KEEP IN TOUCH
Subscribe to our mailing list to get free tips on Data Protection and Cybersecurity updates weekly!







Microsoft took control of domains used by cybercriminals as part of the infrastructure needed to launch phishing attacks designed to exploit vulnerabilities and public fear resulting from the COVID-19 pandemic.
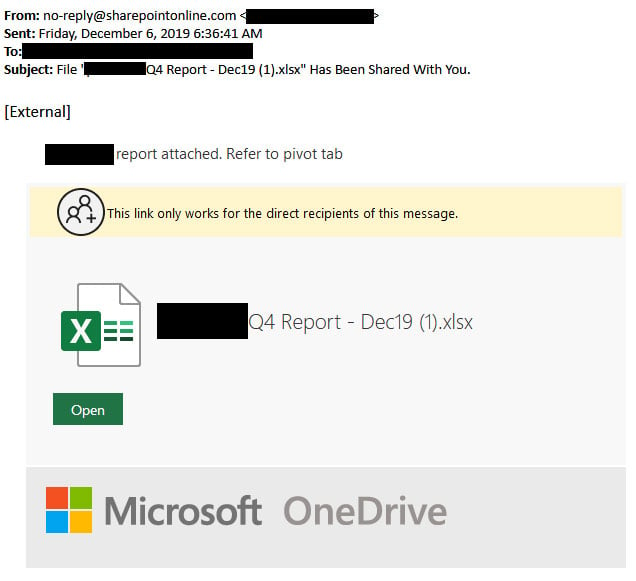
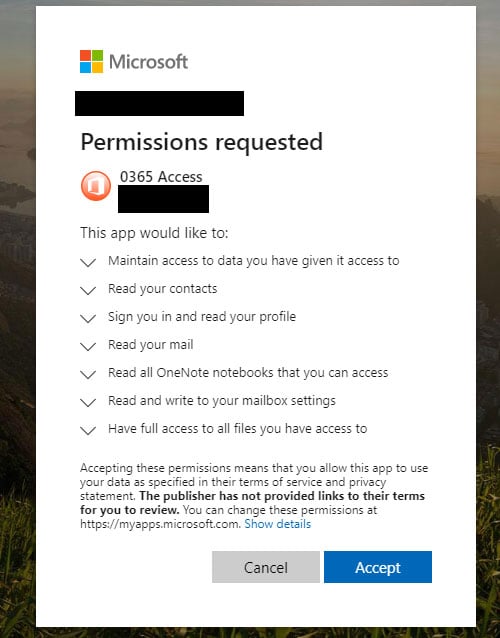
The threat actors who controlled these domains were first spotted by Microsoft’s Digital Crimes Unit (DCU) while attempting to compromise Microsoft customer accounts in December 2019 using phishing emails designed to help harvest contact lists, sensitive documents, and other sensitive information, later to be used as part of Business Email Compromise (BEC) attacks.
The attackers baited their victims (more recently using COVID-19-related lures) into giving them permission to access and control their Office 365 account by granting access permissions to attacker-controlled malicious OAuth apps.
BleepingComputer reported on the inner-workings of such an attack in December 2019, showing how this tactic allowed attackers to hijack their victims’ Office 365 accounts.
“Today, the U.S. District Court for the Eastern District of Virginia unsealed documents detailing Microsoft’s work to disrupt cybercriminals that were taking advantage of the COVID-19 pandemic in an attempt to defraud customers in 62 countries around the world,” Microsoft Corporate Vice President for Customer Security & Trust Tom Burt said.
“Our civil case has resulted in a court order allowing Microsoft to seize control of key domains in the criminals’ infrastructure so that it can no longer be used to execute cyberattacks.”
The domains used to host malicious web apps and seized by Microsoft are officeinvetorys[.]com, officehnoc[.]com, officesuited[.]com, officemtr[.]com, officesuitesoft[.]com, and mailitdaemon[.]com.
Also read: Top 25 Data Protection Statistics That You Must Be Informed
In early-April, the company said that the actual volume of malicious attacks did not increase since the start of the pandemic but, instead, malicious actors repurposed the infrastructure used in previous attacks to launch rethemed campaigns exploiting fears surrounding the COVID-19 pandemic.
“Attackers don’t suddenly have more resources they’re diverting towards tricking users; instead, they’re pivoting their existing infrastructure, like ransomware, phishing, and other malware delivery tools, to include COVID-19 keywords that get us to click,” Microsoft 365 Security Corporate Vice President Rob Lefferts said at the time.
Until April, around 60,000 attacks out of millions of targeted messages were using pandemic-related URLs or malicious attachments based on data collected by Microsoft from thousands of weekly email phishing campaigns. “In a single day, SmartScreen sees and processes more than 18,000 malicious COVID-19-themed URLs and IP addresses.”
Despite that, Lefferts said that represented less than two percent of the total volume of threats actively tracked by Microsoft on a daily basis.
Redmond also spotted nation-state actors using COVID-19 lures in campaigns targeting healthcare entities, with the company alerting dozens of hospitals about exposed VPN devices and gateways on their networks to defend against such attacks.
“In cases where criminals suddenly and massively scale their activity and move quickly to adapt their techniques to evade Microsoft’s built-in defensive mechanisms, additional measures such as the legal action filed in this case are necessary,” Burt added.
“This unique civil case against COVID-19-themed BEC attacks has allowed us to proactively disable key domains that are part of the criminals’ malicious infrastructure, which is a critical step in protecting our customers.”
In early-March, Microsoft also coordinated the takedown of the infrastructure used by the Necurs botnet (the largest spam botnet at the time) in campaigns distributing and infecting millions of computers with malware payloads.
A single Necurs-infected device was observed by Microsoft’s researchers sending around 3.8 million spam messages to more than 40.6 million targets withing just 58 days.
Update: Added the list of seized domains.
Also read: How Being Data Protection Trained Can Help With Job Retention