KEEP IN TOUCH
Subscribe to our mailing list to get free tips on Data Protection and Cybersecurity updates weekly!







Taiwanese laptop maker Compal Electronics suffered a DoppelPaymer ransomware attack over the weekend, with the attackers demanding an almost $17 million ransom.
Compal is the second-largest original design manufacturer (ODM) of laptops globally, with well-known companies rebranding their devices or designs, including Apple, HP, Dell, Lenovo, and Acer.
Over the weekend, Taiwanese media reported that Compal suffered a cyberattack, but the laptop maker claimed it was just an “abnormality” in their office automation system.
Also Read: The Scope Of Singapore Privacy: How We Use It In A Right Way
“Lu Qingxiong said that the main reason was an abnormality in the office automation system. The company suspected of being invaded by hackers. It has urgently repaired most of it and is expected to return to normal today,”
“Lu Qingxiong emphasized that Compal is not being blackmailed by hackers, as is reported by the outside world, and everything is currently normal in production,” UDN reported.
Since then, BleepingComputer has confirmed that Compal suffered a DoppelPaymer ransomware attack after we obtained a ransom note used in the attack.
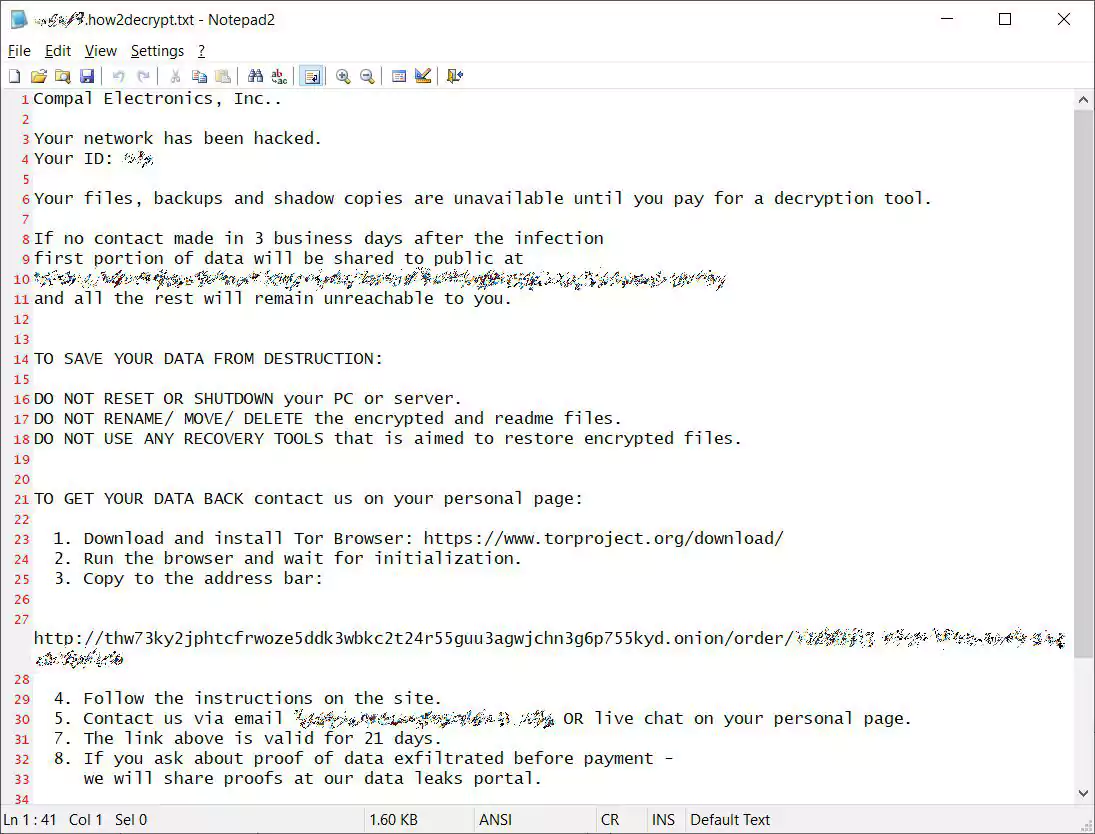
DoppelPaymer is a ransomware operation known for attacking enterprise targets by gaining access to admin credentials and using them to spread throughout a Windows network. Once they gain access to a Windows domain controller, they deploy the ransomware payloads to all devices on the network.
Also Read: How To Make A PDPC Complaint: With Its Importance And Impact
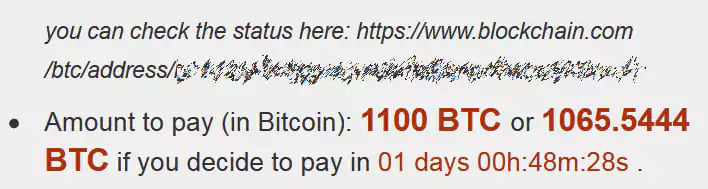
According to the DoppelPaymer Tor payment site linked to in the ransom note, the ransomware gang is demanding 1,100 Bitcoins, or $16,725,500.00 at today’s prices, to receive a decryptor.
According to the ransom note and DoppelPaymer’s past history, the attackers likely stole unencrypted data as part of their attack.
This stolen data is then used as a double-extortion strategy where the ransomware gangs threaten to release the files on data leak sites if a ransom is not paid.
It should be noted that the initial ransom demands are a “starting” price and are commonly negotiated to a significantly lower amount for victims who decide to pay the ransom.
Other victims attacked by DoppelPaymer in the past include PEMEX (Petróleos Mexicanos), the City of Torrance in California, Newcastle University, Hall County in Georgia, and Bretagne Télécom.