KEEP IN TOUCH
Subscribe to our mailing list to get free tips on Data Protection and Cybersecurity updates weekly!







The Chaos Ransomware gang encrypts gamers’ Windows devices through fake Minecraft alt lists promoted on gaming forums.
Minecraft is a massively popular sandbox video game currently played by over 140 million people, and according to Nintendo sales numbers, it’s a top-seller title in Japan.
Also Read: Lessons from PDPC Incident and Undertaking: August 2021 Cases
According to researchers at FortiGuard, a recently discovered variant of the Chaos ransomware is being tentatively distributed in Japan, encrypting the files of Minecraft players and dropping ransom notes.
The lure used by the threat actors are ‘alt list’ text files that supposedly contain stolen Minecraft account credentials, but in reality, is Chaos ransomware executable.
Minecraft players who want to troll or grief other players without the risk of their accounts being banned will sometimes use ‘alt’ lists to find stolen accounts that they can use for bannable offenses.
Due to their popularity, alt lists are always in demand and are commonly shared for free or through automated account generators that supply the community with “spare” accounts.
.png)
When encrypting victims, the Chaos ransomware will append four random characters or digits as the extension to encrypted files.
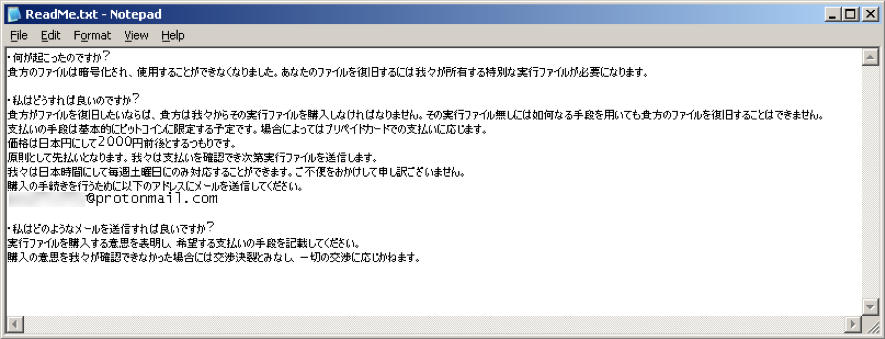
The ransomware will also drop a ransom note named ‘ReadMe.txt,’ where the threat actors demand 2,000 yen (~$17.56) in pre-paid cards.
Also Read: Data Minimization; Why Bigger is Not Always Better
This particular variant of the Chaos Ransomware is configured to search the infected systems for different file types smaller than 2ΜΒ and encrypts them.
However, if the file is larger than 2MB is will inject random bytes into the files, making them unrecoverable even if a ransom is paid.
Due to the destructive nature of the attack, those who pay the ransom can only recover smaller files.
The reason for this functionality is unclear, and it could be caused by poor coding, incorrect configuration, or to damage gamers’ files purposely.
In this particular campaign, the threat actors are promoting text files to create a false sense of security while swapping them out in the end with executables.
Users should be suspicious of and not execute any files they download from the Internet unless they trust the site and have scanned it with a tool like VirusTotal.