



Three vulnerabilities found in the iSCSI subsystem of the Linux kernel could allow local attackers with basic user privileges to gain root privileges on unpatched Linux systems.
These security bugs can only be exploited locally, which means that potential attackers will have to gain access to vulnerable devices by exploiting another vulnerability or using an alternative attack vector.
GRIMM researchers discovered the bugs 15 years after they were introduced in 2006 during the initial development stages of the iSCSI kernel subsystem.
According to GRIMM security researcher Adam Nichols, the flaws affect all Linux distributions, but luckily, the vulnerable scsi_transport_iscsi kernel module is not loaded by default.
However, depending on the Linux distribution attackers might target, the module can be loaded and exploited for privilege escalation.
“The Linux kernel loads modules either because new hardware is detected or because a kernel function detects that a module is missing,” Nichols said.
“The latter implicit autoload case is more likely to be abused and is easily triggered by an attacker, enabling them to increase the attack surface of the kernel.”
Also Read: 3 Reasons Why You Must Take A PDPA Singapore Course
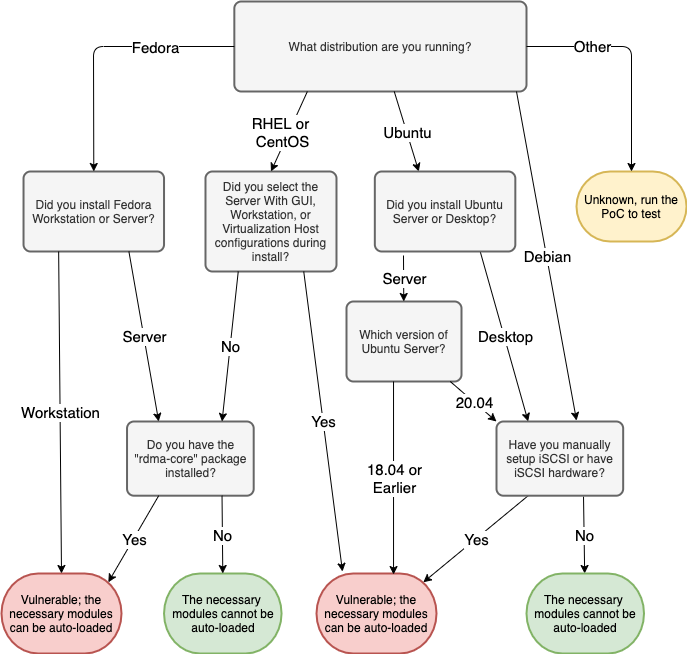
“On CentOS 8, RHEL 8, and Fedora systems, unprivileged users can automatically load the required modules if the rdma-core package is installed,” Nichols added.
“On Debian and Ubuntu systems, the rdma-core package will only automatically load the two required kernel modules if the RDMA hardware is available. As such, the vulnerability is much more limited in scope.”
Attackers can abuse the bugs to bypass exploit-blocking security features such as Kernel Address Space Layout Randomization (KASLR), Supervisor Mode Execution Protection (SMEP), Supervisor Mode Access Prevention (SMAP), and Kernel Page-Table Isolation (KPTI).
The three vulnerabilities can lead to local elevation of privileges, information leaks, and denials of service:
All three vulnerabilities are patched as of 5.11.4, 5.10.21, 5.4.103, 4.19.179, 4.14.224, 4.9.260, and 4.4.260, and patches became available in mainline Linux kernel on March 7th. No patches will be released for EOL unsupported kernels versions like 3.x and 2.6.23.
If you have already installed one of the Linux kernel versions, your device can’t be compromised in attacks exploiting these bugs.
Also Read: What You Should Know About The Data Protection Obligation Singapore
If you haven’t patched your system, you can use the above diagram to find if your device is vulnerable to exploitation attempts.