KEEP IN TOUCH
Subscribe to our mailing list to get free tips on Data Protection and Cybersecurity updates weekly!





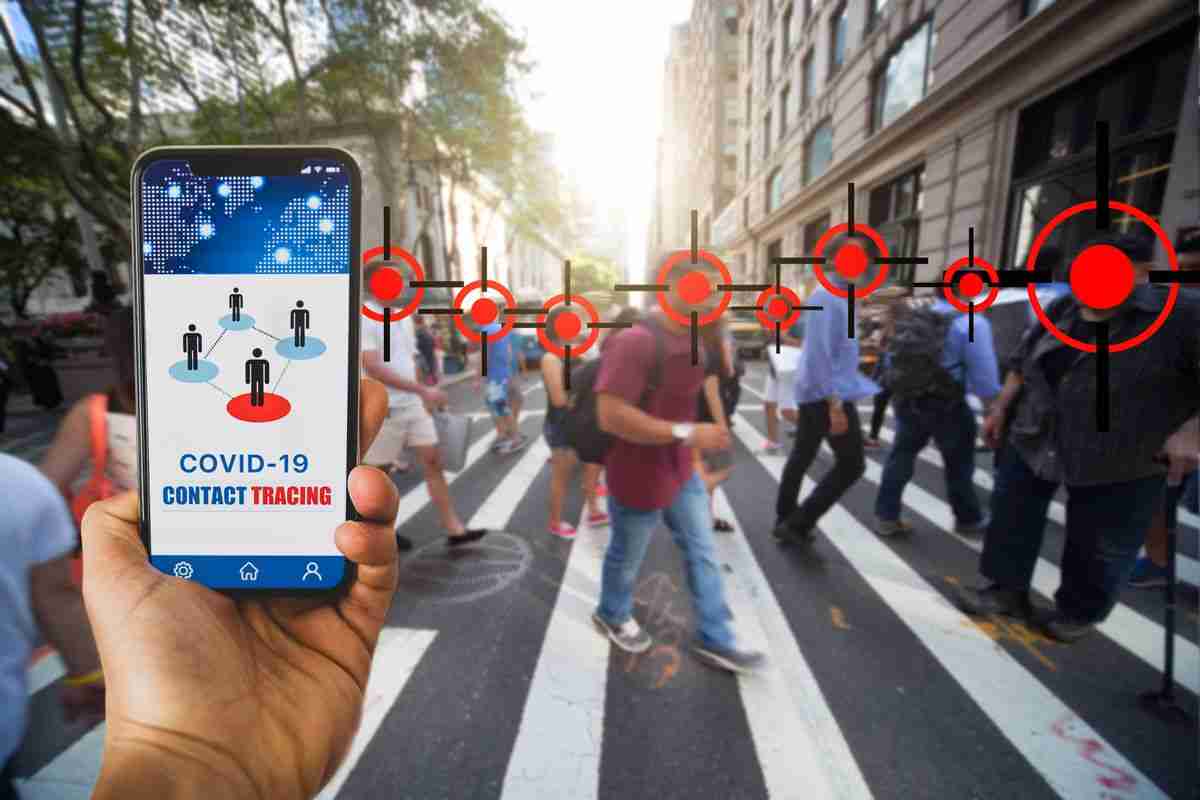
The malware surfaced just days after health officials in Canada announced the launch of a tracing app in the fight against COVID-19.
A new strain of ransomware is being deployed in attacks created off the back of the release of contact-tracing apps during the novel coronavirus pandemic.
Researchers from ESET said this week that the ransomware emerged only a few days after Health Canada announced the release of COVID Alert, which will first be tested in Ontario before rolling out nationwide.
While the official app is not due to be made available to mobile device users until next month at the earliest, cyberattackers are trying to capitalize on the government’s announcement with an Android package of their own — marketed as Canada’s official COVID-19 tracing app, but hiding a malicious secret.
According to the cybersecurity firm, two websites offered what appeared to be Health Canada’s tracing app. However, the now-defunct domains — tracershield[.]ca and covid19tracer[.]ca — were actually hosting APKs that, when downloaded, installed the CryCryptor ransomware on Android devices.
The ransomware first came to ESET’s attention by way of a tweet by a Twitter user under the handle @ReBensk. While the alert warned that the APKs were hiding a banking Trojan, upon further examination, the malware turned out to be the new ransomware.
See also: New WastedLocker ransomware demands payments of millions of USD
If an Android user downloads the APK from the fraudulent domains and installs the app, the malware requests access to files and begins the task of encrypting content on the device with specific extensions, including .PNG.
.ENC is appended to compromised files, which are encrypted using AES and a 16-character key. A text file making a ransom demand is also left in each directory where encrypted files are stored.
ESET has been able to create a decryption tool for the current version of the Android malware which has been made available on GitHub.
Also read: 9 Policies For Security Procedures Examples
It was possible to do so as the ransomware takes advantage of a bug categorized as “Improper Export of Android Components” (CWE-926) by MITRE. This issue allows installs apps to launch exported services, but in turn, this meant that a tool could be created that launches CryCryptor’s own decryption functions.
CNET: Republicans push bill requiring tech companies to help access encrypted data
Furthermore, the ransomware was traced back to GitHub after its source code was made public on 11 June. According to ESET, the developer — who named the open source malware CryDroid — disguised the release as a research project.
“We dismiss the claim that the project has research purposes — no responsible researcher would publicly release a tool that is easy to misuse for malicious purposes,” ESET says.
TechRepublic: Only 31% of Americans concerned with data security, despite 400% rise in cyberattacks
As the team was not convinced, GitHub has been made aware of the code’s true nature.
Earlier this month, researchers said a new ransomware variant that appeared on the scene in May is being exclusively used in attacks against US companies. Thought to be the work of Evil Corp, the WastedLocker ransomware typically demands ransom payments reaching millions of dollars.
Also read: 7 Phases Of Data Life Cycle Every Business Must Be Informed