





Threat actors are using legitimate corporate contact forms to send phishing emails that threaten enterprise targets with lawsuits and attempt to infect them with the IcedID info-stealing malware.
IcedID is a modular banking trojan first spotted in 2017 and updated to also deploy second-stage malware payloads, including Trickbot, Qakbot, and Ryuk ransomware.
Its operators can use it to download additional modules after infecting a device, steal credentials and financial information, and move laterally across the victims’ networks to compromise more computers and deploy more payloads.
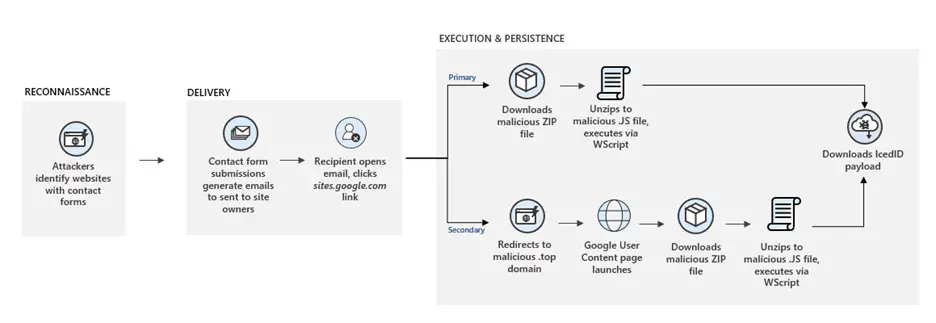
Recently detected by the Microsoft 365 Defender Threat Intelligence Team, this phishing campaign seems to have found a way to bypass contact forms’ CAPTCHA protection to flood enterprises with a barrage of phishing messages.
Microsoft threat intelligence analysts Emily Hacker and Justin Carroll observed “an influx of contact form emails targeted at enterprises by means of abusing companies’ contact forms.”
“This indicates that attackers may have used a tool that automates this process while circumventing CAPTCHA protections,” the Microsoft threat analysts said.
Using this phishing method, the attackers bypass the targeted enterprise’s secure email gateways, significantly increasing their phishing messages’ chance of landing in a target’s inbox instead of getting flagged and sent to the spam folder.
Also Read: 4 Best Practices On How To Use SkillsFuture Credit
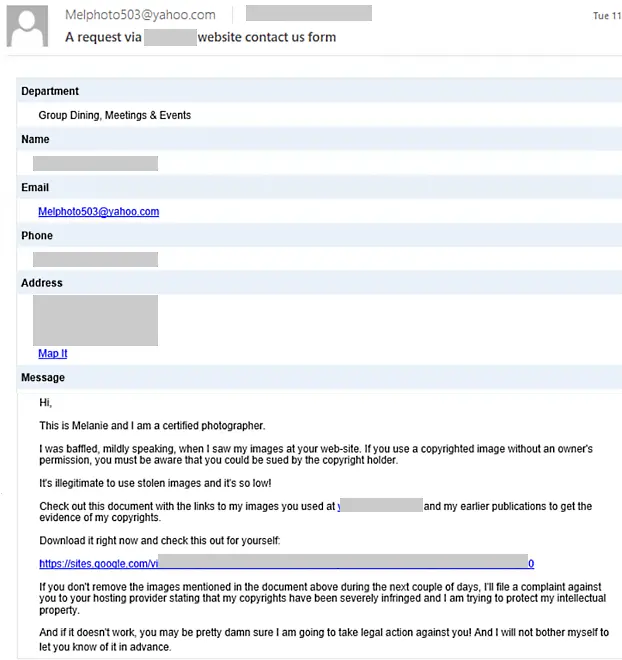
To further increase their attacks’ efficiency, the threat actors threaten their targets with legal action for copyright infringements to pressure them into clicking embedded links directing them to IcedID payloads.
The recipients are told to click on an embedded link to review the attackers’ “evidence” but are instead redirected to a Google Sites-hosted website used to deliver the IcedID malware.
The targets are then asked to log in using their Google accounts to see the content. After logging, an archive containing a heavily obfuscated .js-based downloader is downloaded on their computers.
An IcedID payload and a Cobalt Strike beacon are then downloaded on the compromised device using WScript and Powershell.
“While this specific campaign delivers the IcedID malware, the delivery method can be used to distribute a wide range of other malware, which can in turn introduce other threats to the enterprise,” the Microsoft analysts added.
“This threat shows attackers are always on the hunt for attack paths for infiltrating networks, and they often target services exposed to the internet. Organizations must ensure they have protections against such threats.”
Cisco Talos researchers discovered a similar campaign in September 2020 using legitimate contact forms to send phishing emails to distribute various malware payloads, including Gozi ISFB, ZLoader, SmokeLoader, and AveMaria.
Also Read: 3 Reasons Why You Must Take A PDPA Singapore Course
After the disruption of Emotet’s network in January, IcedID malicious activity has surged slowly, filling the gap left behind by Emotet, according to research from Awake Security and Uptycs.