KEEP IN TOUCH
Subscribe to our mailing list to get free tips on Data Protection and Cybersecurity updates weekly!



Lorem ipsum dolor sit amet, consectetur adipiscing elit, sed do eiusmod tempor incididunt ut labore et dolore magna aliqua. Ut enim ad minim veniam, quis nostrud exercitation ullamco laboris nisi ut aliquip ex ea commodo consequat. Duis aute irure dolor in reprehenderit in voluptate velit esse cillum dolore eu fugiat nulla pariatur. Excepteur sint occaecat cupidatat non proident, sunt in culpa qui officia deserunt mollit anim id est laborum.

Lorem ipsum dolor sit amet, consectetur adipiscing elit, sed do eiusmod tempor incididunt ut labore et dolore magna aliqua. Ut enim ad minim veniam, quis nostrud exercitation ullamco laboris nisi ut aliquip ex ea commodo consequat. Duis aute irure dolor in reprehenderit in voluptate velit esse cillum dolore eu fugiat nulla pariatur. Excepteur sint occaecat cupidatat non proident, sunt in culpa qui officia deserunt mollit anim id est laborum.

Lorem ipsum dolor sit amet, consectetur adipiscing elit, sed do eiusmod tempor incididunt ut labore et dolore magna aliqua. Ut enim ad minim veniam, quis nostrud exercitation ullamco laboris nisi ut aliquip ex ea commodo consequat. Duis aute irure dolor in reprehenderit in voluptate velit esse cillum dolore eu fugiat nulla pariatur. Excepteur sint occaecat cupidatat non proident, sunt in culpa qui officia deserunt mollit anim id est laborum.

Annual VAPT is mandatory for all networks, mobile, and web apps that store personal data in data bases. We believe businesses shouldn't have to pay extra to stay compliant and avoid penalties. If you find a lower price with another licensed VAPT service provider, for the same scope of work or more, we'll beat their price by 20%. Terms & Conditions apply.

We're not only affordable, we're the best. All our VAPT clients have stayed safe from cyber threats. We're so sure of our services that we offer a 200% money back guarantee on top of the 10% price beat guarantee. We're the only company in Singapore that dares to offer this. If you suffer a data breach or hack after using our VAPT services, we'll refund you every cent you paid us. And as a form of apology, we'll give you extra 100% to work with someone else! If we can't keep you safe, we don't deserve your money. Terms & Conditions apply.


Certified Ethical Hacker (CEH)

Offensive Security Certified Professional (OSCP)

CREST Registered Penetration Tester (CRT)

CREST Certified Web Applications Tester (CCT App)

CREST Practitioner Security Analyst (CPSA)
CSRO License (Entity): Privacy Ninja Penetration Testing Service License No. CS/PTS/C-2022-0128


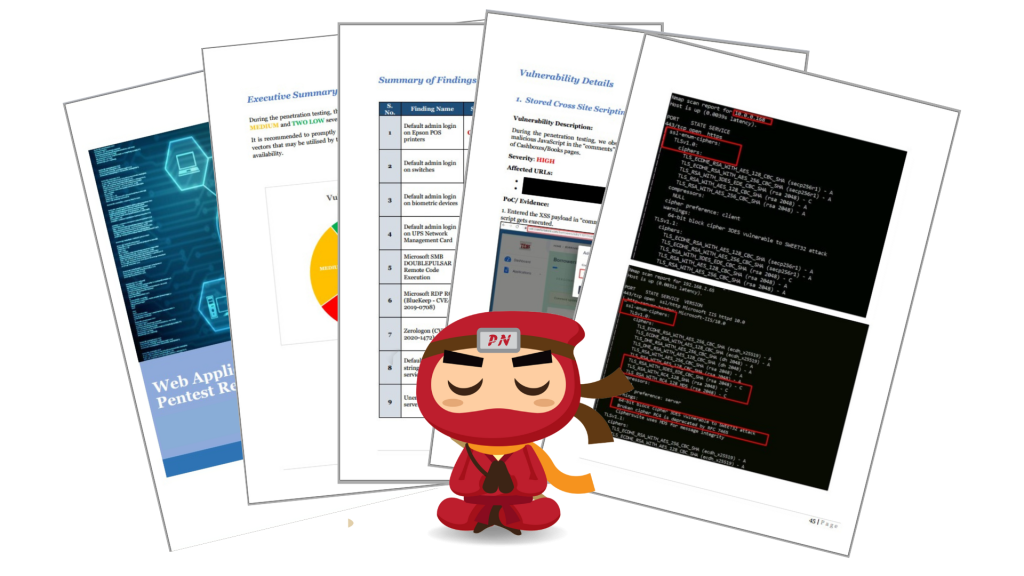
What we found after penetration testing:
SQL Injection – An attacker can access and dump the whole database containing critical data using malicious SQL commands in user input fields
Local File Inclusion (LFI) – An attacker can read sensitive files without any restriction by fooling the target system, gaining access to sensitive information, such as password files
Stored Cross-Site Scripting (XSS) – An authenticated user can embed malicious JavaScript code in a page, which will be executed whenever any user accesses that page.
Malicious File Upload – An attacker can upload malicious executable files containing malicious content, like shell.php, to a computer system without any restriction, which might lead to remote code execution (RCE) attacks
Broken Authorisation – An authenticated user can deactivate and delete job alerts of other users without any restriction.
Link Injection – Any authenticated user can embed malicious HTML tags such as hyperlink <a> tag in a page, which may redirect users to a malicious website controlled by the attacker.
And many more
What we found after our penetration test:
Stored Cross-Site Scripting (XSS) – An authenticated user can embed malicious JavaScript code in a page, which will be executed whenever any user accesses that page.
Malicious File Upload – An attacker can upload malicious executable files containing malicious content to a computer system without any restriction, which might lead to other cyber-attacks such as insecure redirection, user account takeover, etc.
Host Header Injection – An attacker can redirect the users to a malicious web application controlled by the attacker and carry out various attacks such as session hijacking, malware download, etc.
HTML Injection – Any authenticated user can embed malicious HTML tags such as hyperlink <a> tag in a page, which may redirect users to a malicious website controlled by the attacker.
And many more

