KEEP IN TOUCH
Subscribe to our mailing list to get free tips on Data Protection and Cybersecurity updates weekly!






The US Cybersecurity and Infrastructure Security Agency (CISA) has released the Ransomware Readiness Assessment (RRA), a new module for its Cyber Security Evaluation Tool (CSET).
RRA is a security audit self-assessment tool for organizations that want to understand better how well they are equipped to defend against and recover from ransomware attacks targeting their information technology (IT), operational technology (OT), or industrial control system (ICS) assets.
This CSET module was tailored RRA to assess varying levels of ransomware threat readiness to be helpful to all orgs regardless of their cybersecurity maturity.
“The RRA also provides a clear path for improvement and contains an evolving progression of questions tiered by the categories of basic, intermediate, and advanced,” CISA says on the tool’s wiki page.
“This is intended to help an organization improve by focusing on the basics first, and then progressing by implementing practices through the intermediate and advanced categories.
Also Read: The Difference Between GDPR and PDPA Under 10 Key Issues
CISA says the RRA can be used to defend against this growing threat as it effectively:
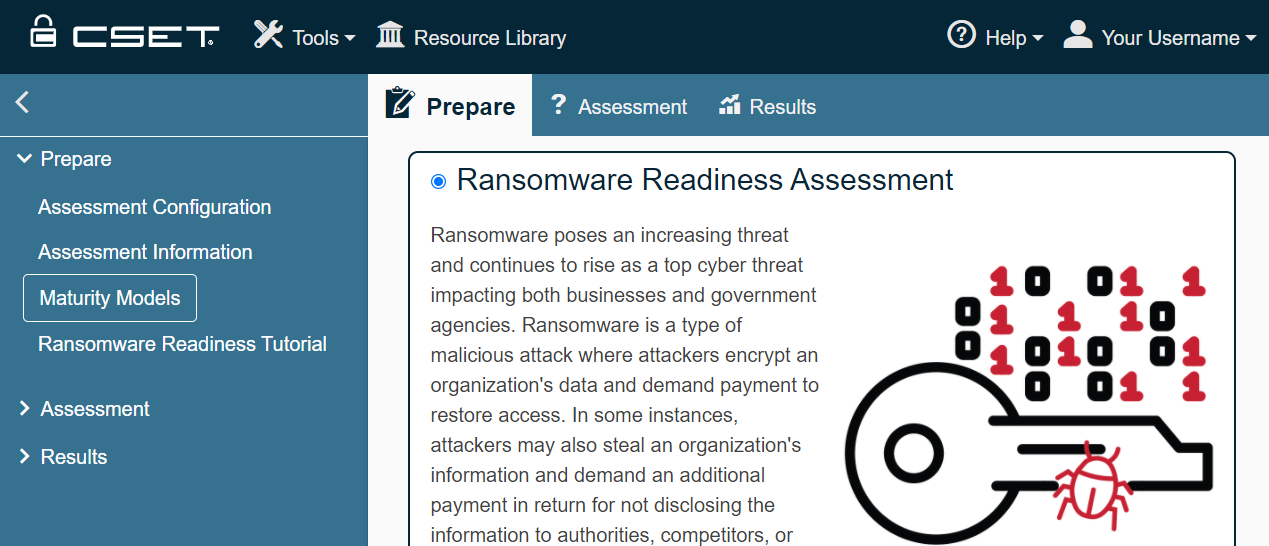
To use the self-assessment tool, you have to first install CSET and then:
CISA has previously released Aviary, a tool to review post-compromise activity in Microsoft Azure Active Directory (AD), Office 365 (O365), and Microsoft 365 (M365) environments.
Aviary works by analyzing data outputs generated using Sparrow, a PowerShell-based tool for detecting potentially compromised apps and accounts in Azure and Microsoft 365.
Also Read: PDPA Compliance Singapore: 10 Areas to Work On
CISA also released CHIRP (short for CISA Hunt and Incident Response Program), a Python-based forensics collection tool that detects signs of SolarWinds hackers’ activity on Windows systems.