KEEP IN TOUCH
Subscribe to our mailing list to get free tips on Data Protection and Cybersecurity updates weekly!







Researchers have developed a way to track a user across different browsers on the same machine by querying the installed applications on the device.
Certain applications, when installed, will create custom URL schemes that the browser can use to launch a URL in a specific application.
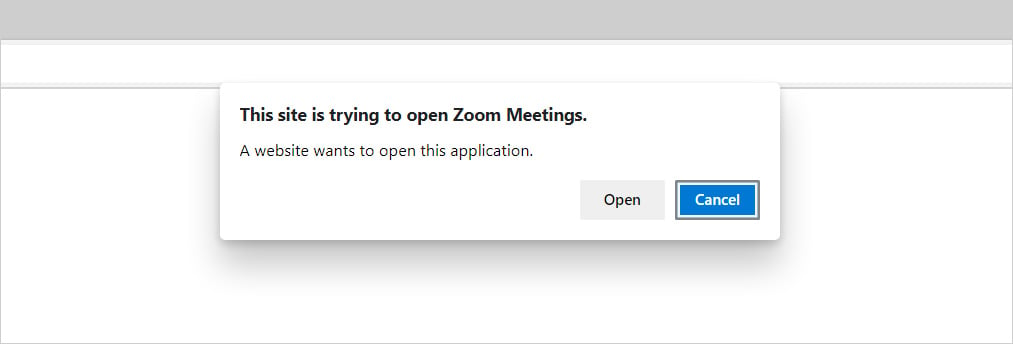
For example, the custom URL scheme for a Zoom web meeting is zoommtg://, which when opened, will prompt the browser to launch the Zoom client, as shown below.
Over a hundred different custom URL handlers configured by applications exist, including Slack, Skype, Windows 10, and even steam.
Also Read: Compliance Course Singapore: Spotlight On The 3 Offerings
A researcher from one of the most well-known fingerprinting scripts, FingerprintJS, has disclosed a vulnerability that allows a website to track a device’s user between different browsers, including Chrome, Firefox, Microsoft Edge, Safari, and even Tor.
“Cross-browser anonymity is something that even a privacy conscious internet user may take for granted. Tor Browser is known to offer the ultimate in privacy protection, though due to its slow connection speed and performance issues on some websites, users may rely on less anonymous browsers for their every day surfing,” explains a new vulnerability report by FingerprintJS’ Konstantin Darutkin.
“They may use Safari, Firefox or Chrome for some sites, and Tor for sites where they want to stay anonymous. A website exploiting the scheme flooding vulnerability could create a stable and unique identifier that can link those browsing identities together.”
To perform cross-browser tracking using scheme flooding, a website builds a profile of applications installed on a device by attempting to open their known URL handlers and checking if the browser launches a prompt.
If a prompt is launched to open the application, then it can be assumed that the specific app is installed. By checking for different URL handlers, a script can use the detected applications to build a unique profile for your device.
As the installed applications on a device are the same regardless of the browser you are using, this could allow a script to track a user’s browser usage on both Google Chrome and an anonymizing browser such as Tor.
To test this vulnerability, we visited Darutkin’s demo site at schemeflood.com with Microsoft Edge, where a script launches URL handlers for a variety of applications to determine if they are installed.
When completed, a unique identifier was shown on my profile that was also the same for tests using different browsers on my PC, including Firefox, Google Chrome, and Tor.
