





Newly discovered Android malware found on Google’s Play Store disguised as a Netflix tool is designed to auto-spread to other devices using WhatsApp auto-replies to incoming messages.
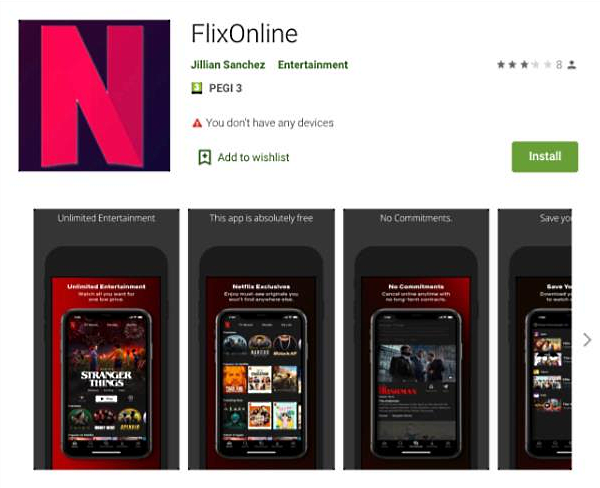
Researchers at Check Point Research (CPR) discovered this new malware disguised as an app named FlixOnline and trying to lure potential victims with promises of free access to Netflix content.
CPR researchers responsibly disclosed their research findings to Google who quickly took down and removed the malicious application from the Play Store.
The malicious FlixOnline app was downloaded roughly 500 times throughout the two months it was available for download on the store.
Once the app is installed on an Android device from the Google Play Store, the malware starts a service that requests overlay, battery optimization ignore, and notification permissions.
After the permissions are granted, the malware will be able to generate overlays over any app windows for credential theft purposes, block the device from shutting down its process to optimize energy consumption, gain access to app notifications, and manage or reply to messages.
It then starts monitoring for new WhatsApp notifications to auto-reply to all incoming messages using custom text payloads received from the command-and-control server and crafted by its operators.
Also Read: The Difference Between GDPR And PDPA Under 10 Key Issues
“The technique here is to hijack the connection to WhatsApp by capturing notifications, along with the ability to take predefined actions, like ‘dismiss’ or ‘reply’ via the Notification Manager,” said Aviran Hazum, Manager of Mobile Intelligence at Check Point.
“The fact that the malware was able to be disguised so easily and ultimately bypass Play Store’s protections raises some serious red flags.”
Check Point said that the automatic responses observed in this campaign redirected the victims to a fake Netflix site that tried to harvest their credentials and credit card information.
Using this malware, the attackers could perform various malicious activities, including:
This wormable Android malware “highlights that users should be wary of download links or attachments that they receive via WhatsApp or other messaging apps, even when they appear to come from trusted contacts or messaging groups,” Check Point concluded.
“Although CPR helped stop this one malware campaign, we suspect the malware family identified is here to stay, as it may return in different apps on the Play Store.”
Indicators of compromise (IOCs), including malware sample hashes and the C2 server address, are available at the end of Check Point’s report.
Also Read: PDPA Compliance Singapore: 10 Areas To Work On
Another Android malware disguised as a System Update discovered by Zimperium researchers on third-party Android app stores provided threat actors with spyware capabilities designed to automatically trigger whenever new info is ready for exfiltration.