their affiliates picked the wrong target with Colonial Pipeline, the core DarkSide team says that they will now evaluate all targets before they allow an affiliate to perform an attack.
If true, this is a good thing for critical infrastructure, healthcare, and government agencies, as it is likely DarkSide will pass on attacking these entities in the future. However, this could lead to affiliates switching to other ransomware operations with fewer scruples about who they attack.
For a ransomware operation that is considered to be run professionally and with more ethics than other operations, they also tend to make press statements that don’t always go so well.
In October 2020, DarkSide announced that they donated $20,000 of their ill-gotten bitcoins to the Children International and The Water Project charities.
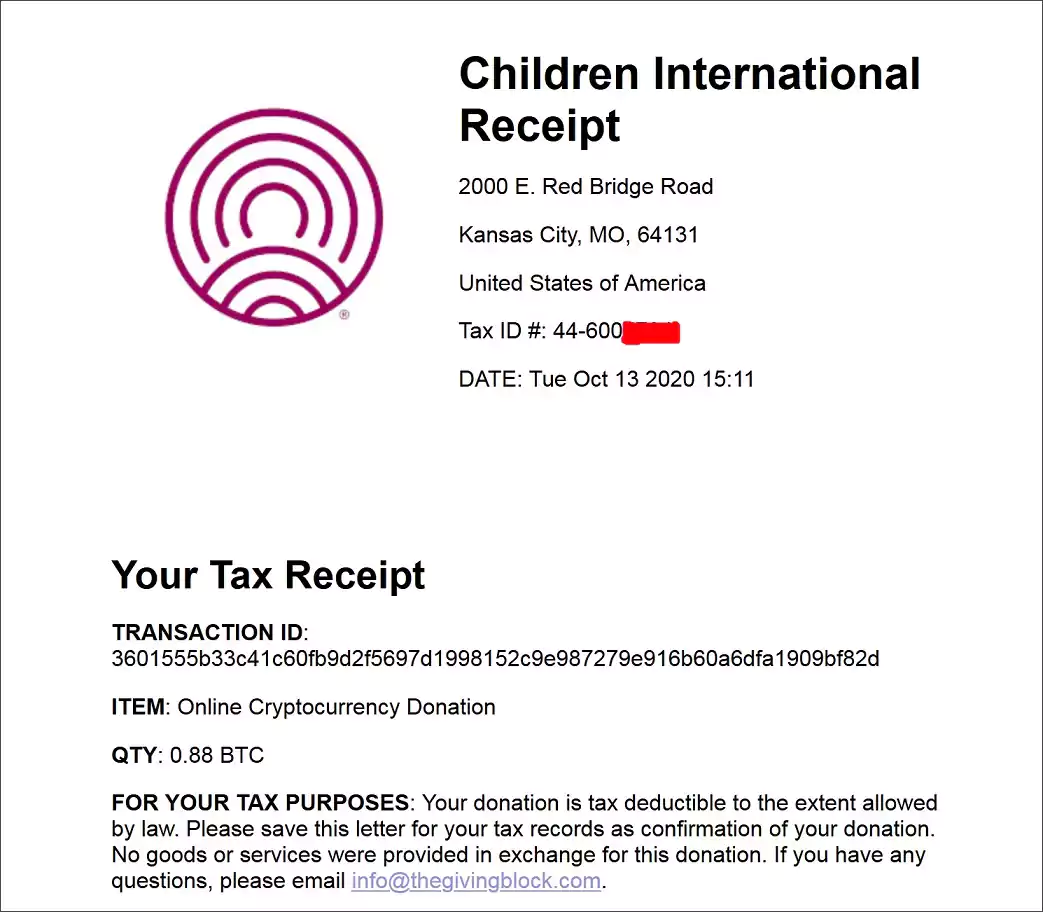
However, because they publicly announced the donation, the charities stated that they could not keep them.
“We are aware of the situation and are researching it internally. If the donation is linked to a hacker, we have no intention of keeping it,” Children International told BleepingComputer in a statement at the time.
In November 2020, they issued another press release stating they were creating a “sustainable” data leak storage system hosted on servers in Iran.
As Iran is on the US sanctions list, this caused ransomware negotiation firms, such as Coveware, to put DarkSide on their restricted list and no longer negotiate ransom payment for this operation.
“DarkSide’s own TOR site announces the intent to use infrastructure hosted within Iran, a sanctioned nexus. The purpose of this infrastructure is to store data stolen from victims of ransom attacks.”
“It is probable that a portion of the proceeds from any prospective ransom payment to DarkSide would be used to pay services providers within Iran. Accordingly, we have placed DarkSide on our restricted list,” Coveware CEO Bill Siegel told BleepingComputer.
DarkSide eventually had to walk back their claims of working with hosting service in Iran for fear of losing ransom payments.
Also Read: The DNC Singapore: Looking At 2 Sides Better
With Colonial Pipeline, DarkSide went too far and is now in the crosshairs of US law enforcement.
It would not be surprising if DarkSide releases the Colonial Pipeline decryption keys for free and does not leak the data for the pipeline as a gesture of goodwill.