KEEP IN TOUCH
Subscribe to our mailing list to get free tips on Data Protection and Cybersecurity updates weekly!






Emotet attacks have targeted multiple state and local governments in the U.S. as part of potentially targeted campaigns that have been ramping up since August, the Cybersecurity and Infrastructure Security Agency (CISA) said in an alert published today.
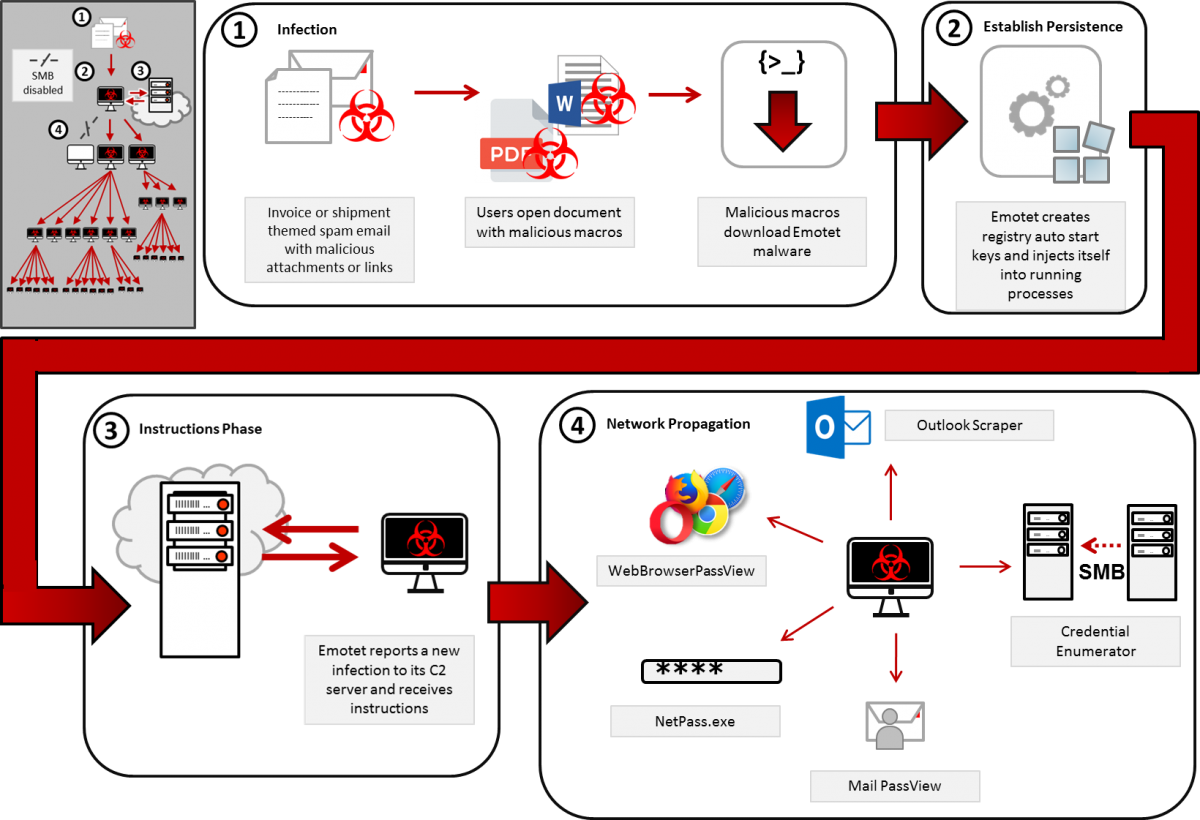
Emotet, a common banking Trojan when it was first spotted in 2014, in recent years has evolved into a botnet that the TA542 threat group (also tracked as Mummy Spider) uses to deliver second stage malware payloads on infected devices.
The malware is used to drop other malware families including the Trickbot (a known vector used to deploy both Ryuk and Conti ransomware) and the QakBot trojans.
Today’s alert is based on information collected by both CISA and the Multi-State Information Sharing & Analysis Center (MS-ISAC) since Emotet’s resurgence in July 2020.
During this time, “CISA observed Emotet being executed in phases during possible targeted campaigns,” the DHS agency explains.
Since August, the two organizations “have seen a significant increase in malicious cyber actors targeting state and local governments with Emotet phishing emails.”
“This increase has rendered Emotet one of the most prevalent ongoing threats,” CISA adds.
Since it came back online, Emotet has consistently ranked first in the list of top 10 malware strains uploaded and analyzed on the interactive malware analysis platform Any.Run.
In fact, Emotet overshadows the next malware in the top (the Njrat Remote Access Trojan), with almost ten times the number of samples submitted for analysis on the platform.
Also Read: Advisory Guidelines on Key Concepts in the PDPA: 23 Chapters
Starting with July 2020, CISA has observed increased Emotet activity, with the “EINSTEIN Intrusion Detection System, which protects federal, civilian executive branch networks” detecting around 16,000 related alerts.
“Since reemerging on July 17, Emotet has sustained its activities with daily spam runs spewing more than 500K emails every day (except weekends) starting at around 2:00 AM Pacific Time (UTC -7),” Microsoft said at the time.
After it was revived, Emotet began deploying the TrickBot trojan on infected Windows devices, later fully replacing the TrickBot payloads as it started to spread QakBot malware.
To secure networks and devices against Emotet attacks, CISA and MS-ISAC recommend admins and users to be cautious when opening suspicious attachments, to use antivirus software, and to block suspicious IPs addresses.
If you want updates and more info on active Emotet campaigns, you should follow the Cryptolaemus group on Twitter, a collective of security researchers who monitor the malware’s daily activity.
Also Read: How Singapore Cybersecurity Masterplan 2020 Is Formidable