What we found after our penetration test:
Fake user account creation with invalid mobile numbers – An attacker can create unlimited bogus/fake user accounts using automated scripts, causing the backend database to be overloaded with fake user accounts.
Firebase database publicly exposed – An attacker can gain sensitive information about a user, such as an email id, username and token.
Lack of binary protection – An attacker can use an automated tool to reverse engineer the code and modify it using malware to perform some hidden functionality.
Application signed with a debug certificate – An attacker can debug the application activities/communication and perform a Man-in-the-Middle attack.
SQL Injection – An attacker can supply SQL payloads in the user input field and dump the whole database containing all user’s sensitive data.
And many more
What we found after our penetration test:
Sensitive Information Disclosure – An attacker can gain remote access to user credentials or mobile application data without restriction and use them for authentication bypass or social engineering attacks.
Business Logical Flaw – A user can create a wallet with wrong collection settings, which could lead to flaws in business logic while funding transactions.
Lack of binary protection – An attacker can use an automated tool to reverse engineer the code and modify it using malware to perform some hidden functionality.
Misconfiguration in Manifest/plist – An attacker can conduct a Man-in-the-Middle attack since application traffic is transmitted in clear text format.
Insecure Data Storage – An attacker can use the information stored in the app folder for further attacks, which may lead to user account takeover.
And many more
What we found after our penetration test:
Default admin login on routers and VoIPs – An attacker can steal sensitive data by sniffing the traffic going through the routers/VoIPs and can implant its own exploit to compromise all other systems in the internal network.
Default admin login on biometric devices – An attacker can add, modify, and delete user accounts and related details from biometric devices without anyone’s knowledge.
Microsoft SMB EternalBlue Remote Code Execution – An attacker can take complete control over the server with SYSTEM security privileges and steal sensitive data or credentials of other logged-in users.
Malicious File Upload – An attacker can upload malicious executable files on the web server, which can get executed at the back end whenever a user accesses or views that particular file
XMLRPC DOS Attack – An attacker can access the xmlrpc.php file without any authentication and conduct a DOS attack against the web server
Synology DiskStation Manager (Multiple Possible Vulnerabilities) – An input validation error exists in the ‘externaldevices.cgi’ script that allows any administrative user to execute arbitrary commands with root privileges on the remote host.
Unsupported Windows OS – An attacker can conduct numerous exploits against outdated IIS servers such as RCE, DoS, Buffer Overflow, Command Injection, etc.
And many more
What we found after our penetration test:
Default admin login on POS printers – An attacker can add, modify and delete the printer’s configuration without authorisation.
Default admin login on switches – An attacker can steal sensitive data by sniffing the traffic going through the switches or can implant its own exploit to compromise all other systems present in the internal network.
Default admin login on biometric devices – An attacker can add, modify, and delete user accounts and related details from biometric devices without anyone’s knowledge.
Default admin login on UPS Network Management Card – An attacker can control NMC devices and attack other systems by changing the NMC configuration without restriction.
Microsoft SMB DOUBLEPULSAR Remote Code Execution – An attacker can take complete control over the server with SYSTEM security privileges and steal sensitive data or credentials of other logged-in users.
Microsoft RDP RCE (BlueKeep – CVE- 2019-0708) – An attacker can take complete control over the server through RDP service and run arbitrary commands with administrator privileges
Zerologon (CVE- 2020-1472) – An attacker can set an empty password for a domain user account and retrieve password hashes of all existing domain users.
Default community strings for SNMP service – An attacker can retrieve and modify sensitive information related to the device, such as device firmware version, routing tables, network interfaces, and configuration details.
Unencrypted Telnet server – An attacker can eavesdrop on a Telnet session and obtain user credentials via a MiTM attack.
Outdated Apache Server – An attacker can conduct numerous exploits against outdated Apache servers such as RCE, DoS, Buffer Overflow, Command Injection, etc.
Outdated VMware ESXI patches – An attacker with local administrative privileges on a virtual machine may exploit this issue to execute code as the virtual machine’s VMX process runs on the host.
Unsupported IIS version – An attacker can conduct numerous exploits against outdated IIS servers such as RCE, DoS, Buffer Overflow, Command Injection, etc.
And many more






Established in 2018, Privacy Ninja is a Singapore-based IT security company specialising in data protection and cybersecurity solutions for businesses. We offer services like vulnerability assessments, penetration testing, and outsourced Data Protection Officer support, helping organisations comply with regulations and safeguard their data.
Singapore
7 Temasek Boulevard,
#12-07, Suntec Tower One,
Singapore 038987
Latest resources sent to your inbox weekly
© 2025 Privacy Ninja. All rights reserved
Subscribe to our mailing list to get free tips on Data Protection and Cybersecurity updates weekly!

Subscribe to our mailing list to get free tips on Data Protection and Cybersecurity updates weekly!