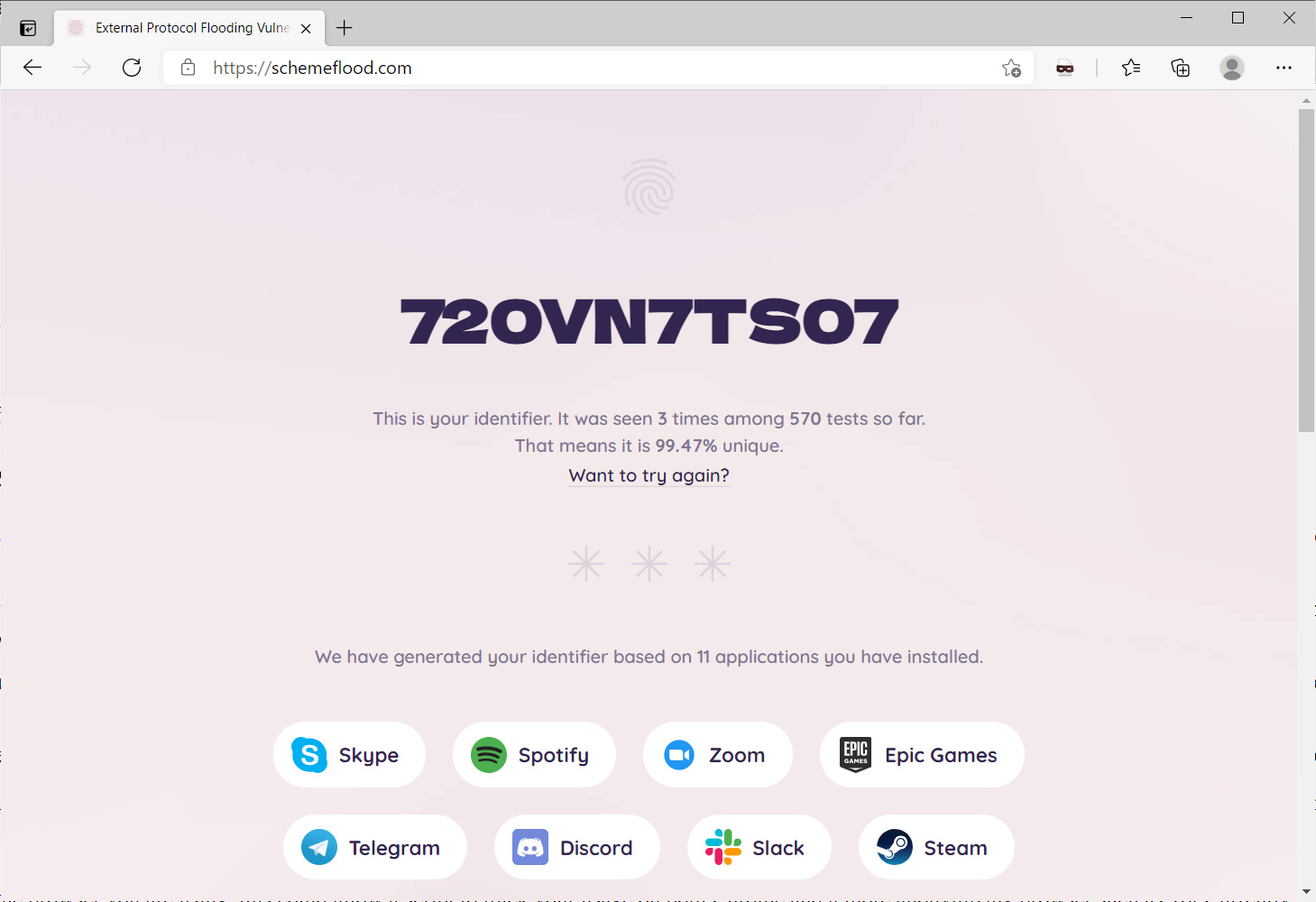
Darutkin’s scheme flooding vulnerability currently checks for the following twenty-four applications, Skype, Spotify, Zoom, vscode, Epic Games, Telegram, Discord, Slack, Steam, Battle.net, Xcode, NordVPN, Sketch, Teamviewer, Microsoft Word, WhatsApp, Postman, Adobe, Messenger, Figma, Hotspot Shield, ExpressVPN, Notion, and iTunes.
It is possible that multiple users can have the same combination of installed programs, leading to the same profile ID.
Of the four major browsers tested by Darutkin, only Google Chrome had previously added mitigations to prevent this type of attack by preventing multiple attempts to use URL handlers without a user gesture (interaction).
However, Darutkin discovered that triggering a built-in Chrome extension, such as the Chrome PDF Viewer, bypasses this mitigation.
“The built-in Chrome PDF Viewer is an extension, so every time your browser opens a PDF file it resets the scheme flood protection flag. Opening a PDF file before opening a custom URL makes the exploit functional,” explains Darutkin.
Also Read: Considering Enterprise Risk Management Certification Singapore? Here Are 7 Best Outcomes
Microsoft Edge Program Manager Eric Lawrence has acknowledged the attack, and Chromium and Microsoft engineers are working on a fix in a new bug report.
Until browsers add working mitigations for this attack, the only way to prevent this method of cross-browser tracking is to use a browser on a different device.