KEEP IN TOUCH
Subscribe to our mailing list to get free tips on Data Protection and Cybersecurity updates weekly!






The DontTouchTheGreenButton.com website just launched by the Trump campaign in relation to the recently filed Arizona “rejected votes” lawsuit was discovered to be leaking voter data.
The data included the voter name, address, and a unique identifier. However, reports have surfaced of users alleging the website has SQL Injection flaws that make it possible to collect a voter’s SSN and date of birth.
Over the weekend, President Trump’s re-election campaign and the Republican National Committee filed a lawsuit in Arizona alleging the polling officials in Maricopa County had incorrectly rejected in-person votes on Election Day, by misusing a mechanical feature (a green button) of the voting machines.
“Poll workers struggled to operate the new voting machines in Maricopa County, and improperly pressed and told voters to press a green button to override significant errors,” said Matt Morgan, Trump 2020 campaign general counsel.
“The result is that the voting machines disregarded votes cast by voters in person on Election Day in Maricopa County,” alleged Morgan.
To collect anecdotal evidence from voters who may have observed such behavior at the polling stations which validates what the lawsuit alleges, the campaign set up a website to collect sworn declarations from voters.
The website DontTouchTheGreenButton.com requests personal information from voters, such as their name and address, phone number, email address, date of birth, last 4 digits of social security number (SSN), and answers to multiple-choice questions.
Also Read: Website Ownership Laws: Your Rights And What These Protect
To limit the ability to submit declarations only to Maricopa County voters, the website lets users “search” for their name and auto-populate their address, as shown below:
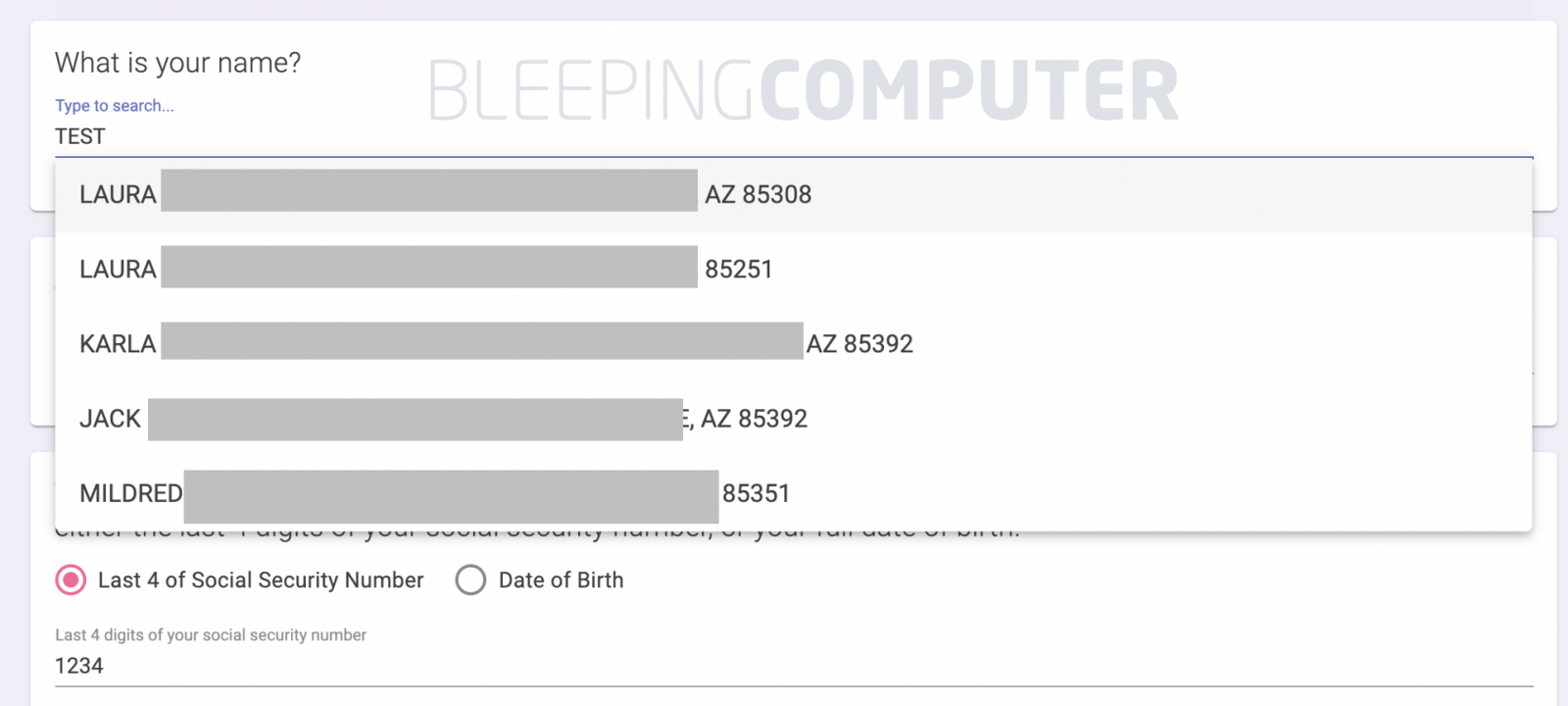
Given voter records are already public information, the ability for anyone to look up this information is hardly surprising—although an obvious privacy concern.
However, the website used an API that may make it possible to scrape voter information in bulk.
Provided the website was launched fairly quickly after the lawsuit was filed, some users are calling it “hastily set-up” and ridden with data leaks and SQL Injection flaws.
BleepingComputer observed the data was being pulled from the server using Algolia REST API.
The exposed API key and Application ID in the request could let anyone programmatically run queries to scrape the voter data in bulk from the service.
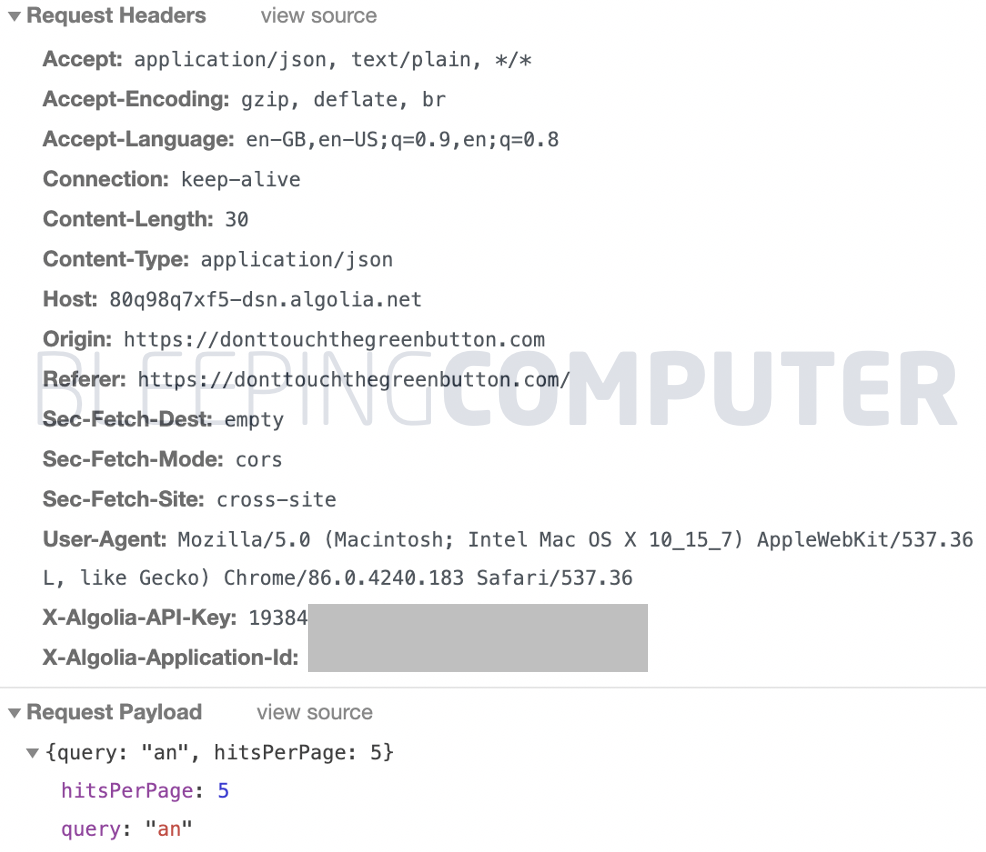
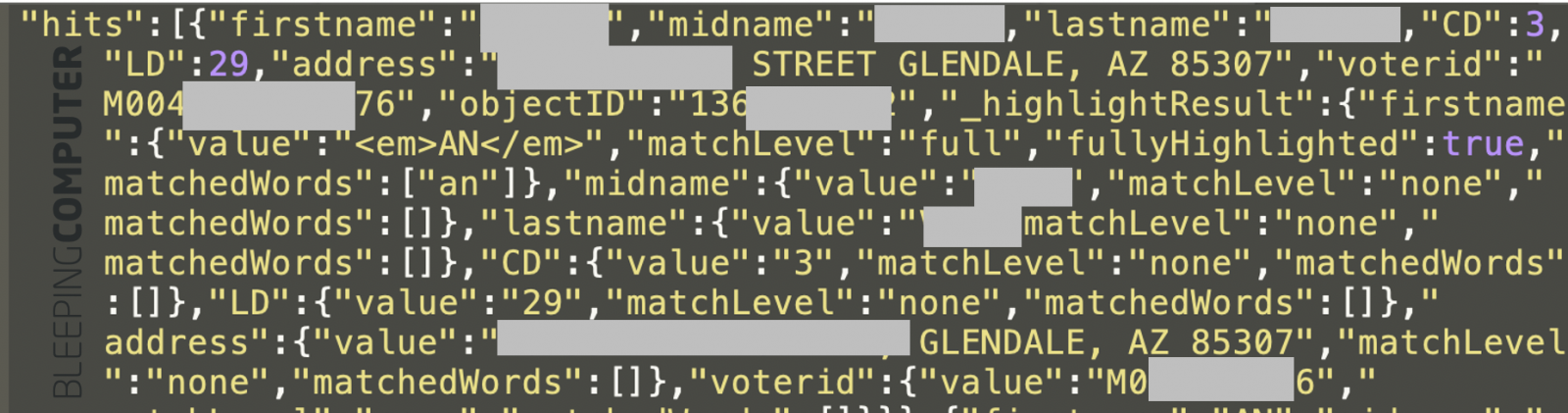
The JSON data returned by the REST API contains a list of 5 voter names and addresses by default, along with unique identifiers based on the search query (e.g. first few letters of the voter’s name).
In theory, one could make automated queries to download voter information by altering the hitsPerPage value shown above to a higher value, and do this repeatedly for different multi-letter combinations until they have crawled the entire data set.
Also Read: Computer Misuse Act Singapore: The Truth And Its Offenses
This API used to retrieve voter information has since been removed from the DontTouchTheGreenButton.com site.
On Reddit, some users further alleged that the website was matching the name and address submitted against the last 4 digits of SSN entered by the user and exposing the partial SSN.
Whereas, other users mentioned one could execute a SQL Injection attack against the website to obtain the SSN and Date of Birth information for voters.
BleepingComputer did not verify these additional allegations.
This event marks the second API leak incident this year concerning voter registration data.
Earlier this year, an API used by the Biden campaign’s Vote Joe app was found to be leaking voter data that should have remained confidential.
When launching a mission-critical website such as DontTouchTheGreenButton.com it may be a good idea to conduct a thorough security assessment to safeguard user data and privacy.
Update 12:55 PM EST: API removed from site.